A Main method will have a loop of your choice that will ask five users one...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
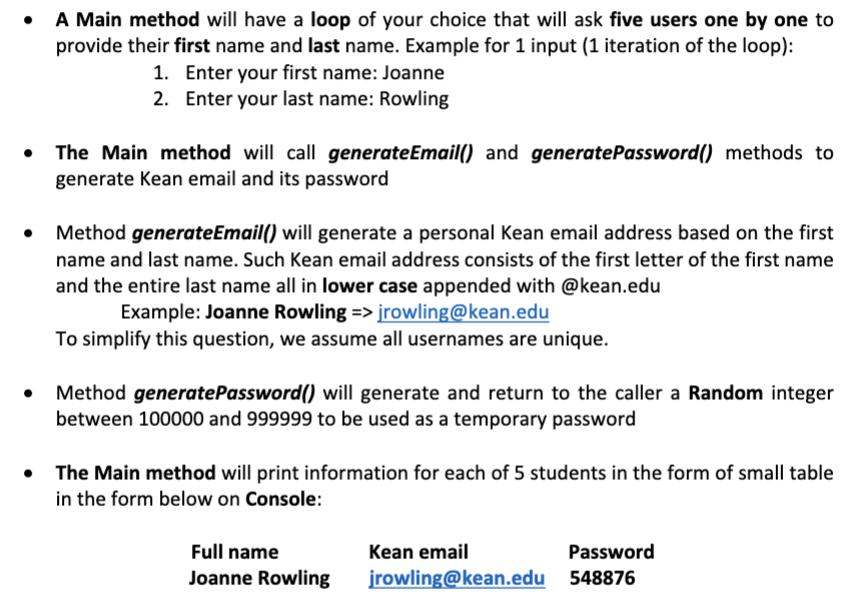
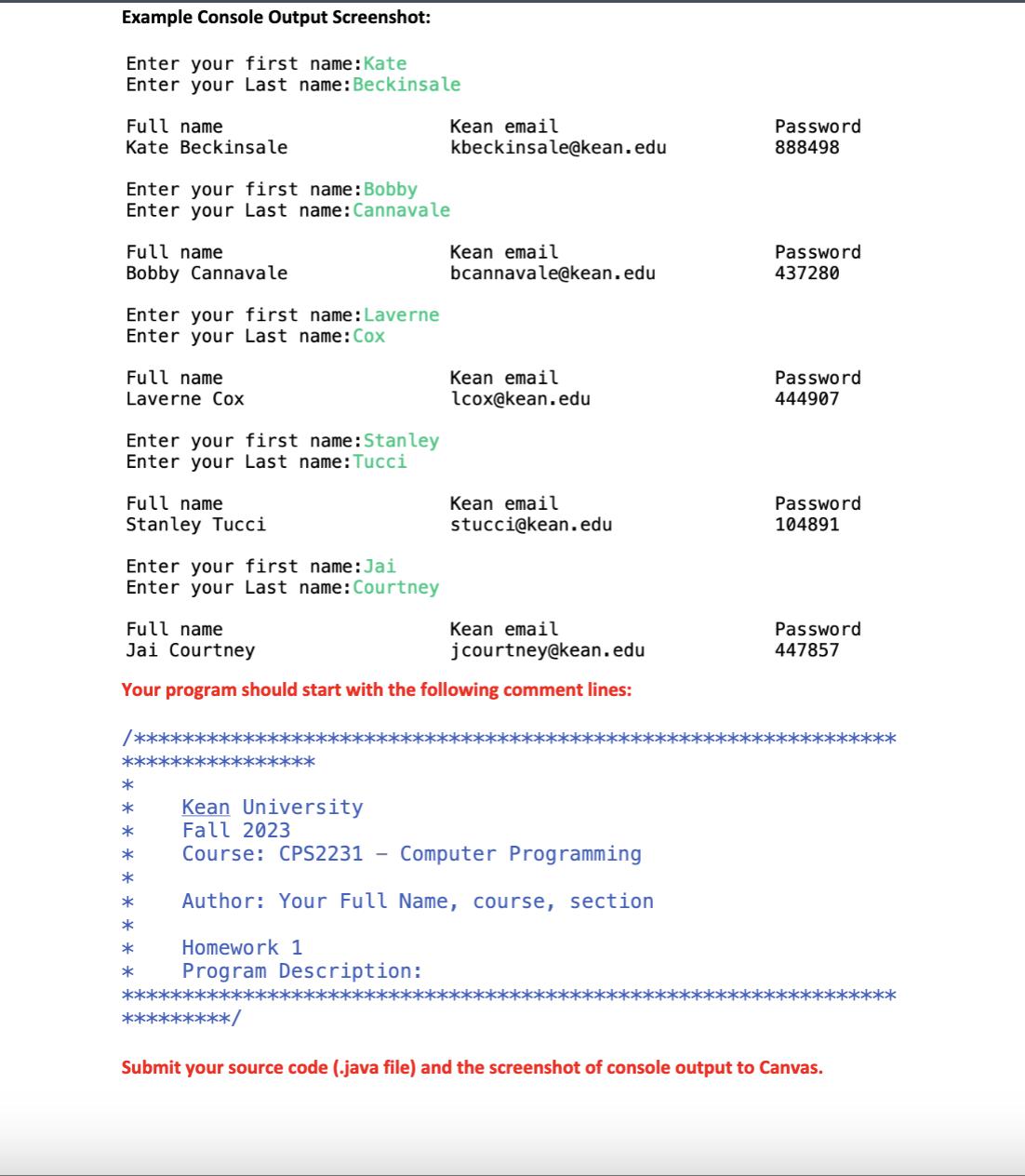
• A Main method will have a loop of your choice that will ask five users one by one to provide their first name and last name. Example for 1 input (1 iteration of the loop): 1. Enter your first name: Joanne 2. Enter your last name: Rowling The Main method will call generateEmail() and generatePassword() methods to generate Kean email and its password Method generateEmail() will generate a personal Kean email address based on the first name and last name. Such Kean email address consists of the first letter of the first name and the entire last name all in lower case appended with @kean.edu Example: Joanne Rowling => jrowling@kean.edu To simplify this question, we assume all usernames are unique. Method generatePassword() will generate and return to the caller a Random integer between 100000 and 999999 to be used as a temporary password • The Main method will print information for each of 5 students in the form of small table in the form below on Console: Full name Joanne Rowling Kean email jrowling@kean.edu Password 548876 Example Console Output Screenshot: Enter your first name: Kate Enter your Last name: Beckinsale Full name Kate Beckinsale Enter your first name: Bobby Enter your Last name: Cannavale Full name Bobby Cannavale Enter your first name: Laverne Enter your Last name: Cox Full name Laverne Cox Enter your first name: Stanley Enter your Last name: Tucci Full name Stanley Tucci Enter your first name: Jai Enter your Last name: Courtney /******** * * * * * * * * * *** Kean email kbeckinsale@kean.edu Kean email bcannavale@kean.edu Full name Kean email jcourtney@kean.edu Jai Courtney Your program should start with the following comment lines: Kean email lcox@kean.edu *********/ Kean email stucci@kean.edu Kean University Fall 2023 Course: CPS2231 Computer Programming Author: Your Full Name, course, section Homework 1 Program Description: Password 888498 Password 437280 Password 444907 Password 104891 Password 447857 Submit your source code (.java file) and the screenshot of console output to Canvas. ***** • A Main method will