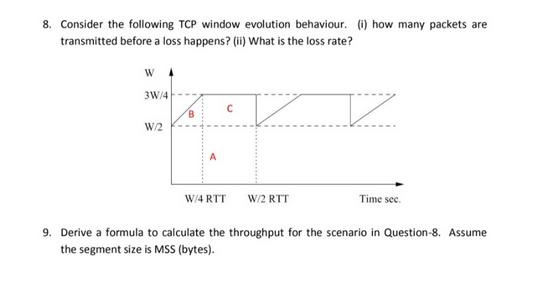
8. Consider the following TCP window evolution behaviour. (i) how many packets are transmitted before a...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
8. Consider the following TCP window evolution behaviour. (i) how many packets are transmitted before a loss happens? (ii) What is the loss rate? V W 3W/4 W/2 B A с V W/4 RTT W/2 RTT Time sec. 9. Derive a formula to calculate the throughput for the scenario in Question-8. Assume the segment size is MSS (bytes). 8. Consider the following TCP window evolution behaviour. (i) how many packets are transmitted before a loss happens? (ii) What is the loss rate? V W 3W/4 W/2 B A с V W/4 RTT W/2 RTT Time sec. 9. Derive a formula to calculate the throughput for the scenario in Question-8. Assume the segment size is MSS (bytes).
Expert Answer:
Answer rating: 100% (QA)
The image depicts a typical TCP window evolution behavior with a focus on congestion control mechanisms It looks like a graph showing how the congesti... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these programming questions
-
Find the limit . Use I\'Hospital\'s rule when appropriate. lim x l n x 2 x
-
A company has a production capacity of 1000 units and is currently producing 600 units. The fixed costs are $1,200. The variable cost per unit is $1. The units sell for $5 each. A customer has...
-
Consider Figure 3.58. Assuming TCP Reno is the protocol experiencing the behavior shown above, answer the following questions. In all cases, you should provide a short discussion justifying your...
-
Use the data given in Table 3.9 to compute the mean, standard deviation, coefficient of variation, and coefficient of skewness for the current ratio of JNJ. Table 3.9 Year 1990 1991 1992 1993 1994...
-
Under what circumstances could the application of 338 be beneficial to the parent corporation? Detrimental?
-
Suppose you need to sort relation r using sort-merge and mergejoin the result with an already sorted relation s. a. Describe how the sort operator is broken into sub operators to model the pipelining...
-
How is arbitration commenced?
-
Rutherford Wheel and Axle, Inc. has an automate production process, and production activity is quantified in terms of process hours. A standard-costing system is used. The annual static budget for...
-
a widower is a fish merchant who buys and sells large quantities of fresh seafood products. He is very rich and also very generous towards the local fishing community. His assets amount to $100...
-
The management of Hartman Company is trying to determine the amount of each of two products to produce over the coming planning period. The following information concerns labor availability, labor...
-
Maximizing the Learning of All Students" and what you have learned, address the scenario below: Mr. Green has taught high school Spanish for10 years. He would like to start differentiating...
-
Many people are called upon to develop documents that meet the needs of their workplaces, from administrative assistants to software developers. Thus, people who are not technical communicators...
-
Find a technical document for a technology that interests you. Assume that you work for the company that developed this technology and that you have been asked to write another document about the...
-
How do recursive heuristics for problem solving differ from recipes or procedural steps provided to help technical communicators generate usable documents?
-
Can you recall a time when one or more of your personally held principles clashed with a value held by an organization or business in which you worked? What was at stake, and for whom? How did you...
-
Research the Shannon-Weaver transmission model of communication. What is the model and where does it come from? How has it been critiqued? Have you ever encountered someone who held to this view of...
-
Match each chemical reaction with the correct diagram according to Hess' Law. Enthalpy, , = + -, = + , = - g Enthalpy. 7 = = - - , = g + = - Enthalpy. , = - ; - , = - B , =...
-
Following is the current balance sheet for a local partnership of doctors: The following questions represent independent situations: a. E is going to invest enough money in this partnership to...
-
Read the POP3 RFC, RFC 1939. What is the purpose of the UIDL POP3 command?
-
Suppose the network layer provides the following service. The network layer in the source host accepts a segment of maximum size l,200 bytes and a destination host address from the transport layer....
-
Suppose Alice wants to communicate with Bob using symmetric key cryptography using a session key KS. In Section 8.2, we learned how public-key cryptography can be used to distribute the session key...
-
When a predecessor auditor reissues the report on the prior period's financial statements at the request of the former client, the predecessor auditor should a. Indicate the introductory paragraph of...
-
When audited financial statements are presented in a client's document containing other information, the auditor should a. Perform inquiry and analytical procedures to ascertain whether the other...
-
Which of the following events occurring after the issuance of an auditor's report most likely would cause the auditor to make further inquiries about the previously issued financial statements? a. A...

Study smarter with the SolutionInn App


