4. When using ftp, each character, ch, that is typed on the remote machine is copied...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
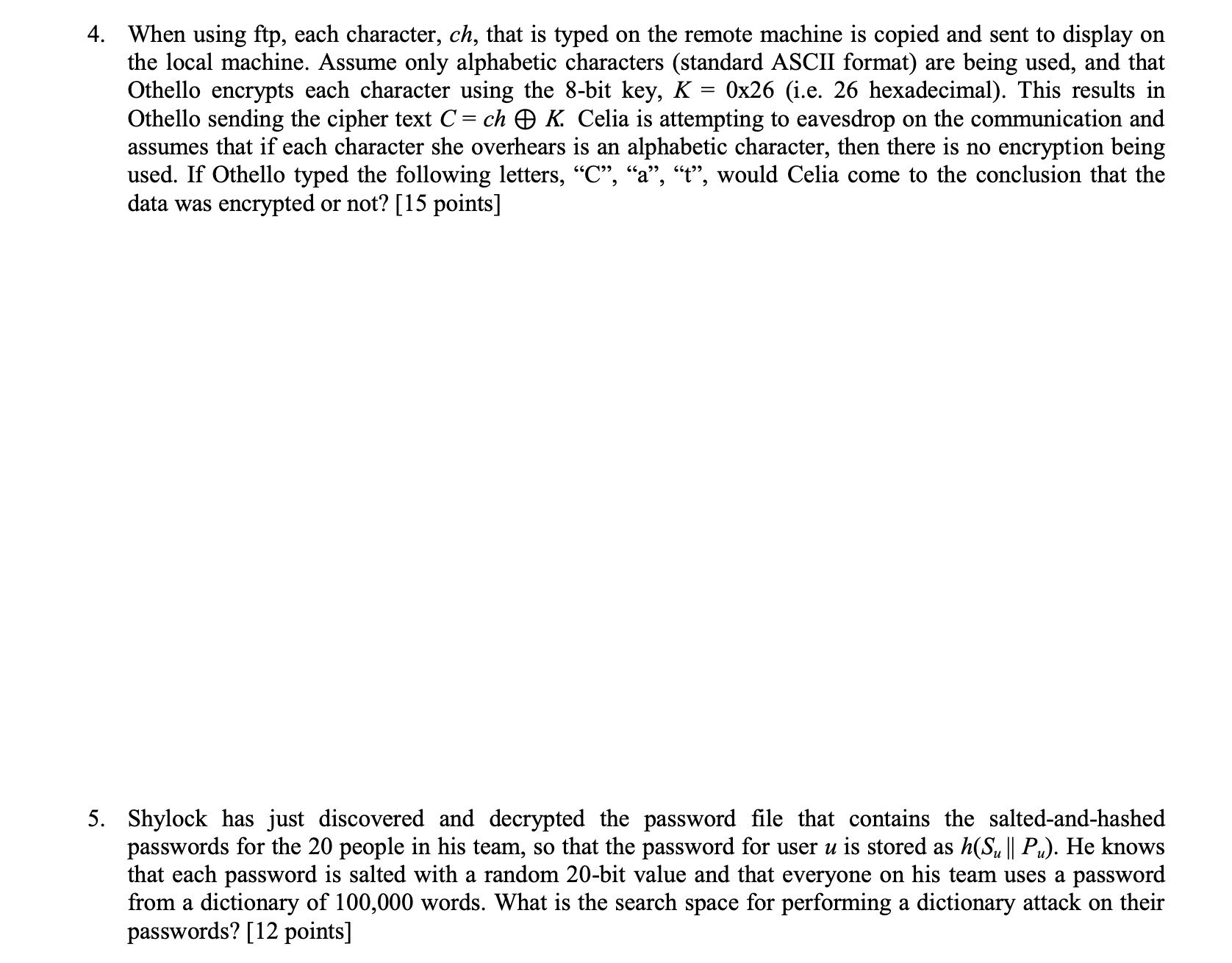
4. When using ftp, each character, ch, that is typed on the remote machine is copied and sent to display on the local machine. Assume only alphabetic characters (standard ASCII format) are being used, and that Othello encrypts each character using the 8-bit key, K = 0x26 (i.e. 26 hexadecimal). This results in Othello sending the cipher text C = ch K. Celia is attempting to eavesdrop on the communication and assumes that if each character she overhears is an alphabetic character, then there is no encryption being used. If Othello typed the following letters, "C", "a", "t", would Celia come to the conclusion that the data was encrypted or not? [15 points] 5. Shylock has just discovered and decrypted the password file that contains the salted-and-hashed passwords for the 20 people in his team, so that the password for user u is stored as h(Su || Pu). He knows that each password is salted with a random 20-bit value and that everyone on his team uses a password from a dictionary of 100,000 words. What is the search space for performing a dictionary attack on their passwords? [12 points] 4. When using ftp, each character, ch, that is typed on the remote machine is copied and sent to display on the local machine. Assume only alphabetic characters (standard ASCII format) are being used, and that Othello encrypts each character using the 8-bit key, K = 0x26 (i.e. 26 hexadecimal). This results in Othello sending the cipher text C = ch K. Celia is attempting to eavesdrop on the communication and assumes that if each character she overhears is an alphabetic character, then there is no encryption being used. If Othello typed the following letters, "C", "a", "t", would Celia come to the conclusion that the data was encrypted or not? [15 points] 5. Shylock has just discovered and decrypted the password file that contains the salted-and-hashed passwords for the 20 people in his team, so that the password for user u is stored as h(Su || Pu). He knows that each password is salted with a random 20-bit value and that everyone on his team uses a password from a dictionary of 100,000 words. What is the search space for performing a dictionary attack on their passwords? [12 points]
Expert Answer:
Answer rating: 100% (QA)
4 In the given scenario Othello encrypts each character using the 8bit key K 0x26 Celia is attemptin... View the full answer

