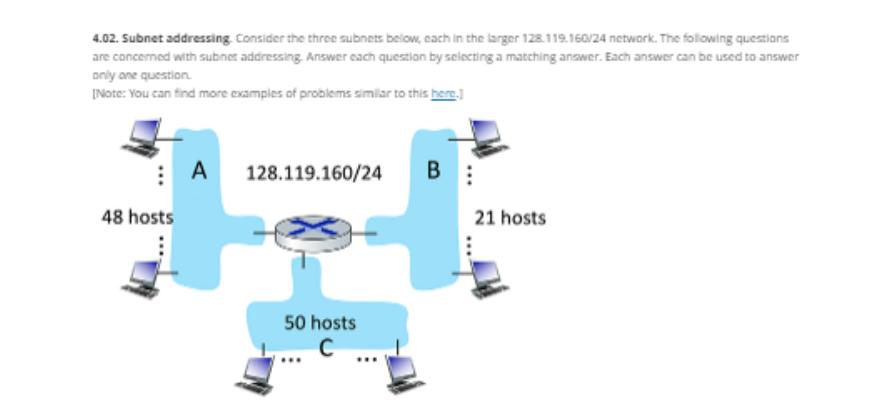
4.02. Subnet addressing. Consider the three subnets below, each in the larger 128.119.160/24 network. The following...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
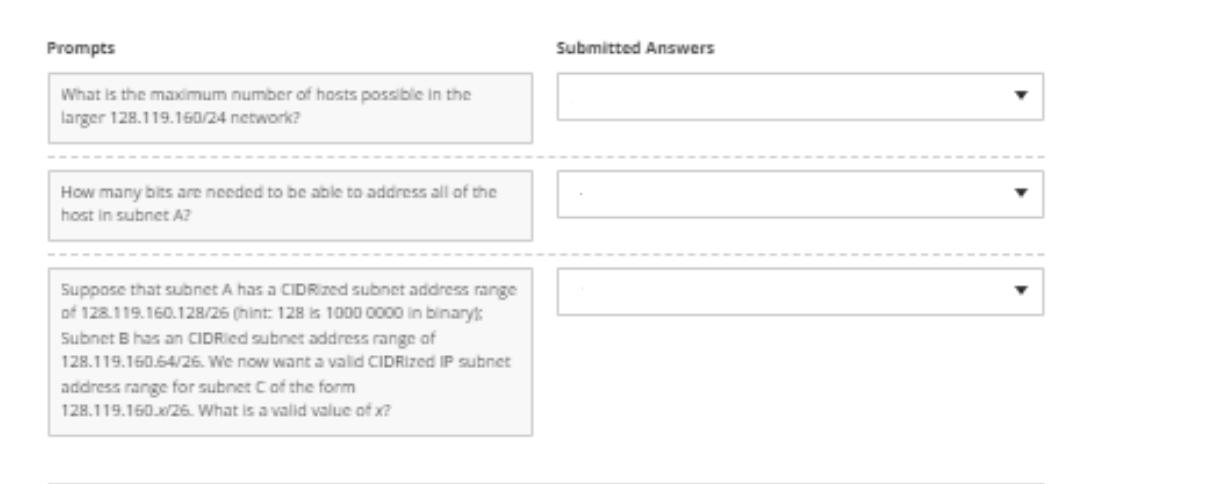
4.02. Subnet addressing. Consider the three subnets below, each in the larger 128.119.160/24 network. The following questions are concerned with subnet addressing. Answer each question by selecting a matching answer. Each answer can be used to answer only one question. [Note: You can find more examples of problems similar to this here.] 48 hosts A 128.119.160/24 50 hosts C B 21 hosts Prompts What is the maximum number of hosts possible in the larger 128.119.160/24 network? How many bits are needed to be able to address all of the host in subnet A? Suppose that subnet A has a CIDRized subnet address range of 128.119.160.128/26 (hint: 128 is 1000 0000 in binary: Subnet B has an CIDRied subnet address range of 128.119.160.64/26. We now want a valid CIDRized IP subnet address range for subnet C of the form 128.119.160.x/26. What is a valid value of x? Submitted Answers 4.02. Subnet addressing. Consider the three subnets below, each in the larger 128.119.160/24 network. The following questions are concerned with subnet addressing. Answer each question by selecting a matching answer. Each answer can be used to answer only one question. [Note: You can find more examples of problems similar to this here.] 48 hosts A 128.119.160/24 50 hosts C B 21 hosts Prompts What is the maximum number of hosts possible in the larger 128.119.160/24 network? How many bits are needed to be able to address all of the host in subnet A? Suppose that subnet A has a CIDRized subnet address range of 128.119.160.128/26 (hint: 128 is 1000 0000 in binary: Subnet B has an CIDRied subnet address range of 128.119.160.64/26. We now want a valid CIDRized IP subnet address range for subnet C of the form 128.119.160.x/26. What is a valid value of x? Submitted Answers
Expert Answer:
Answer rating: 100% (QA)
The images youve provided feature a networking problem focused on subnet addressing The first image shows three subnets A B and C labeled with the num... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these programming questions
-
A prospective borrower has an estimated monthly housing expense of$ 1 , 6 0 0 and his monthly obligations total $ 2 , 1 0 0 . If the borrower\'s monthly grossincome is $ 5 , 8 4 5 , what is the total...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
What is the effect of cultural commoditization and transformation on local traditions and customs? Give an example. Check Chapter 4 in the textbook for information on cultural commoditization and...
