7:19 ivylearn.ivytech.edu Go to https://www.cve.org/and answer explore About: Overview, History, Process, Related Efforts and Metrics and...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
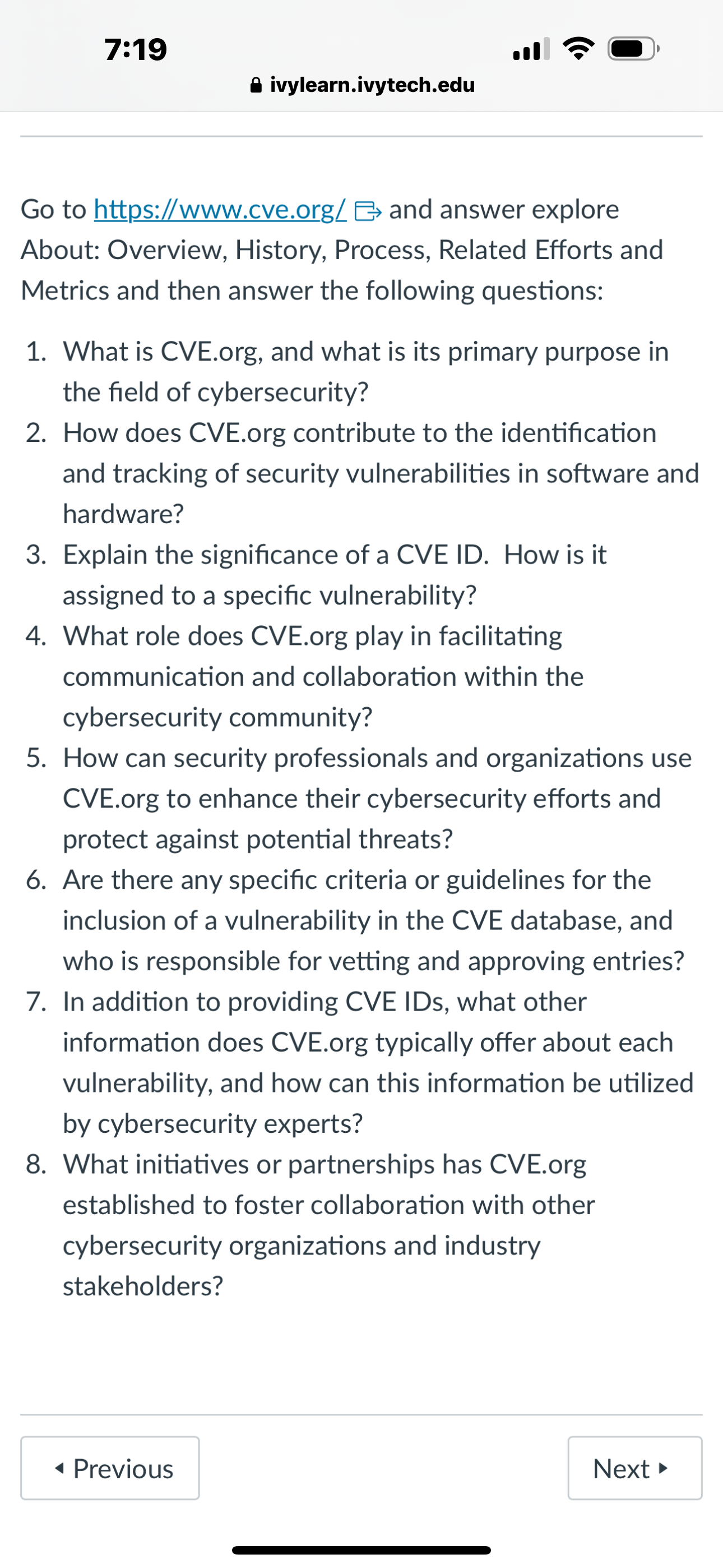
7:19 ivylearn.ivytech.edu Go to https://www.cve.org/and answer explore About: Overview, History, Process, Related Efforts and Metrics and then answer the following questions: 1. What is CVE.org, and what is its primary purpose in the field of cybersecurity? 2. How does CVE.org contribute to the identification and tracking of security vulnerabilities in software and hardware? 3. Explain the significance of a CVE ID. How is it assigned to a specific vulnerability? 4. What role does CVE.org play in facilitating communication and collaboration within the cybersecurity community? 5. How can security professionals and organizations use CVE.org to enhance their cybersecurity efforts and protect against potential threats? 6. Are there any specific criteria or guidelines for the inclusion of a vulnerability in the CVE database, and who is responsible for vetting and approving entries? 7. In addition to providing CVE IDs, what other information does CVE.org typically offer about each vulnerability, and how can this information be utilized by cybersecurity experts? 8. What initiatives or partnerships has CVE.org established to foster collaboration with other cybersecurity organizations and industry stakeholders? Previous Next 7:19 ivylearn.ivytech.edu Go to https://www.cve.org/and answer explore About: Overview, History, Process, Related Efforts and Metrics and then answer the following questions: 1. What is CVE.org, and what is its primary purpose in the field of cybersecurity? 2. How does CVE.org contribute to the identification and tracking of security vulnerabilities in software and hardware? 3. Explain the significance of a CVE ID. How is it assigned to a specific vulnerability? 4. What role does CVE.org play in facilitating communication and collaboration within the cybersecurity community? 5. How can security professionals and organizations use CVE.org to enhance their cybersecurity efforts and protect against potential threats? 6. Are there any specific criteria or guidelines for the inclusion of a vulnerability in the CVE database, and who is responsible for vetting and approving entries? 7. In addition to providing CVE IDs, what other information does CVE.org typically offer about each vulnerability, and how can this information be utilized by cybersecurity experts? 8. What initiatives or partnerships has CVE.org established to foster collaboration with other cybersecurity organizations and industry stakeholders? Previous Next
Expert Answer:

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these algorithms questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Dissertation Topic: "The Effects of Cybersecurity Measures on the Productivity and Well-being of Teleworkers in the Healthcare Industry". Introduction Draft no more than TWO paragraphs here -...
-
George and Weezy received $29,100 of Social Security benefits this year ($11,000 for George: $18,100 for Weezy). They also received $4,800 of Interest from jointly owned City of Ranburne Bonds and...