Related Book For 

Accounting Information Systems
ISBN: 978-0133428537
13th edition
Authors: Marshall B. Romney, Paul J. Steinbart
Posted Date:
Students also viewed these programming questions
-
What is the probability that the program is implemented when p = 0 . 8 0 ?
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
Determine all the FIR filters which are specified by the lattice parameters K1 = , K2 = 0.6, K3 = -0.7, and K4 = 1/3
-
A bowling ball traveling with constant speed hits the pins at the end of a bowling lane 16.5 m long. The bowler hears the sound of the ball hitting the pins 2.50s after the ball is released from his...
-
Armando Corporation consists of two manufacturing divisions: Crater Division and Dollar Division. The Crater Division manufactures and transfers partially processed components to the Dollar Division...
-
For each of the following sets of numbers, calculate a \(95 \%\) confidence interval for the mean \((\sigma\) known); before going through the steps in calculating the confidence interval, the sample...
-
Jackson, Inc.s fiscal year ends December 31. Selected transactions for the period 20-1 through 20-8 involving bonds payable issued by Jackson are as follows: 20-1 Oct. 30 Issued $600,000 of 10-year,...
-
Lazaro currently makes $90,000 per year and goes skydiving 99 times per year. His income elasticity of demand for skydiving is, = 1.3. a. Explain in words what is meant by, = 1.3. b. What percentage...
-
Survey two relatives or friends and ask about their decision-making process when they most recently bought a vehicle. Find out if they thought about the opportunity costs when making the purchase....
-
The Race Track: Betting is closed. We have $1, 000 bet on horse A, $2, 000 on horse B, and $3, 000 on horse C. Compute the odds the track will post in order to take 10% no matter which horse wins. If...
-
Sugar and High Fructose Corn Syrup (HFCS) are: a. perfect substitutes b. perfect complements c. imperfect complements d. imperfect substitutes
-
In the wide open spaces of the American West, farms are likely to be: a. larger than in the Eastern US b. smaller than in the Eastern US c. the same size as in the Eastern US d. cannot determine from...
-
A point located inside the PPF is: a. efficient and attainable b. efficient but not attainable c. not efficient but attainable d. neither efficient nor attainable
-
The production possibilities frontier shows: a. all combinations of two inputs that can produce a constant level of output b. all combinations of two outputs that can be produced with a constant...
-
Labor-intensive agricultural production practices are most likely to occur in: a. Florida b. Kansas c. Texas d. Sub-Saharan Africa
-
A baker has purchased a machine to dispense chocolate chips in cookie dough. On average, the number of chips in a cookie is 5. Customers complain if there are not many chips in the cookie. What is...
-
Write a declaration for each of the following: a. A line that extends from point (60, 100) to point (30, 90) b. A rectangle that is 20 pixels wide, 100 pixels high, and has its upper-left corner at...
-
Refer to Problems 17.8 and 17.9 for information about the revenue and expenditure cycles for the Computer Warehouse and use that information to draw an integrated REA diagram for both cycles.
-
Managers at some companies face an ongoing systems development crisis: IS departments develop systems that businesses cannot or will not use. At the heart of the problem is a great divide that...
-
As an internal auditor for the state auditors office, you are assigned to review the implementation of a new computer system in the state welfare agency. The agency is installing an online computer...
-
True or False: Engineers seldom have an opportunity to influence the recovery period for expenditures.
-
True or False: Straight-line depreciation is the most popular depreciation method used in financial reporting.
-
A lumber company purchases and installs a wood chipper for \(\$ 200,000\). The chipper is classified as MACRS 7-year property. Its useful life is 10 years. The estimated salvage value at the end of...

Study smarter with the SolutionInn App