have a loop of your choice that will ask five users one by one to provide their first name and last name. Example for 1 input (1 iteration of the loop): 1. Enter your first name: Joanne 2. Enter your last name: Rowling The Main method will call generateEmail() and generatePassword() methods to generate Kean email and its password Method generateEmail() will generate a personal Kean email address based on the first name and last name. Such Kean email address consists of the first letter of the first name and the entire last name all in lower case appended with @kean.edu Example: Joanne Rowling => jrowling@kean.edu To simplify this question, we assume all usernames are unique. Method generatePassword() will generate and return to the caller a Random integer between 100000 and 999999 to be used as a temporary password • The Main method will print information for each of 5 students in the form of small table in the form below on Console: Full name Joanne Rowling Kean email jrowling@kean.edu Password 548876 Example Console Output Screenshot: Enter your first name: Kate Enter your Last name: Beckinsale Full name Kate Beckinsale Enter your first name: Bobby Enter your Last name: Cannavale Full name Bobby Cannavale Enter your first name: Laverne Enter your Last name: Cox Full name Laverne Cox Enter your first name: Stanley Enter your Last name: Tucci Full name Stanley Tucci Enter your first name: Jai Enter your Last name: Courtney /******** * * * * * * * * * *** Kean email kbeckinsale@kean.edu Kean email bcannavale@kean.edu Full name Kean email jcourtney@kean.edu Jai Courtney Your program should start with the following comment lines: Kean email lcox@kean.edu *********/ Kean email stucci@kean.edu Kean University Fall 2023 Course: CPS2231 Computer Programming Author: Your Full Name, course, section Homework 1 Program Description: Password 888498 Password 437280 Password 444907 Password 104891 Password 447857 Submit your source code (.java file) and the screenshot of console output to Canvas. *****
Expert Answer:
Related Book For 

Systems Analysis And Design
ISBN: 978-1119496489
7th Edition
Authors: Alan Dennis, Barbara Wixom, Roberta M. Roth
Posted Date:
Students also viewed these programming questions
-
Explain the methodology of calculation of HDI.
