A corporate has asked you to restructure their single LAN network into small LANs. The corporate...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
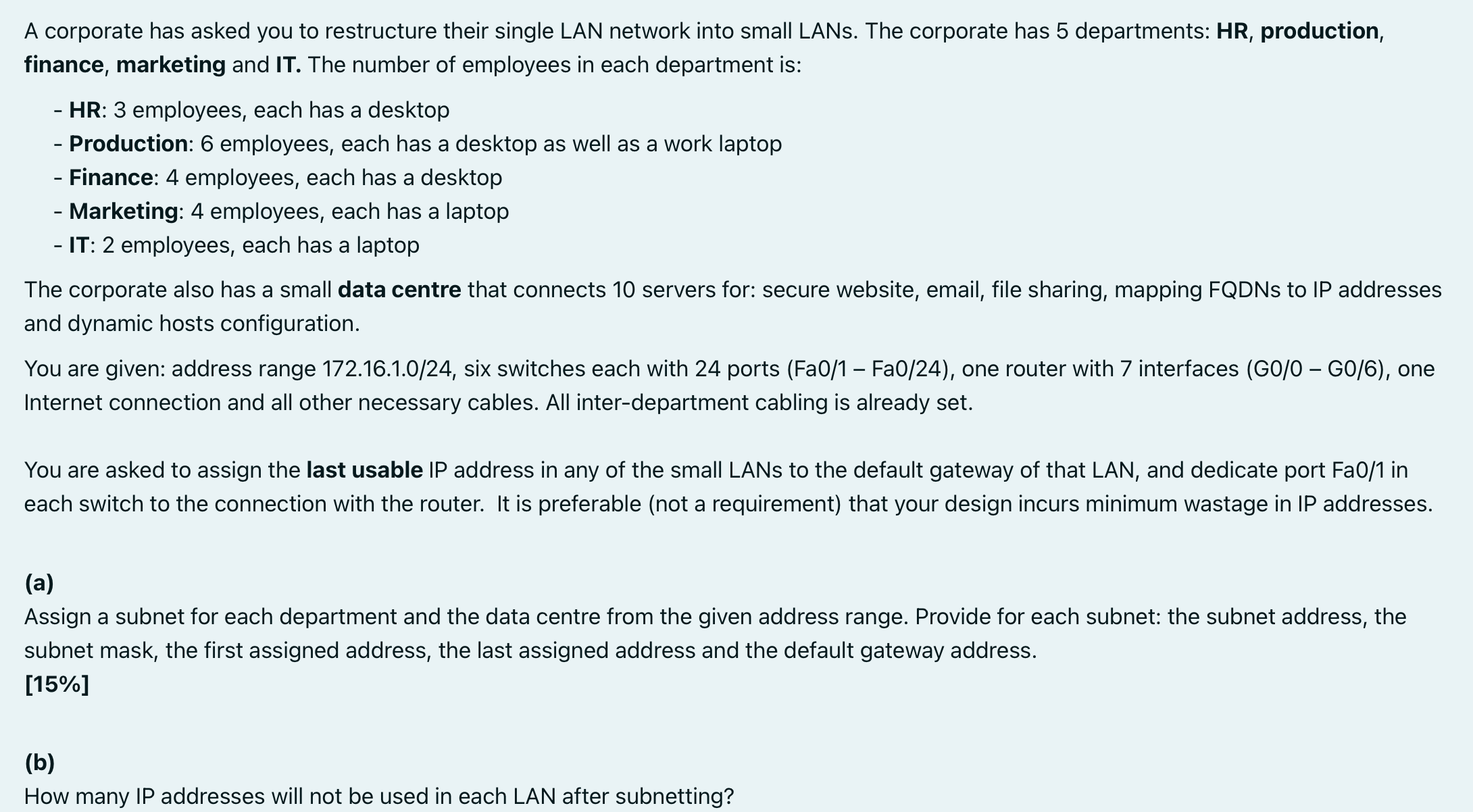
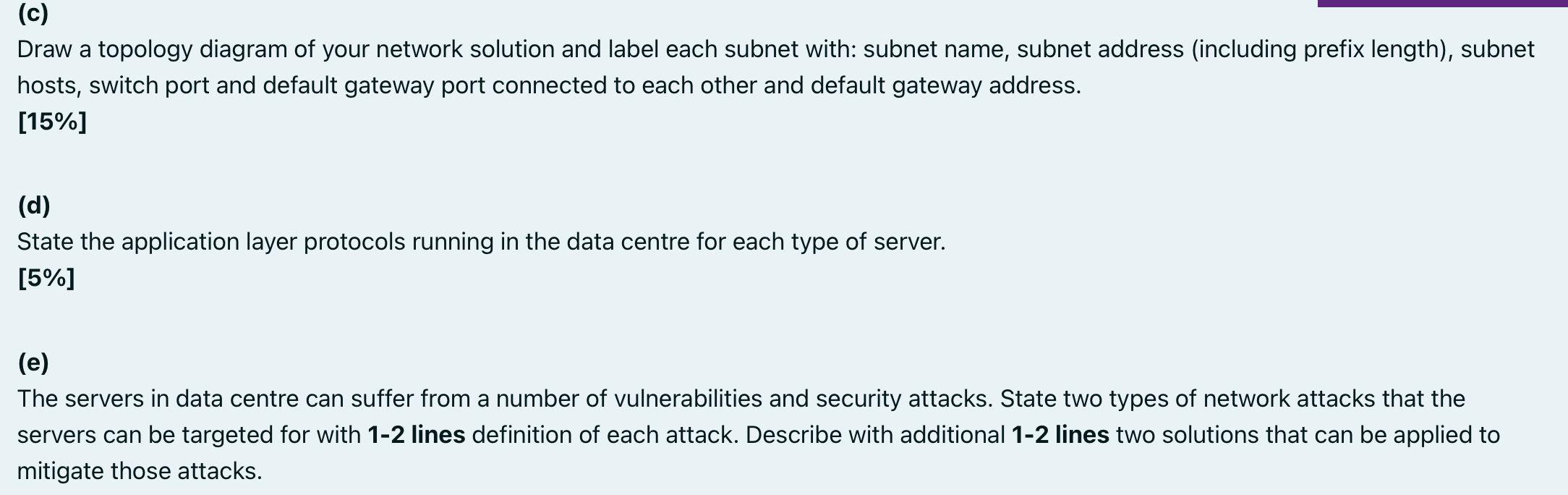
A corporate has asked you to restructure their single LAN network into small LANs. The corporate has 5 departments: HR, production, finance, marketing and IT. The number of employees in each department is: - HR: 3 employees, each has a desktop - Production: 6 employees, each has a desktop as well as a work laptop - Finance: 4 employees, each has a desktop - Marketing: 4 employees, each has a laptop - IT: 2 employees, each has a laptop The corporate also has a small data centre that connects 10 servers for: secure website, email, file sharing, mapping FQDNs to IP addresses and dynamic hosts configuration. You are given: address range 172.16.1.0/24, six switches each with 24 ports (Fa0/1 Fa0/24), one router with 7 interfaces (G0/0 G0/6), one Internet connection and all other necessary cables. All inter-department cabling is already set. You are asked to assign the last usable IP address in any of the small LANs to the default gateway of that LAN, and dedicate port Fa0/1 in each switch to the connection with the router. It is preferable (not a requirement) that your design incurs minimum wastage in IP addresses. (a) Assign a subnet for each department and the data centre from the given address range. Provide for each subnet: the subnet address, the subnet mask, the first assigned address, the last assigned address and the default gateway address. [15%] (b) How many IP addresses will not be used in each LAN after subnetting? (c) Draw a topology diagram of your network solution and label each subnet with: subnet name, subnet address (including prefix length), subnet hosts, switch port and default gateway port connected to each other and default gateway address. [15%] (d) State the application layer protocols running in the data centre for each type of server. [5%] (e) The servers in data centre can suffer from a number of vulnerabilities and security attacks. State two types of network attacks that the servers can be targeted for with 1-2 lines