(a) An n n matrix K is the encryption matrix for the Hill cipher. Give...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
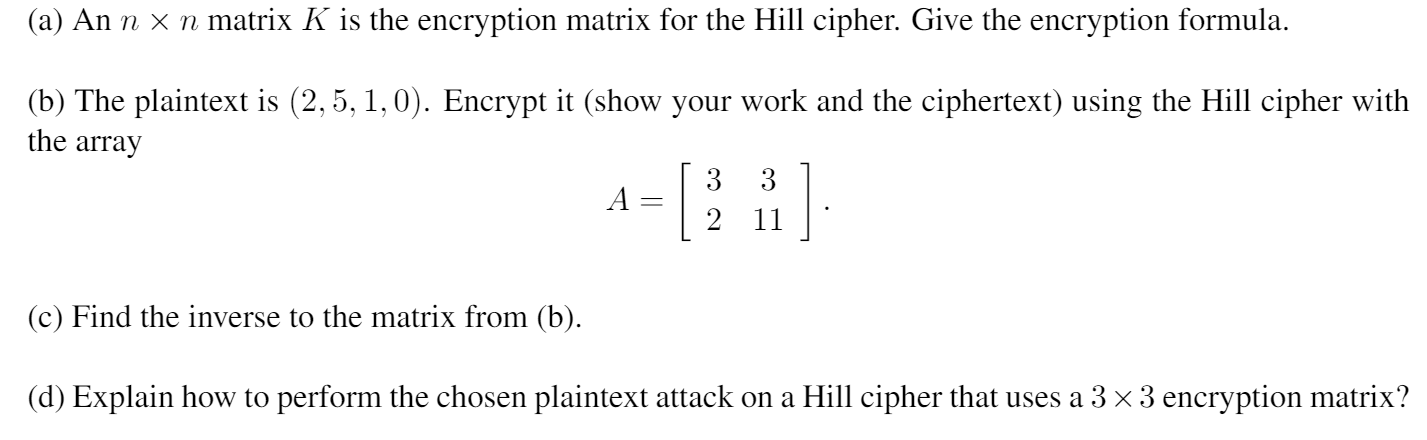
(a) An n × n matrix K is the encryption matrix for the Hill cipher. Give the encryption formula. (b) The plaintext is (2, 5, 1,0). Encrypt it (show your work and the ciphertext) using the Hill cipher with the array (c) Find the inverse to the matrix from (b). A = 3 3 2 11 (d) Explain how to perform the chosen plaintext attack on a Hill cipher that uses a 3 × 3 encryption matrix? (a) An n × n matrix K is the encryption matrix for the Hill cipher. Give the encryption formula. (b) The plaintext is (2, 5, 1,0). Encrypt it (show your work and the ciphertext) using the Hill cipher with the array (c) Find the inverse to the matrix from (b). A = 3 3 2 11 (d) Explain how to perform the chosen plaintext attack on a Hill cipher that uses a 3 × 3 encryption matrix?
Expert Answer:
Answer rating: 100% (QA)
Solution Hill cipher is a polygraphic cipher which is based on Linear Alg... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
Encrypt the following words using a Caesar cipher with a distance value of 5. Provide an algorithm written in python to generate the cypher. So Python Much cipher Wow Write a program to open...
-
Please show your work and write out your solutions in detail by giving formulas and a short summary at the end. Please do not just post about financial calc or excel without explaining how you got...
-
The ciphertext OIKYWVHBX was produced by encrypting a plaintext message using the Vigenre cipher with key HOT. What is the plaintext message?
-
Identify and discuss three ways that tourism and hospitality businesses can maintain a long-term relationship with their clients
-
The New York Times, a profit-maximizing newspaper, faces a downward-sloping demand schedule for advertisements. When advertising for itself in its own pages (for example, an ad saying Read Maureen...
-
Think about this for a minute and then write down as many reasons as you can for people wanting to form a partnership.
-
True or False: If MARR \(=10 \%\) and IRR \(=9 \%\), then ERR \( <10 \%\) and \(\mathrm{PW}>\$ 0\).
-
Stratton Testing is considering investing in a new testing device. It has two options: Option A would have an initial lower cost but would require a significant expenditure for rebuilding after 5...
-
Discuss the breath of responsibilities required of a radiographer. List the five main areas of responsibility in each specialty of radiologic technology. Discuss advantages to working in each of the...
-
On July 1 of this year, R. Green established the Green Rehab Clinic. The organizations account headings are presented below. Transactions completed during the month of July follow. a. Green deposited...
-
Organization: Super League Project type : Establishment of a newprofessional sports league Project name : Super League Date : Apr 2021 Cost : Unknown Synopsis : The public announcement of a new...
-
Your company s Microsoft Entra tenant is configured to send logs to Log Analytics workspace. You need to query the logs and add an additional column to the result set. Which KQL operator should you...
-
Define the following security terms: i . . Attack tree. ii . . Network security. iii. Security attack. iv . . Security mechanism
-
You decided to follow agile methodologies to develop your bike - renting mobile application. Developers in your team start pushing code changes, including bug fixes and new features very frequently...
-
The SSH protocol can be used for the following EXCEPT: A . . Secure remote login B . . Secure file transfer C . . As a VPN protocol D . . Authenticate Web user
-
Do some quick research on the trucking industry in the United States. Concentrate on the large freight carriers (JB Hunt, Knight-Swift, Werner, et al). Select any one macro-environmental force that...
-
You are considering a new product. Machinery and equipment will cost $60,000 if bought today and it will be depreciated straight line to zero over the next three years. In addition, you will require...
-
One study found that the elderly who do not have children dissave at about the same rate as the elderly who do have children. What might this finding imply about the reason the elderly do not dissave...
-
In a bus CSMA/CD network with a data rate of 10 Mbps, a collision occurs 20 s after the first bit of the frame leaves the sending station. What should the length of the frame be so that the sender...
-
Which of the following is a random-access protocol? a. CSMA/CD b. Polling c. TDMA
-
What is the function of the twisting in twisted-pair cable?
-
You have learned the importance of making sure that requirements are correctly identified. Hut how do you know when you have a correct requirement-that is, what criteria must each requirement meet in...
-
Prepare a full feasibility analysis, including Economic, Operational, Schedule, Legal, and Technical analyses for the system you are suggesting in problem 1. Your analysis should be no more than 30...
-
Complete the following sentences: A critical part of designing the deciding how to distribute the system's data. and to different Databases are a resource typically. by many- future. In designing for...

Study smarter with the SolutionInn App