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
THIRD AVENUE SOFTWARE HEALTH-CARE APP PROJECT This case is new for the ninth edition of Information Technology Project Management . The case provides an opportunity to apply agile and Scrum...
-
The pilot of a small boat charts a course such that the boat will always be equidistant from an upcoming rock and the shoreline. Describe the path of the boat. If the rock is 2 miles offshore, write...
-
When faced with labour shortages and high staff turnover, most retail stores do not bother with criminal record checks when hiring employees. Explain what internal control activity is missing from...
-
Think for a moment about a computerised accounting system - that is, one where all the entries are made on computer and the books are electronic documents. Can you think of any reason why the folio...
-
Define extinguishment of debt.
-
Leslie and Leon Lazo are married and file a joint return for 2014. Leslie's Social Security number is 466-47-3311 and Leon's is 467-74-4451. They live at 143 Snapdragon Drive, Reno, NV 82102. For...
-
Sunland Street Inc. makes unfinished bookcases that it sells for$58. Production costs are $37 variable and $11 fixed. Because ithas unused capacity, sunland Street is considering finishing thebookc 2...
-
Determine the forces in members AB , AC , and AD . Point M is the centroid of triangle BCD . The forces are positive if in tension, negative if in compression. B 5.2' M 5.2' 1190 lb x D 5.2 6.6'
-
A long one-year forward contract on a productive asset was entered at a forward price of 1,000. Now, seven months later, the underlying asset is selling for 1,050. The PV of the cost to store,...
-
The following question is taken from the June 2011 F8 Paper Audit and Assurance of the ACCA. We are only asking you to consider requirement (a) of the question. You are an audit manager in NAB &...
-
You are auditing a listed company that manufactures high quality engineering products with numerous components, manufactured and assembled by the company. During your audit of inventory valuation you...
-
Moorfoot plc You are the auditor of Duddingston Limited, a subsidiary of Moorfoot plc. Duddingston is engaged in the production and selling of pharmaceutical products. The managing director of...
-
Identify the five sections of The UK Corporate Governance Code and explain why each area of guidance, if properly implemented, will contribute to good corporate governance. Can you illustrate the...
-
We noted in the chapter that often the directors of a company exerted a considerable influence, more so when there is no audit committee, in determining which firm of auditors should be appointed....
-
What is "Auditor Change"? How does the SEC phrase it? How widespread is it?
-
Cornell and Roberts are partners who agree to admit Stanley to their partnership. Cornell has a capital balance of $80,000 and Roberts has a capital balance of $120,000. Cornell and Roberts share net...
-
Create a set of use cases for the process of buying glasses from the viewpoint of the patient, but do not bother to identify the steps within each use case. (Just complete the information at the top...
-
Describe the principal steps in the implementation phase. What are the major deliverables?
-
Suppose that you are installing a new accounting package in your small business. What conversion strategy would you use? Develop a conversion plan (i.e., technical aspects only).
-
1. The German-American Vocational League was formed in New York during World War II to serve as a propaganda agency for the German Reich. Under U.S. law all foreign agents were required to register....
-
3. David and Fiona Rookard purchased tickets for a trip through Mexico from a Mexicoach office in San Diego. Mexicoach told them that the trip would be safe. It did not tell them, however, that their...
-
2. ETHICS Radio TV Reports (RTV) was in the business of recording, transcribing, and monitoring radio and video programming for its clients. The Department of Defense (DOD) in Washington, D.C., was...

Study smarter with the SolutionInn App