-
1. It is your sixtieth birthday. You plan to work 5 more years before retiring. Then you want to spend $20,000 for a Mediterranean cruise. What lump sum do you have to invest now to accumulate the...
-
Solve for x. -4+log3(x+1)=-3
-
Find the interquartile range of the data set in Example 1. Are there any outliers? Data from Example 1 Each year in the U.S., automobile commuters waste fuel due to traffic congestion. The amounts...
-
Fleetwood Corporation sold $800,000 of 12 percent, 10-year bonds at face value on September 1, 2014. The issue date of the bonds was May 1, 2014. 1. Prepare the journal entries to record the sale of...
-
Pharoah Company entered into these transactions during May 2025, its first month of operations. 1. Stockholders invested $44,500 in the business in exchange for common stock of the company. 2....
-
24. A positive gamma portfolio tends to have a () left tail than the normal distribution. If the distribution of AP is normal, the calculated VaR tends to be( ). IV too low I heavier A. I, III II...
-
What is meant by a performance-based management fee and what is the basis for determining performance in such an arrangement?
-
Discuss three of the CMS's major value-based programs. Define the programs and the criteria that are needed for each of these programs to be successful.
-
a. Why is the term hedge to describe "hedge funds" misleading? b. Where is the term hedge fund described in the U.S. securities laws?
-
What is the source of income for an asset management firm?
-
Some hedge funds will refer to their strategies as "arbitrage strategies." Why would this be misleading?
-
Jensen and Meckling (1976) refers to the costs that arise due to the use of an agent by a principal in an agency relationship as agency cost. These costs include (1) the costs of opportunistic...
-
The pendulum consists of two rods: AB is pin supported at A and swings only in the y-z plane, whereas a bearing at B allows the attached rod BD to spin about rod AB. At a given instant, the rods have...
-
Scott Butterfield is self-employed as a CPA. He uses the cash method of accounting, and his Social Security number is 644-47-7833. His principal business code is 541211. Scott's CPA practice is...
-
Joan is a self-employed attorney in New York City. Joan took a trip to San Diego, CA, primarily for business, to consult with a client and take a short vacation. On the trip, Joan incurred the...
-
Jim (age 50) and Martha (age 49) are married with three dependent children. They file a joint return for 2012. Their income from salaries totals $50,000, and they received $10,000 in taxable...
-
When and why should exchange rates change under a fixed-exchange-rate system?
-
Using the diagram in exercise 5, illustrate the effect of the change in Japanese tastes if exchange rates are fixed. What will happen to the foreign exchange market equilibrium? Data from in exercise...
-
How does a currency speculator profit from exchange-rate changes? Give an example of a profitable speculation.

Study smarter with the SolutionInn App


