a. Consider the following hash function. Messages are in the form of a sequence of numbers...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
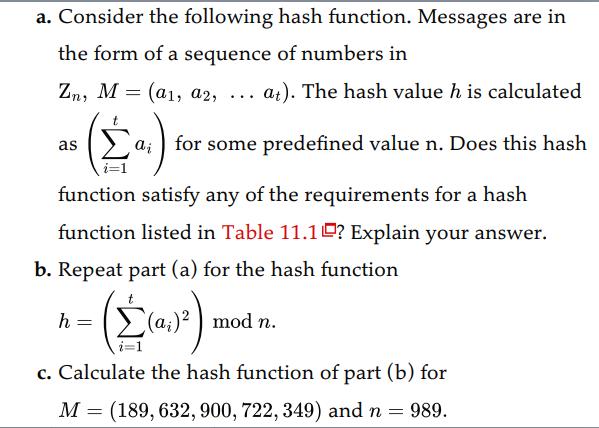
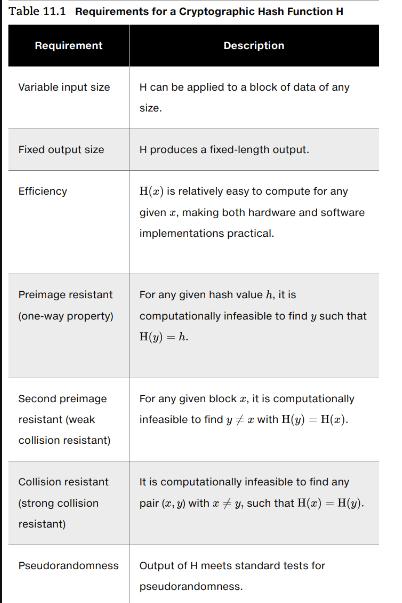
a. Consider the following hash function. Messages are in the form of a sequence of numbers in Zn, M (a1, a2, = at). The hash value h is calculated for some predefined value n. Does this hash as ... function satisfy any of the requirements for a hash function listed in Table 11.1? Explain your answer. b. Repeat part (a) for the hash function -( É(0₂)²) c. Calculate the hash function of part (b) for M = (189, 632, 900, 722, 349) and n = 989. h = mod n. Table 11.1 Requirements for a Cryptographic Hash Function H Requirement Variable input size Fixed output size Efficiency Preimage resistant (one-way property) Second preimage resistant (weak collision resistant) Collision resistant (strong collision resistant) Pseudorandomness Description H can be applied to a block of data of any size. H produces a fixed-length output. H() is relatively easy to compute for any given , making both hardware and software implementations practical. For any given hash value h, it is computationally infeasible to find y such that H(y) =h. For any given block z, it is computationally infeasible to find y + z with H(y) = H (z). # It is computationally infeasible to find any pair (x,y) with #y, such that H(x) - H(y). x Output of H meets standard tests for pseudorandomness. a. Consider the following hash function. Messages are in the form of a sequence of numbers in Zn, M (a1, a2, = at). The hash value h is calculated for some predefined value n. Does this hash as ... function satisfy any of the requirements for a hash function listed in Table 11.1? Explain your answer. b. Repeat part (a) for the hash function -( É(0₂)²) c. Calculate the hash function of part (b) for M = (189, 632, 900, 722, 349) and n = 989. h = mod n. Table 11.1 Requirements for a Cryptographic Hash Function H Requirement Variable input size Fixed output size Efficiency Preimage resistant (one-way property) Second preimage resistant (weak collision resistant) Collision resistant (strong collision resistant) Pseudorandomness Description H can be applied to a block of data of any size. H produces a fixed-length output. H() is relatively easy to compute for any given , making both hardware and software implementations practical. For any given hash value h, it is computationally infeasible to find y such that H(y) =h. For any given block z, it is computationally infeasible to find y + z with H(y) = H (z). # It is computationally infeasible to find any pair (x,y) with #y, such that H(x) - H(y). x Output of H meets standard tests for pseudorandomness.
Expert Answer:
Answer rating: 100% (QA)
Lets examine the given hash functions based on the requirements listed in Table 111 Part a The hash value h is calculated as h sumi1t ai for some pred... View the full answer

