a. Cross Site Request Forgery (CSRF) attacks against web sites that rely solely on cookies for...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
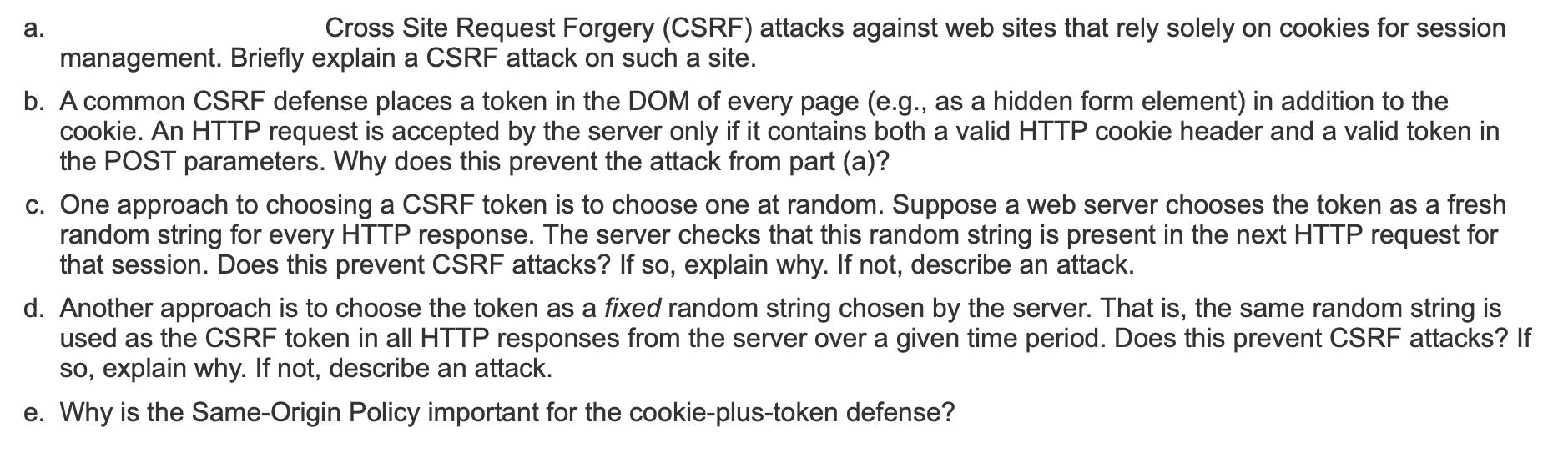
a. Cross Site Request Forgery (CSRF) attacks against web sites that rely solely on cookies for session management. Briefly explain a CSRF attack on such a site. b. A common CSRF defense places a token in the DOM of every page (e.g., as a hidden form element) in addition to the cookie. An HTTP request is accepted by the server only if it contains both a valid HTTP cookie header and a valid token in the POST parameters. Why does this prevent the attack from part (a)? c. One approach to choosing a CSRF token is to choose one at random. Suppose a web server chooses the token as a fresh random string for every HTTP response. The server checks that this random string is present in the next HTTP request for that session. Does this prevent CSRF attacks? If so, explain why. If not, describe an attack. d. Another approach is to choose the token as a fixed random string chosen by the server. That is, the same random string is used as the CSRF token in all HTTP responses from the server over a given time period. Does this prevent CSRF attacks? If so, explain why. If not, describe an attack. e. Why is the Same-Origin Policy important for the cookie-plus-token defense? a. Cross Site Request Forgery (CSRF) attacks against web sites that rely solely on cookies for session management. Briefly explain a CSRF attack on such a site. b. A common CSRF defense places a token in the DOM of every page (e.g., as a hidden form element) in addition to the cookie. An HTTP request is accepted by the server only if it contains both a valid HTTP cookie header and a valid token in the POST parameters. Why does this prevent the attack from part (a)? c. One approach to choosing a CSRF token is to choose one at random. Suppose a web server chooses the token as a fresh random string for every HTTP response. The server checks that this random string is present in the next HTTP request for that session. Does this prevent CSRF attacks? If so, explain why. If not, describe an attack. d. Another approach is to choose the token as a fixed random string chosen by the server. That is, the same random string is used as the CSRF token in all HTTP responses from the server over a given time period. Does this prevent CSRF attacks? If so, explain why. If not, describe an attack. e. Why is the Same-Origin Policy important for the cookie-plus-token defense?