definition of each attack. Describe with additional 1-2 lines two solutions that can be applied to mitigate those attacks. A corporate has asked you to restructure their single LAN network into small LANs. The corporate has 5 departments: HR, production, finance, marketing and IT. The number of employees in each department is: - HR: 3 employees, each has a desktop - Production: 6 employees, each has a desktop as well as a work laptop - Finance: 4 employees, each has a desktop - Marketing: 4 employees, each has a laptop - IT: 2 employees, each has a laptop The corporate also has a small data centre that connects 10 servers for: secure website, email, file sharing, mapping FQDNs to IP addresses and dynamic hosts configuration. You are given: address range 172.16.1.0/24, six switches each with 24 ports (Fa0/1 Fa0/24), one router with 7 interfaces (G0/0 G0/6), one Internet connection and all other necessary cables. All inter-department cabling is already set. You are asked to assign the last usable IP address in any of the small LANs to the default gateway of that LAN, and dedicate port Fa0/1 in each switch to the connection with the router. It is preferable (not a requirement) that your design incurs minimum wastage in IP addresses. (a) Assign a subnet for each department and the data centre from the given address range. Provide for each subnet: the subnet address, the subnet mask, the first assigned address, the last assigned address and the default gateway address. [15%] (b) How many IP addresses will not be used in each LAN after subnetting? (c) Draw a topology diagram of your network solution and label each subnet with: subnet name, subnet address (including prefix length), subnet hosts, switch port and default gateway port connected to each other and default gateway address. [15%] (d) State the application layer protocols running in the data centre for each type of server. [5%] (e) The servers in data centre can suffer from a number of vulnerabilities and security attacks. State two types of network attacks that the servers can be targeted for with 1-2 lines definition of each attack. Describe with additional 1-2 lines two solutions that can be applied to mitigate those attacks.
