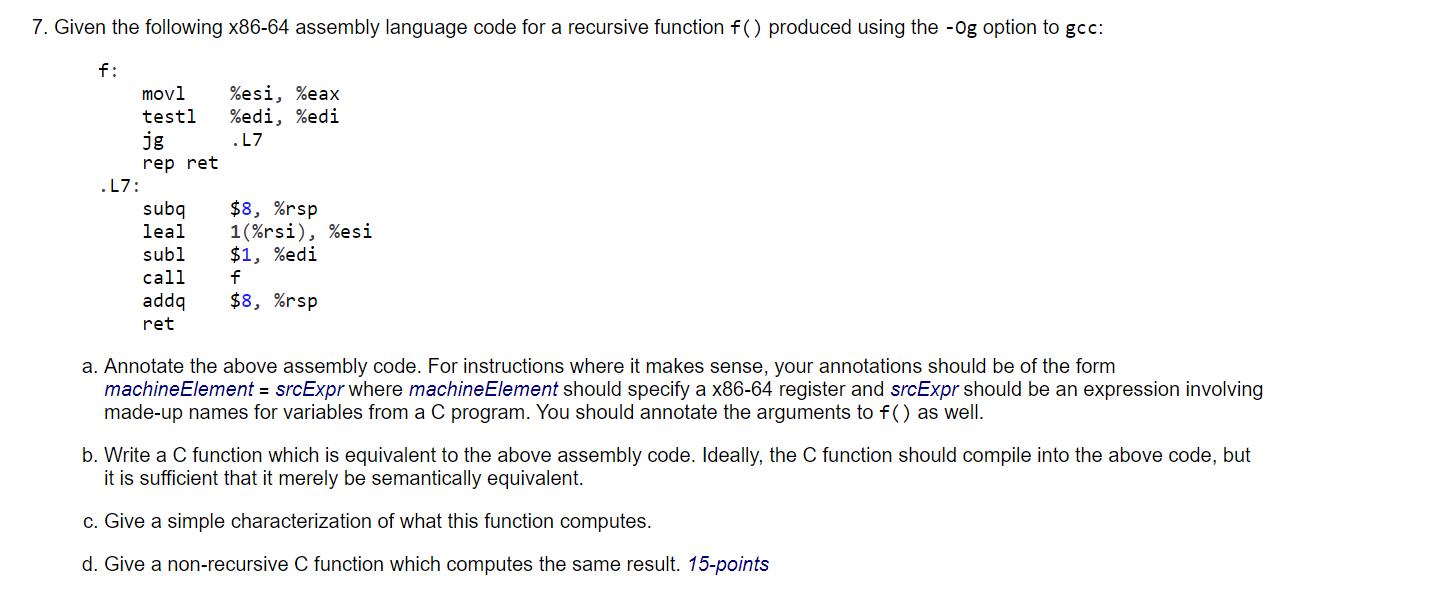
7. Given the following x86-64 assembly language code for a recursive function f() produced using the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
7. Given the following x86-64 assembly language code for a recursive function f() produced using the -og option to gcc: f: movl %esi, %eax testl %edi, %edi. jg .L7 rep ret .L7: subq $8, %rsp leal subl 1(%rsi), %esi $1, %edi call f addq ret $8, %rsp a. Annotate the above assembly code. For instructions where it makes sense, your annotations should be of the form machineElement = srcExpr where machine Element should specify a x86-64 register and srcExpr should be an expression involving made-up names for variables from a C program. You should annotate the arguments to f() as well. b. Write a C function which is equivalent to the above assembly code. Ideally, the C function should compile into the above code, but it is sufficient that it merely be semantically equivalent. c. Give a simple characterization of what this function computes. d. Give a non-recursive C function which computes the same result. 15-points 7. Given the following x86-64 assembly language code for a recursive function f() produced using the -og option to gcc: f: movl %esi, %eax testl %edi, %edi. jg .L7 rep ret .L7: subq $8, %rsp leal subl 1(%rsi), %esi $1, %edi call f addq ret $8, %rsp a. Annotate the above assembly code. For instructions where it makes sense, your annotations should be of the form machineElement = srcExpr where machine Element should specify a x86-64 register and srcExpr should be an expression involving made-up names for variables from a C program. You should annotate the arguments to f() as well. b. Write a C function which is equivalent to the above assembly code. Ideally, the C function should compile into the above code, but it is sufficient that it merely be semantically equivalent. c. Give a simple characterization of what this function computes. d. Give a non-recursive C function which computes the same result. 15-points
Expert Answer:

