3.2 Class Dictionary This class implements a dictionary using a hash table in which collisions are...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
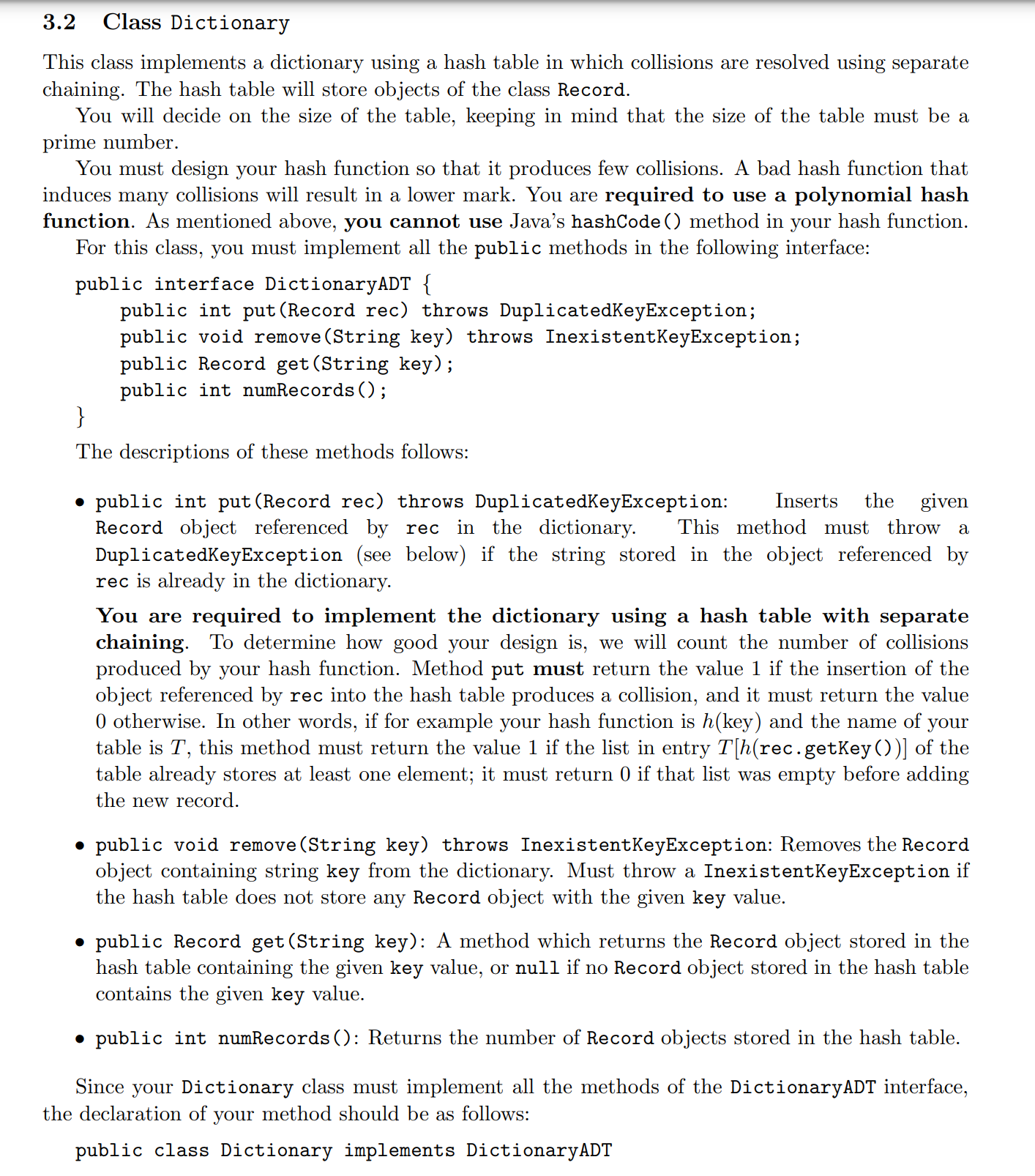
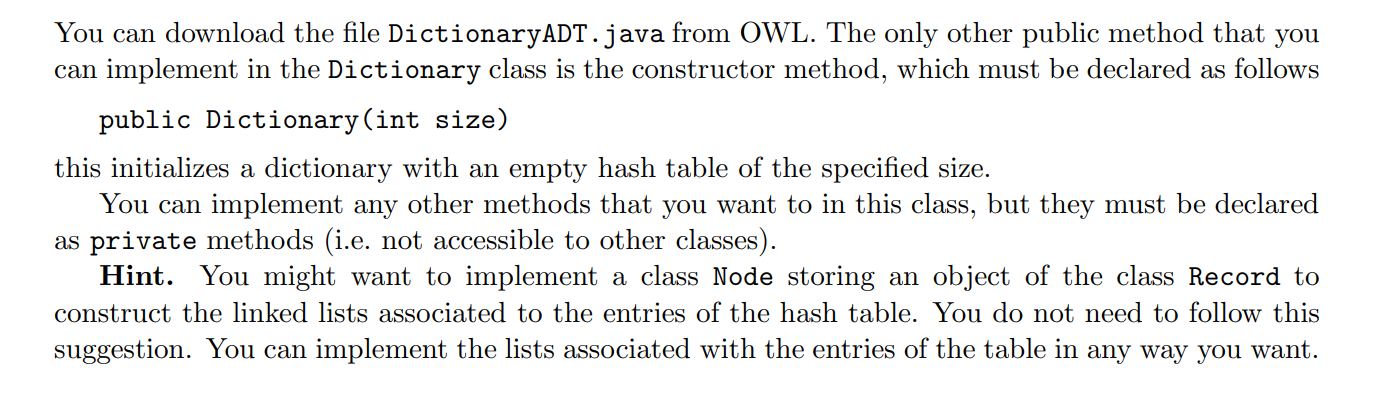
3.2 Class Dictionary This class implements a dictionary using a hash table in which collisions are resolved using separate chaining. The hash table will store objects of the class Record. You will decide on the size of the table, keeping in mind that the size of the table must be a prime number. You must design your hash function so that it produces few collisions. A bad hash function that induces many collisions will result in a lower mark. You are required to use a polynomial hash function. As mentioned above, you cannot use Java's hashCode () method in your hash function. For this class, you must implement all the public methods in the following interface: public interface DictionaryADT { public int put (Record rec) throws DuplicatedKeyException; public void remove (String key) throws InexistentKeyException; public Record get (String key); public int numRecords (); } The descriptions of these methods follows: Inserts the given This method must throw a public int put (Record rec) throws DuplicatedKeyException: Record object referenced by rec in the dictionary. DuplicatedKeyException (see below) if the string stored in the object referenced by rec is already in the dictionary. You are required to implement the dictionary using a hash table with separate chaining. To determine how good your design is, we will count the number of collisions produced by your hash function. Method put must return the value 1 if the insertion of the object referenced by rec into the hash table produces a collision, and it must return the value 0 otherwise. In other words, if for example your hash function is h(key) and the name of your table is T, this method must return the value 1 if the list in entry T[h(rec.getKey())] of the table already stores at least one element; it must return 0 if that list was empty before adding the new record. public void remove (String key) throws InexistentKeyException: Removes the Record object containing string key from the dictionary. Must throw a InexistentKeyException if the hash table does not store any Record object with the given key value. public Record get(String key): A method which returns the Record object stored in the hash table containing the given key value, or null if no Record object stored in the hash table contains the given key value. public int numRecords (): Returns the number of Record objects stored in the hash table. Since your Dictionary class must implement all the methods of the DictionaryADT interface, the declaration of your method should be as follows: public class Dictionary implements Dictionary ADT You can download the file DictionaryADT.java from OWL. The only other public method that you can implement in the Dictionary class is the constructor method, which must be declared as follows public Dictionary (int size) this initializes a dictionary with an empty hash table of the specified size. You can implement any other methods that you want to in this class, but they must be declared as private methods (i.e. not accessible to other classes). Hint. You might want to implement a class Node storing an object of the class Record to construct the linked lists associated to the entries of the hash table. You do not need