Expert Answer:
Answer rating: 100% (QA)
a In a CSRF attack against a site relying solely on cookies for session management an attacker tricks a users browser into making an unintended and ma... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these accounting questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
Assume FCFs are $2 million for two years (FCF1 and FCF2) and FCFs grow 3% thereafter. Assume WACC = 7%. Calculate firms value
-
Offer an argument for why a political regime that favors a large government will cause interest rates to be higher. Offer at least one example of why a political regime that favors a large government...
-
A lawnmower tractor engine produces 18 hp using 40 Btu/s of heat transfer from burning fuel. Find the thermal efficiency and the rate of heat transfer rejected to the ambient.
-
Write a Monte Carlo code for a system of \(N\) hard spheres of diameter \(D\) on a one-dimensional ring of length \(L\) with periodic boundary conditions. Calculate the pair correlation function and...
-
Kozma Companys chart of accounts includes the following selected accounts. 101 Cash ............... 401 Sales Revenue 112 Accounts Receivable ........ 414 Sales Discounts 120 Inventory ................
-
You are about to make a delicious chicken Alfredo pasta for dinner but realize you are out of prego Alfredo sauce so you rush to the supermarket to pick uo a bottle. As yiu are heading down tge aisle...
-
7. Copper Mines, Inc (CMI) . purchased property for the purpose of extracting copper ore. CMl paid $3,500,000 for the property plus $100,000 closing costs. CMl estimates it will be able to extract...
-
BENEFITS AND DRAWBACKS OF AGILE PROJECT MANAGEMENT IN BANKING SECTOR explain these in brief with references Agile Software Development and Modeling Adopting Agile Methods and Project Management in...
-
The chart below contains a description of top risks, inherent risk assessment, three risk response alternatives, and residual risk assessment for each response alternative for Jones Hiking Trails....
-
BUS 420 - Capital Structure - page 3 Team # 2. World Outsourcing Corp. (WOC) is an unleveraged firm with 60m shares outstanding. WOC's marginal income tax rate is 40% per year; its financial distress...
-
1) Evaluate the company's marketing profitability and how it contributes to net profit before taxes. 2) How would marketing profits and net profit change if sales increase by 25 percent? 3) Evaluate...
-
Deus Inc. manufactures office tables and chairs in its two factories located in Luzon and Visayas. Both factories produce the same two products and then sells them to wholesalers located in the...
-
On December 31, Year 1, Delta issues 1 million shares of common stock to equity investors in exchange for $50 million in cash. Delta traditionally declares and pays an annual dividend of $2 per share...
-
Analyse the plot below that shows absorbance at 405 nm as time (s) increases. Select the absorbance values that best match the data points shown. Absorbance (405 nm) 1 0.8 0.6 0.4 0.2 0 Absorbance at...
-
Assessing simultaneous changes in CVP relationships Braun Corporation sells hammocks; variable costs are $75 each, and the hammocks are sold for $125 each. Braun incurs $240,000 of fixed operating...
-
Relate that dust particle buildups and debris inside systems can dramatically reduce the effectiveness and efficiency of the equipment. This often leads to unexpected shutdowns and overheating....
-
Compensating for weak or missing security mechanisms in the protection infrastructure, such as firewalls. Identification and authentication systems, link encryption systems, access control...
-
The piece of the system that manages access controls within TCB is an object known as which of the following? a. Covert channel b. Storage channel c. Reference monitor d. Standard
-
Design a fast LOT-based filter bank with at least eight sub-bands.
-
Prove the relationship in Equation (9.210). CC2=CC = 0, (9.210)
-
Show that the relations in Equations (9.256)-(9.258) are valid. E(z) = [C3+2 (I - 3)]4. (9.256)

Study smarter with the SolutionInn App


