a) A channel with alphabet (0, 1, 2, 3, 4) has transition probabilities of the (10)...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
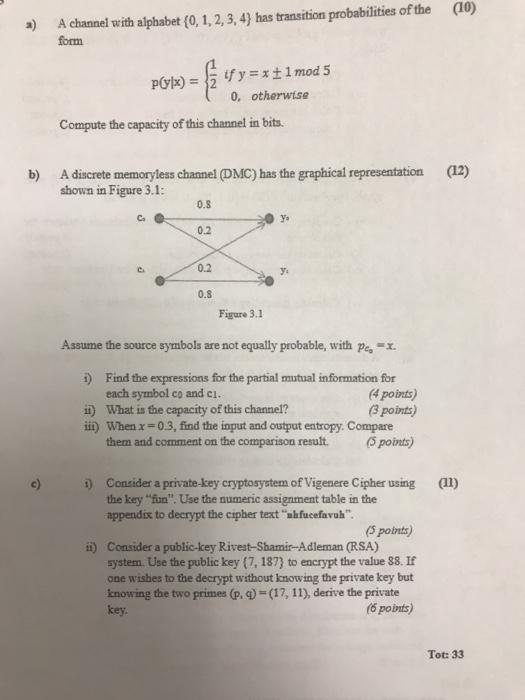
a) A channel with alphabet (0, 1, 2, 3, 4) has transition probabilities of the (10) form P(y|x) = $₁ Compute the capacity of this channel in bits. b) A discrete memoryless channel (DMC) has the graphical representation (12) shown in Figure 3.1: 0.8 0.2 if y=x ±1 mod 5 0, otherwise 0.2 0.8 Figure 3.1 Assume the source symbols are not equally probable, with pe, X. 1) Find the expressions for the partial mutual information for each symbol co and c1. (4 points) ii) What is the capacity of this channel? (3 points) iii) When x=0.3, find the input and output entropy. Compare them and comment on the comparison result. (5 points) 1) Consider a private-key cryptosystem of Vigenere Cipher using (11) the key "fun". Use the numeric assignment table in the appendix to decrypt the cipher text "ahfucefavuh". (5 points) ii) Consider a public-key Rivest-Shamir-Adleman (RSA) system. Use the public key (7, 187) to encrypt the value 88. If one wishes to the decrypt without knowing the private key but knowing the two primes (p, q)=(17, 11), derive the private key. (6 points) Tot: 33 a) A channel with alphabet (0, 1, 2, 3, 4) has transition probabilities of the (10) form P(y|x) = $₁ Compute the capacity of this channel in bits. b) A discrete memoryless channel (DMC) has the graphical representation (12) shown in Figure 3.1: 0.8 0.2 if y=x ±1 mod 5 0, otherwise 0.2 0.8 Figure 3.1 Assume the source symbols are not equally probable, with pe, X. 1) Find the expressions for the partial mutual information for each symbol co and c1. (4 points) ii) What is the capacity of this channel? (3 points) iii) When x=0.3, find the input and output entropy. Compare them and comment on the comparison result. (5 points) 1) Consider a private-key cryptosystem of Vigenere Cipher using (11) the key "fun". Use the numeric assignment table in the appendix to decrypt the cipher text "ahfucefavuh". (5 points) ii) Consider a public-key Rivest-Shamir-Adleman (RSA) system. Use the public key (7, 187) to encrypt the value 88. If one wishes to the decrypt without knowing the private key but knowing the two primes (p, q)=(17, 11), derive the private key. (6 points) Tot: 33
Expert Answer:
Answer rating: 100% (QA)
a To compute the capacity of the given channel we need to determine the channels transition probabilities and calculate the mutual information The tra... View the full answer

Related Book For 

Introduction to Java Programming, Comprehensive Version
ISBN: 978-0133761313
10th Edition
Authors: Y. Daniel Liang
Posted Date:
Students also viewed these accounting questions
-
Analyzing Causes In 2013, it was reported that house prices were increasing for the first time in almost 5 years. Identify the factors that explain why house prices began to rise
-
For the Dupit Corp. case study introduced in Section 11.4, the management science team was able to apply a variety of queueing models by making the following simplifying approximation. Except for the...
-
4 year(s) ago, Mary invested 43,673 dollars. She has earned and will earn compound interest of 11.19 percent per year. In 1 year(s) from today, Zach can make an investment and earn simple interest of...
-
Describe several features of the ACA that are designed to minimize adverse selection. Why might some of those measures not end up working very well?
-
List the quantum numbers for each electron in the ground state of (a) Carbon (Z = 6), (b) Aluminum (Z = 13).
-
The seller may sue the buyer for the price of any lost or damaged goods after the risk of their loss has passed to the buyer. True/False
-
The population densities in people per square mile in the 50 U.S. states have a mean of 199.6 and a standard deviation of 265.4. Random samples of size 35 are drawn from this population, and the mean...
-
The Campbell Company is evaluating the proposed acquisition of a new milling machine. The machines base price is $108,000, and it would cost another $12,500 to modify it for special use by your firm....
-
i need help i need to Write out one minute self-sell. i need to highlight my educational and career accomplishments. And end with a question to encourage two-way communication. The se...
-
1. Name at least three ways that Shu could automate her asset management. Suggest at least one option for retirement savings, general savings, and general convenience. 2. What major factors should...
-
The Cable and the boom Show in the fiq supporta load of 600 Ib. The Compressive for the boom and the tensile is equal 60 .75 C 600Ib T= 439.23 N , C= 537.94 N O T= 537.94 N,., C= 439.23 N Not one of...
-
Give three ways in which utility software might be used to facilitate auditors' assessment of operational efficiency in an application system.
-
How might auditors use the following utilities during the evidence-collection phase of an audit? a. Configuration utility b. Pointer validation utility c. Trace d. Report generator
-
Briefly explain the nature of specialized audit software. Give three reasons why auditors might develop specialized audit software.
-
Briefly explain the nature of a neural network. What are its major components? How can neural networks assist auditors?
-
How might an expert system assist auditors in the following tasks: a. Analyzing the inherent risk associated with an audit b. Evaluating the reliability of an internal control system c. Planning an...
-
155. Activities that involve the production or purchase of merchandise and the sale of goods and services to customers, including expenditures related to administering the business, are classified...
-
Consider the discrete group G of order 8 that has the following Cayley diagram e If we have the sequence of operations: fcagec, which of the options represents the reduction of the sequence to a...
-
Rewrite the preceding program that uses a new greedy algorithm that places an object with the smallest weight into the first bin in which it would fit. Your program should prompt the user to enter...
-
Modify Listing 28.10, ConnectedCircles.java, to enable the user to drag and move a circle. Listing 1 import javafx.application. Application; 2 import javafx.geometry.Point2D; 3 import...
-
Write a program that compresses a source file into a target file using the Huffman coding method. First use ObjectOutputStream to output the Huffman codes into the target file, and then use...
-
Is the Internal Revenue Code responsible for the backdating problem? Did Code Sec. 162(m), which restricts the deductibility of nonperformance-based executive compensation to \(\$ 1\) million, cause...
-
Go to the Securities and Exchange Commission's Internet site (sec.gov) and find a Litigation Release number that deals with each of the following issues. Give the Litigation Release number and write...
-
Determine whether the following are preventive (P), detective (D), or corrective (C) controls. a. Training b. Bank reconciliations c. Passwords d. Surprise cash count e. Quality circle team f. Job...

Study smarter with the SolutionInn App