Related Book For 

Computer organization and architecture designing for performance
ISBN: 978-0136073734
8th edition
Authors: william stallings
Posted Date:
Students also viewed these programming questions
-
Design a Java class that represents a cache with a fixed size. It should support operations like add, retrieve, and remove, and it should evict the least recently used item when it reaches capacity.
-
Mark Cotteleer owns a company that manufactures sailboats, Actual demand for Marks sailboats during each season in 2006 through 2009 was as follows: Mark has forecasted that annual demand for his...
-
Havana, Inc., has identified an investment project with the following cash flows. If the discount rate is 8 percent, what is the future value of these cash flows in Year 4? What is the future value...
-
Suppose that the number of plants of a particular type found in a rectangular sampling region (called a quadrat by ecologists) in a certain geographic area is an rv X with pmf Is E(X) finite? Justify...
-
What are the central dynamics that characterize matrilineal kinship systems?
-
1. Name at least three ways that Shu could automate her asset management. Suggest at least one option for retirement savings, general savings, and general convenience. 2. What major factors should...
-
Assume Highline Company has just paid an annual dividend of $1.05. Analysts are predicting an 11.1% per year growth rate in earnings over the next five years. After then, Highline's earnings are...
-
Extend Example 20.3 to calculate CVA when default can happen in the middle of each month. Assume that the default probability during the first year is 0.001667 per month and the default probability...
-
For the circuit in Figure initial conditions as Vo assuming the 2V and I. 1.5 mA, ic(0+) D ic 100F Vo 1 mH I. 100 2 v
-
Forensic accounting expert witnesses may provide biased testimony. The adversarial system incentivizes attorneys to hire experts who are favorable to their preferred verdict. This creates a potential...
-
A sex offender is convicted and sentenced to a long jail term. Say 10 years. After serving their sentence rather than being released they are civilly committed and remain incarcerated at a mental...
-
Ben needed to replace his laptop so he went shopping at Sim Lim Square. He approached Jerry, a salesman at Newstar Computers and Accessories ("NCA"). Ben told Jerry that he was looking for a 15-inch...
-
Karen's elderly Uncle Joe gave her written authority to sell the family house. Uncle Joe lived in Maine and Karen lived in Minnesota. After about two months Karen found a buyer for the house and...
-
Tom decided to buy his girlfriend, Geri, the latest Orange Series 9 smartwatch for her Christmas present. The watch cost $800. The watch was described to come with sapphire crystal glass that is...
-
6.4 Competitive Advantage (Figure 6-3) We discussed three types of competitive advantages cost, differentiation, and marketing advantages. For each area of advantage, identify a business that has a...
-
How does health insurance risk differ from other types of insurance risk (e.g., automobile or homeowners insurance)? What is the difference between cost sharing and cost shifting? Is retiree health...
-
Define data speculation.
-
Suggest reasons why RAMs traditionally have been organized as only 1 bit per chip whereas ROMs are usually organized with multiple bits per chip.
-
Consider a dynamic partitioning scheme. Show that, on average, the memory contains half as many holes as segments. Discuss.
-
Consider an experiment that selects a cell phone camera and records the recycle time of a flash (the time taken to ready the camera for another flash). The possible values for this time depend on the...
-
Suppose that the recycle times of two cameras are recorded. The extension of the positive real line \(R\) is to take the sample space to be the positive quadrant of the plane \[ S=R^{+} \times R^{+}...
-
Each message in a digital communication system is classified as to whether it is received within the time specified by the system design. If three messages are classified, use a tree diagram to...

Study smarter with the SolutionInn App