Expert Answer:

Related Book For 

Auditing and Assurance services an integrated approach
ISBN: 978-0132575959
14th Edition
Authors: Alvin a. arens, Randal j. elder, Mark s. Beasley
Posted Date:
Students also viewed these computer network questions
-
Create a conclusion to following work. Hotels form an uninterrupted narrative of a story, filling guests with emotions that define their stay. They have ceased to be considered one-dimensional places...
-
In Exercises 7582, express the given function h as a composition of two functions f and g so that h(x) = (f g)(x). h(x) = x-9
-
Carr Orthotics Company distributes a specialized ankle support that sells for $30. The company's variable costs are $18 per unit; fixed costs total $360,000 each year. Required a. If sales increase...
-
What is an audit? I Miscues the uses, advantages, and disadvantages of audits.
-
What is the purpose of the IT strategic planning process?
-
Rick and Debbie Siravo own a beachfront home in Wrightsville Beach, N.C. During the year, they rent it for 20 weeks (140 days) at $1,100 per week and use it 10 days for personal purposes. Rick...
-
A 5 N and a 10 N force act on an object. The moment arm of the 5 N force is 0.2 m. If the 10 N force produces five times the torque of the 5 N force, what is its moment arm? ( Express your answer in...
-
Why are global value chains so important to emerging markets and their development? Select two GVCs, and discuss to what extent emerging market firms and governments can respond to the opportunities...
-
XYZ, Inc. reports taxable income of $200,000 for 2008 and has a 30% marginal tax rate. The tax rate is expected to increase to 40% next year and remain at 40% for the foreseeable future. Excluded...
-
Write an essay on the legislative framework for municipal financial management in South Africa by way of summarising key acts and policy.
-
Write a program to Reverse a queue using stack
-
Compare and contrast operational budgets and capital budgets in local government in South Africa.
-
Compare and contrast routine purchasing to tendering in the South African context.
-
Discuss decentralisation as a reform in tendering for state contracts in South Africa.
-
Implement partition (L,P,S) such that P is the prefix of L and s is the suffix of L and append (P,S,L) holds If L is [],then P and s are [). If L is [H] , then P is [H] and s is 1. Otherwise, let...
-
Maria Castigliani is head of the purchasing department of Ambrosiana Merceti, a medium-sized construction company. One morning she walked into the office and said, The main problem in this office is...
-
Describe the action that an auditor should take if an attorney refuses to provide information that is within the attorney's jurisdiction and may directly affect the fair presentation of the financial...
-
Items 1 through 6 are questions typically found in a standard internal control questionnaire used by auditors to obtain an understanding of internal control for notes payable. In using the...
-
The following (1 through 18) are the balance-related, transaction-related, and presentation and disclosure related audit objectives. Balance-Related Audit Objectives 1. Existence 2. Completeness 3....
-
Estimate the fundamental frequency of a cantilever beam whose cross-sectional area and moment of inertia vary as \[A(x)=A_{0} \frac{x}{l} \quad \text { and } \quad I(x)=\bar{I} \frac{x}{l}\] where...
-
Find the response of a simply supported beam subject to a uniformly distributed harmonically varying load.
-
Prove that the constant \(a\) in Eq. (8.82) is positive for common boundary conditions. c dW(x) W(x) dx4 = 1 dT(t) T(t) dt = a = w (8.82)

Study smarter with the SolutionInn App