(a) (b) (c) Discuss how the Pretty Good Privacy (PGP) system can be used to provide...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
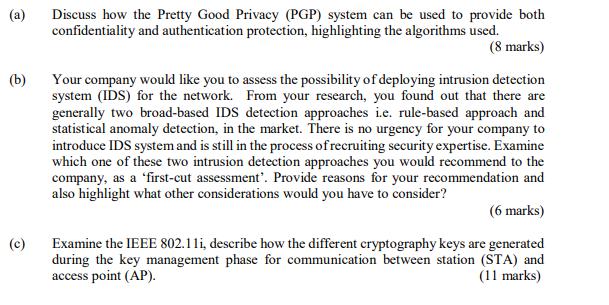
(a) (b) (c) Discuss how the Pretty Good Privacy (PGP) system can be used to provide both confidentiality and authentication protection, highlighting the algorithms used. (8 marks) Your company would like you to assess the possibility of deploying intrusion detection system (IDS) for the network. From your research, you found out that there are generally two broad-based IDS detection approaches i.e. rule-based approach and statistical anomaly detection, in the market. There is no urgency for your company to introduce IDS system and is still in the process of recruiting security expertise. Examine which one of these two intrusion detection approaches you would recommend to the company, as a 'first-cut assessment'. Provide reasons for your recommendation and also highlight what other considerations would you have to consider? (6 marks) Examine the IEEE 802.11i, describe how the different cryptography keys are generated during the key management phase for communication between station (STA) and access point (AP). (11 marks) (a) (b) (c) Discuss how the Pretty Good Privacy (PGP) system can be used to provide both confidentiality and authentication protection, highlighting the algorithms used. (8 marks) Your company would like you to assess the possibility of deploying intrusion detection system (IDS) for the network. From your research, you found out that there are generally two broad-based IDS detection approaches i.e. rule-based approach and statistical anomaly detection, in the market. There is no urgency for your company to introduce IDS system and is still in the process of recruiting security expertise. Examine which one of these two intrusion detection approaches you would recommend to the company, as a 'first-cut assessment'. Provide reasons for your recommendation and also highlight what other considerations would you have to consider? (6 marks) Examine the IEEE 802.11i, describe how the different cryptography keys are generated during the key management phase for communication between station (STA) and access point (AP). (11 marks)
Expert Answer:
Answer rating: 100% (QA)
a Pretty Good Privacy PGP for Confidentiality and Authentication PGP is a widely used cryptographic system that provides both confidentiality and authentication through a combination of symmetric and ... View the full answer

Related Book For 

Management Accounting Information for Decision-Making and Strategy Execution
ISBN: 978-0137024971
6th Edition
Authors: Anthony A. Atkinson, Robert S. Kaplan, Ella Mae Matsumura, S. Mark Young
Posted Date:
Students also viewed these programming questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Hi there , I need help. for my work i need a relevant and well written introduction as well as conclusion to the following below. My work is complete i just need a introduction and conclusion please...
-
Recall the rural medical clinics in Example 8.3 and suppose that each community were required to be 25 miles at most from the nearest clinic. How many clinics would be needed, and what would their...
-
Find the volume and surface area of each solid.. For formulas containing p, give an exact answer and then approximate using 22/7for Ï. 1. Find the volume only. 2. Find the volume only. 10 ft 6...
-
Why are markets for kidneys immoral and unethical, when voluntary exchange is ethical for police, firemen, soldiers, coal miners, and high-rise steel workers, each of whom accepts higher pay in...
-
You are the accountant of a company that is considering expanding its operations to a developing country. The CEO has asked for a report outlining what issues the company should consider from an ESG...
-
Ashwood Mining Co. acquired mineral rights for $15,000,000. The mineral deposit is estimated at 120,000,000 tons. During the current year, 24,000,000 tons were mined and sold. a. Determine the amount...
-
The amount of realized gain to be recognized in a tax year is equal to the gross profit multiplied by the ratio of payments received in the current year divided by the total contract price. ...
-
(a) The steps in the accounting cycle for a merchandising company differ from the steps in the accounting cycle for a service company. Do you agree or disagree? (b) Is the measurement of net income...
-
Symphony Limited is evaluating a proposed capital investment project. The initial investment will be 900,000 and the company operates a straight-line depreciation policy. The initial investment will...
-
What effects does social loafing have on a group? What steps can be taken to minimize social loafing? Describe the difference between a group and a team. When will a team be more effective than a...
-
Define both the Golden Rule and the Platinum Rule. Include in your description an example for each and discuss why each rule might be beneficial and explain the differences in each. Don't forget to...
-
Based on the following data the investment has a positive net present value. time cash flows from investment in a leased property 0 -1,000,000 1 $240,000 2 $240,000 3 $240,000 4 $240,000 5 $240,000 6...
-
What is the computational complexity of the following algorithm? for(int i = n; i = 1; i = i / 2) { } for(int j = 1; j < n; j = j * 2) { System.out.println("i="+i+", j="+j);
-
1. Explain the difference between the human capital and signaling theories of education. 2. Briefly describe each of the 4 main pieces of labor legislation.
-
Find the solution to the interpolation problem of finding a polynomial q(x) with deg(q) < 2 and such that q(xo) = Yo. q(x1) = Y1, and q' (x1) = yi with xo < x1. Under what exact conditions is deg(q)...
-
In July 2013, cnet.com listed the battery life (in hours) and luminous intensity (i. e., screen brightness, in cd/m2) for a sample of tablet computers. We want to know if screen brightness is...
-
What are the three types of information gathering and sharing used under the cooperative form of benchmarking?
-
Describe two broad approaches that companies can use to generate additional revenues.
-
Comparison of two costing systems, original activity-based costs, implementing change The Redwood City plant of Crimson Components Company makes two types of rotators for automobile engines: R361 and...
-
Acne Medication and Gastrointestinal Injury Since 1999, Kamie Kendall had experienced ongoing abdominal pain, and she was eventually diagnosed with ulcerative colitis and irritable bowel syndrome...
-
CMS is a claims processing company in Mobile, Alabama. Chastity Jones, a black woman, completed an online employment application for a customer service position with CMS. Jones interviewed with a...
-
One critical-thinking skill is a heightened awareness of the danger of reaching a conclusion prior to acquiring missing information that were it known would have a reasonable probability of altering...

Study smarter with the SolutionInn App