-
1. What responsibility does an organization have to ensure that its suppliers and business partners behave ethically? To whom is this responsibility owed? 2. How can an organization monitor the...
-
The stockholders' equity section of The Seventies Shop is presented here. THE SEVENTIES SHOP Balance Sheet (partial) ($ in thousands) Stockholders' equity: Preferred stock, $50 par...
-
An experiment was conducted to investigate the sheet flow rate of a land waste treatment plant. Classify each of the following independent variables as quantitative or qualitative and describe the...
-
Presented here are nine transactions and the analysis used to account for them. Evaluate each of the suggested accounting treatments and indicate whether it is true or false. 1. Received cash of...
-
A process that produces titanium forgings for automobile turbocharger wheels is to be controlled through the use of a fraction nonconforming chart. Initially, one sample of size 150 is taken each day...
-
Q1) For all of this question: r = 5%, d = 1%, u = 1.07, d = 0.93 a) S = $56, K = $50, T = 3 months. Find the price of the call option with strike K expiring at time T by finding the replicating...
-
Billingham Packaging is considering expanding its production capacity by purchasing a new machine, the XC-750. The cost of the XC-750 is $2.75 million. Unfortunately, installing this machine will...
-
create a children's book that teaches about the reasons for changes in supply and demand. The bulk of your book should revolve around your examples/explanations for the reasons for shifts in demand...
-
The use case diagram of the SecureEd system is given below. Provide a use case description for one of the following use cases: Course Enroll, CourseSearch, EnterGrade, and Search User. Student...
-
The Open Systems Interconnection (OSI) model defines seven layers through which computer systems communicate over a network. It was the first standard model for network communications, and it was...
-
2. Write a program that lets the user enter their first name, last name, faculty, year of study, city/town, province and postal code, and then print them back to the screen with and without...
-
The current risk-free rate is 2 percent and the market risk premium is 3 percent. You are trying to value ABC company and it has an equity beta of 0.8. The company earned $3.50 per share in the year...
-
1. Write a program that accepts four strings as input, then shows the first character of each string as an acronym: Input four strings to four separate variables. Show the strings. Using an f-string,...
-
Cyber Marketing and eCommerce Search for a business or e-commerce that is currently operating. In this forum, explain to your classmates what products and services you offer, who the business is...
-
The comparative statements of financial position of Menachem NV at the beginning and end of the year 2019 appear below. Net income of ¬34,000 was reported, and dividends of ¬23,000 were paid...
-
Answer true or false se to the following questions and briefly justify your answer: a. With the SR protocol, it is possible for the sender to receive an ACK for a packet that falls outside of its...
-
Consider a virtual-circuit network. Suppose the VC number is a 8-bit field. a) What is the maximum number of virtual circuits that can be carried over a link? b) Suppose a central node determines...
-
Consider a variation of the MAC algorithm (Figure 8.9) where the sender sends (m, H(m) + s), where H(m) + s is the concatenation of H(m) and s. Is this variation flawed? Why or why not?
-
The Cola Company reported the following comparative information at December 31 2020, and December 31, 2019 (amounts in millions and adapted): {Requirements} 1. Calculate the following ratios for 2020...
-
Mark IV Industries Inc. issued \(\$ 100\) million \(13 \%\) debentures due March 15,2025 , with interest payable March 15 and September 15; the price was 96.5. {Requirements} Answer these questions:...
-
Sea Spray Marina experienced these events during 2020. a. December revenue totalled \(\$ 110,000\) and, in addition, Sea Spray collected sales tax of \(7 \%\). The sales tax amount will be remitted...

Study smarter with the SolutionInn App