Related Book For 

Introduction to Algorithms
ISBN: 978-0262033848
3rd edition
Authors: Thomas H. Cormen, Charles E. Leiserson, Ronald L. Rivest
Posted Date:
Students also viewed these computer network questions
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
The strike price of a compensation option is generally set on the day the option is issued. On November 10, 2000, the CEO of Analog Devices, Jerald Fishman, received 600,000 options. The stock price...
-
A sample of two items is selected without replacement from a batch. Describe the (ordered) sample space for each of the following batches: (a) The batch contains the items {a, b, c, d}. (b) The batch...
-
A hydraulic cylinder on an industrial machine pushes a steel block a distance of x feet (0 x 5), where the variable force required is F(x) = 2000xe -x pounds. Find the work done in pushing the...
-
Scientists studying global warming need to know how the average temperature of the entire Earth, or the global average temperature, has changed with time. Consider two difficulties in trying to...
-
Langrova Inc. has the following amounts included in its general ledger at December 31, 2012. Organization costs ..........................$24,000 Trademarks ..............................20,000...
-
At what point do you think modern societies moved far enough away from iron as the basis for economic function and growth? What was iron replaced with that allowed economies to shift to a new level...
-
The following data relate to the operations of Shilow Company, a wholesale distributor of consumer goods: Current assets as of March 31: Cash $ 8,000 Accounts receivable 20,000 Inventory 36,000...
-
This is a standard costing question. Haytham Kenway opened a company for Templar use and his company uses a standard cost system for controlling the making of the product costs. a)Compute direct...
-
A 9 6 . 6 - kg man is skiing across level ground at a speed of 8 . 3 9 m / s when he comes to the small slope 1 . 8 m higher than ground level shown in the following figure. If the skier coasts up...
-
- A large, open bucket of water sits on a table. The height of the water level in the bucket is 4 m above the surface of the table. A small hole is made in the bucket at a distance of 10 cm above the...
-
Figure below shows one-line diagram of a simple three bus power system with generation at bus 1. Bus 1 is considered as slack bus. A load consisting of 400 MW and 150 MVAR is taken from bus 2. A load...
-
A structure is shown below. Use the x-y coordinate system shown in the figure. 3m Kok +0.625m 1000M 3330 in the y-negative direction 3330 in the y-positive direction 1800 in the y-positive direction...
-
8. Explain how electric forces are like gravitation forces and how they differ.
-
x each the-Kx <1 and find the Value of Find the Ex paenion in owers ofx of Sinhx T.
-
Difference between truncate & delete
-
Analyze SELECT to show that if n 140, then at least n/4 elements are greater than the median-of-medians x and at least n/4 elements are less than x.
-
Prove that if NP co-NP, then P NP.
-
Knuth [212] has shown that there are always roots of optimal subtrees such that root[I, j 1] root[I, j] root[i + 1, j] for all 1 i < j n. Use this fact to modify the OPTIMAL-BST procedure to run...
-
The properties of the members of the truss in the left side of the figure are given in the table. Calculate the nodal displacement and element forces. Show that force equilibrium is satisfied as node...
-
Repeat problem 44 for the truss on the right side of the figure. The properties of element 6 are same as those of element 5 , but T = 0 C T = 0 C . Data From Problem 44: The properties of the...
-
The truss shown in the figure supports the force \(F=1,000 \mathrm{~N}\). Both elements have the same axial rigidity of \(A E=10^{7} \mathrm{~N}\), thermal expansion coefficient of \(\alpha=2 \times...

Study smarter with the SolutionInn App