to follow this suggestion. You can implement the lists associated with the entries of the table in any way you want. 3.2 Class Dictionary This class implements a dictionary using a hash table in which collisions are resolved using separate chaining. The hash table will store objects of the class Record. You will decide on the size of the table, keeping in mind that the size of the table must be a prime number. You must design your hash function so that it produces few collisions. A bad hash function that induces many collisions will result in a lower mark. You are required to use a polynomial hash function. As mentioned above, you cannot use Java's hashCode () method in your hash function. For this class, you must implement all the public methods in the following interface: public interface DictionaryADT { public int put (Record rec) throws DuplicatedKeyException; public void remove (String key) throws InexistentKeyException; public Record get (String key); public int numRecords (); } The descriptions of these methods follows: Inserts the given This method must throw a public int put (Record rec) throws DuplicatedKeyException: Record object referenced by rec in the dictionary. DuplicatedKeyException (see below) if the string stored in the object referenced by rec is already in the dictionary. You are required to implement the dictionary using a hash table with separate chaining. To determine how good your design is, we will count the number of collisions produced by your hash function. Method put must return the value 1 if the insertion of the object referenced by rec into the hash table produces a collision, and it must return the value 0 otherwise. In other words, if for example your hash function is h(key) and the name of your table is T, this method must return the value 1 if the list in entry T[h(rec.getKey())] of the table already stores at least one element; it must return 0 if that list was empty before adding the new record. public void remove (String key) throws InexistentKeyException: Removes the Record object containing string key from the dictionary. Must throw a InexistentKeyException if the hash table does not store any Record object with the given key value. public Record get(String key): A method which returns the Record object stored in the hash table containing the given key value, or null if no Record object stored in the hash table contains the given key value. public int numRecords (): Returns the number of Record objects stored in the hash table. Since your Dictionary class must implement all the methods of the DictionaryADT interface, the declaration of your method should be as follows: public class Dictionary implements Dictionary ADT You can download the file DictionaryADT.java from OWL. The only other public method that you can implement in the Dictionary class is the constructor method, which must be declared as follows public Dictionary (int size) this initializes a dictionary with an empty hash table of the specified size. You can implement any other methods that you want to in this class, but they must be declared as private methods (i.e. not accessible to other classes). Hint. You might want to implement a class Node storing an object of the class Record to construct the linked lists associated to the entries of the hash table. You do not need to follow this suggestion. You can implement the lists associated with the entries of the table in any way you want.
