A. Analyze the network design. Choose the right system devices for project implementation by using Packet...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
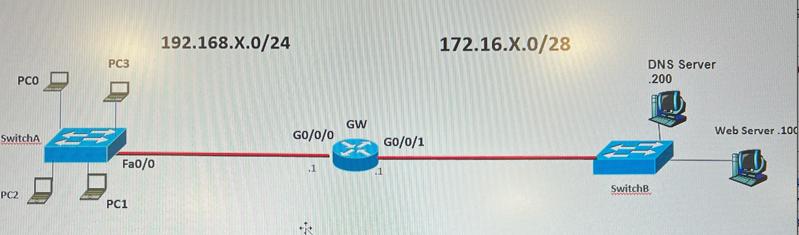
A. Analyze the network design. Choose the right system devices for project implementation by using Packet Tracer. Update the physical topology map based on your ports chosen. B. Apply the right IP settings (static) on all devices. List IP setting table for all IP hosts/devices/servers. Initialized the DNS Server and Web Server (with HTTPs). Domain name: cyt115.local C. Apply switch port security to harden DNS server and Web Server switch access. Test IP connectivity between PCs/Servers and their gateways. D. Make DNS and Web services are available for all PCs. E. Design, deploy and test an ACL filter, so that 1). PC0/1/2/3 are allowed to access DNS and Web services. 2). PCO can PING DNS server and Web server. 3). PC1/2 can SSH login to GW router. 4). All rest type of IP packets from 192.168.X.0/24 network to 172.16.X.0/28 network should be blocked. (X=Group ID) PCO SwitchA PC2 PC3 Fa0/0 PC1 192.168.X.0/24 GO/0/0 ** GW GO/0/1 172.16.X.0/28 DNS Server 200 SwitchB Web Server 100 A. Analyze the network design. Choose the right system devices for project implementation by using Packet Tracer. Update the physical topology map based on your ports chosen. B. Apply the right IP settings (static) on all devices. List IP setting table for all IP hosts/devices/servers. Initialized the DNS Server and Web Server (with HTTPs). Domain name: cyt115.local C. Apply switch port security to harden DNS server and Web Server switch access. Test IP connectivity between PCs/Servers and their gateways. D. Make DNS and Web services are available for all PCs. E. Design, deploy and test an ACL filter, so that 1). PC0/1/2/3 are allowed to access DNS and Web services. 2). PCO can PING DNS server and Web server. 3). PC1/2 can SSH login to GW router. 4). All rest type of IP packets from 192.168.X.0/24 network to 172.16.X.0/28 network should be blocked. (X=Group ID) PCO SwitchA PC2 PC3 Fa0/0 PC1 192.168.X.0/24 GO/0/0 ** GW GO/0/1 172.16.X.0/28 DNS Server 200 SwitchB Web Server 100
Expert Answer:
Answer rating: 100% (QA)
I can provide assistance with the network design as described in the question by providing a general guideline on how to address each point A Analyze the network design Look at the provided network topology to ensure it meets the needs of the scenario Choose appropriate network devices routers switches and ensure that they correctly connect different network segments Ensure redundancy and scalability in the design if required B Apply the right IP settings static on all devices Assign static IP addresses to all devices subnetting the given IP ranges according to the number of hosts required per segment The devices in the 192168X024 network might have IP addresses ranging from 192168X1 to 192168X254 with the gateway GW having an interface in this range as well Similarly devices in the 17216X028 network might have IPs from 17216X1 to 17216X14 since 28 allows for 16 IP addresses in total with 2 reserved for network address and broadcast C Apply switch port security On the switches configure port security to limit the number of MAC addresses that can connect through a port preventing unauthorized access You can also configure additional features like sticky MAC or MAC address whitelisting for stricter control D Make DNS and Web services available for all PCs Ensure DNS and web server IPs are properly configured and reachable from all PCs in the network Implement appropriate routing and switching rules for connectivity between different segments E Design deploy and test ACL filter Configure an Access Control List ACL on the router to meet the specified requirements 1 Permit PC0123 access to DNS and Web services 2 Allow PC0 to ping the DNS server and Web server 3 Permit PC12 to SSH into the gateway router 4 Block all other IP traffic from the 192168X024 network to ... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these computer network questions
-
Pink Rose Co is a constant-growth company that pays out 44 percent of its earnings as dividends and is expected to grow at 2.21 percent. The company has a required return of 7.87 percent. Calculate...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
Consider the following income statement: Fill in the missing numbers and then calculate the OCF. What is the depreciation tax shield? Sales $643,800 Costs 345,300 Depreciation 96,000 EBIT Taxes (35%)...
-
Hillside issues $4,000,000 of 6%, 15-year bonds dated January 1, 2016, that pay interest semiannually on June 30 and December 31. The bonds are issued at a price of $3,456,448. Required 1. Prepare...
-
On January 1, 2016, SugarBear Company acquired equipment costing $150,000, which will be depreciated on the assumption that the equipment will be useful for five years and have a residual value of...
-
The following end-of-year amounts are from the financial statements of Konstan Corporation: total assets, $213,000; total liabilities, $86,000; stockholders equity, $127,000; net sales, $391,000;...
-
Determining sales and variable cost volume variances Required Use the information provided in Exercise 8-3A. a. Determine the sales and variable cost volume variances. b. Classify the variances as...
-
keep in mind in Chapter 1 . Before You Begin: Close the current sample company tab and then open a new one. \ table [ [ Task , Use This Information ] , [ \ table [ [ Add New ] , [ Customers ] ] , \...
-
George and Harry Haygood are building contractors who specialize in the construction of private home dwellings, storage warehouses, and small businesses (less than 20,000 sq. ft. of floor space)....
-
Q1B) AI Arz company for food invested in a new production line that has the information shown in the below table: Develop the depreciation table for the production line using the DDB method and make...
-
The Searider Company uses a job-order costing system. The following transactions occurred in April: a. Raw materials were purchased on account, $180,000. b. Raw materials used in production, $148,000...
-
After watching the video below, what kind of culture do you work in at your organization? How would you like to see your manager initiate a better culture? If you are the manager what would you do to...
-
Morison Cars Inc. has a new project with a cost of $480,000 and annual cash flows of $154,000 for 5 years. The cost of capital for the project is 15%. Calculate (i) net present value, (ii) discounted...
-
flomoku corporation rentsa communication satellite for four years with annual rental payment of 4.8million to be made at the end of each year. if the relevant annual interest rate 4.5%, what is the...
-
What is the importance and advantage for a country in belonging to OIRSA? How does this type of relationship add value to the country's agricultural sector?
-
-1 2 0 4 4 1 3 A 1 1 0 8 1 3 8 pts Time F Alberno 1 Hou 24/7 Find the inverse A of the given matrix A if it exists. 1. Construct the augmented matrix 2. Show all steps to modify it to row echelon...
-
A simple random sample of 220 university students were asked what pasta they usually order and with which sauce. The preferences of these respondents are summarised below: Sauce Bolognese Pasta...
-
I. Define the purpose of an internal monitoring domain, which is an informed awareness of the state of the organizations networks, information systems, and information security defenses. II. Review...
-
True or False: PKI systems are based on public-key cryptosystems and include digital certificates and certificate authorities.
-
I. Gain awareness that a template cipher or perforated page cipher is not strictly an encryption cipher but more of an example of steganography. II. Examine that ciphering is often difficult to...
-
What are the two types of auditors? Briefly define them.
-
How does Philip Wallages view of the audit process compare the empirical scientific cycle to the financial audit process?
-
What are the five components of internal control? Give a sentence on each.

Study smarter with the SolutionInn App