Expert Answer:

Related Book For 

Data Structures and Algorithm Analysis in Java
ISBN: 978-0132576277
3rd edition
Authors: Mark A. Weiss
Posted Date:
Students also viewed these programming questions
-
Let A, B be sets. Define: (a) the Cartesian product (A B) (b) the set of relations R between A and B (c) the identity relation A on the set A [3 marks] Suppose S, T are relations between A and B, and...
-
Two wires carrying equal and opposite currents are twisted together in the construction of a circuit. Why does this technique reduce stray magnetic fields? Please explain for dummies.
-
A carbon atom, with a half-full outer shell of electrons-four in a shell that can hold eight-readily shares its electrons with other atoms and forms a vast number of molecules, many of which are the...
-
Graph each rational function. f(x) = x - 9 x + 3
-
On February 20, 2009, Cedar Valley Aviation, a wholly owned subsidiary of Aerial Services, Inc. (ASI), brought a Piper 522AS (Cheyenne II) in for maintenance to Des Moines Flying Service, Inc....
-
On January 1, 2008, Titania Inc. granted stock options to officers and key employees for the purchase of 20,000 shares of the companys $10 par common stock at $25 per share. The options were...
-
5.) A hoop of 6 kg and radius .15 m is rolling down a 40-degree incline with 5 m length, what acceleration does it travel down the incline? How long does it take to get down the incline?
-
Given the following code snippet, determine the Big O complexity. You may assume N has been declared and initialized, and the code compiles and executes with no errors. Give your answer in Big O...
-
(RiskReturn) An investor currently holds the following portfolio: 8,000 shares of Stock A, worth $18,000; Beta = 1.2 15,000 shares of Stock B, worth $50,000; Beta-1.81 25,000 shares of Stock C, worth...
-
Investment A is an equity (stock) investment in an American company. Returns on this Investment for the past 6 years are detailed in the table below, and Carlo expects the returns of the next 6 years...
-
Learning what constitutes ethical behavior in project management allows those new to the career to understand expectations from the start. Understanding that not all professionals are ethical,...
-
calculate the following KPIs for their investment funds: Annual Portfolio Return Portfolio Variance Portfolio Standard Deviation Sharpe Ratio Frugal Tim has $1.25M Invested (broken down seen below)...
-
What is the MIRR of a project that costs $725, generates free cash inflows of $233 at the end of each of the first 4 years and an outflow of 111 at the end of Year 5? The reinvestment rate is 7.6%....
-
In what ways is a monopolistically competitive market like competition? Firms all sell their goods at a single market-clearing price. There exist many firms in the market, and more firms can enter...
-
on 8 For the following set of lengths 130, 170, 160, 160, 150, 190 Third quartile is: et red d out of Select one: O a. 160 a question O b. 145 O c. 175 O d. 180
-
Suppose that binary heaps are represented using explicit links. Consider the problem of merging binary heap lhs with rhs. Assume both heaps are perfect binary trees, containing 2l 1 and 2r 1 nodes,...
-
Suppose we choose the element in the middle position of the array as the pivot. Does this make it unlikely that quicksort will require quadratic time?
-
Consider the following algorithm for sorting six numbers: Sort the first three numbers using Algorithm A. Sort the second three numbers using Algorithm B. Merge the two sorted groups using...
-
Powerhouse Ltd purchased machinery on 2 January 2019, at a cost of $800 000. The machinery is depreciated using the straightline method over a useful life of 8 years with a residual value of $80 000....
-
The purchases and sales of Big Flower Pty Ltd of one brand of lawn fertiliser for the year ended 31 December 2019 are contained in the schedule below. The selling price up to 30 June was $12 per unit...
-
In groups of four or five, consider the following information. On 1 July 2019, Stevenson Pty Ltd, a proprietary company with three shareholders, acquired some property by issuing 100 000 shares to...

Study smarter with the SolutionInn App