a. Show the layered protocol architecture (i.e., how you would represent them using OSI layers) of...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
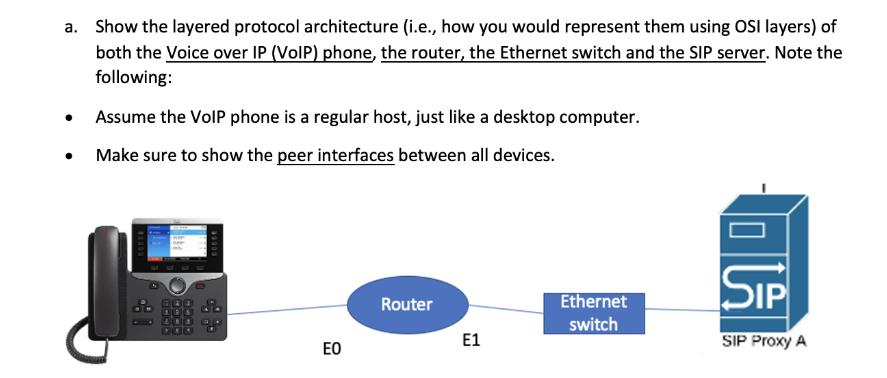
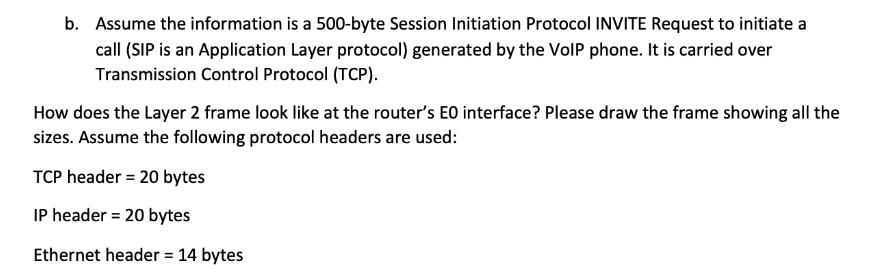
a. Show the layered protocol architecture (i.e., how you would represent them using OSI layers) of both the Voice over IP (VoIP) phone, the router, the Ethernet switch and the SIP server. Note the following: Assume the VoIP phone is a regular host, just like a desktop computer. Make sure to show the peer interfaces between all devices. cosce EO Router E1 Ethernet switch SIP SIP Proxy A b. Assume the information is a 500-byte Session Initiation Protocol INVITE Request to initiate a call (SIP is an Application Layer protocol) generated by the VoIP phone. It is carried over Transmission Control Protocol (TCP). How does the Layer 2 frame look like at the router's EO interface? Please draw the frame showing all the sizes. Assume the following protocol headers are used: TCP header= 20 bytes IP header = 20 bytes Ethernet header = 14 bytes a. Show the layered protocol architecture (i.e., how you would represent them using OSI layers) of both the Voice over IP (VoIP) phone, the router, the Ethernet switch and the SIP server. Note the following: Assume the VoIP phone is a regular host, just like a desktop computer. Make sure to show the peer interfaces between all devices. cosce EO Router E1 Ethernet switch SIP SIP Proxy A b. Assume the information is a 500-byte Session Initiation Protocol INVITE Request to initiate a call (SIP is an Application Layer protocol) generated by the VoIP phone. It is carried over Transmission Control Protocol (TCP). How does the Layer 2 frame look like at the router's EO interface? Please draw the frame showing all the sizes. Assume the following protocol headers are used: TCP header= 20 bytes IP header = 20 bytes Ethernet header = 14 bytes
Expert Answer:
Answer rating: 100% (QA)
To represent the layered protocol architecture of Voice over IP VoIP phone router Ethernet switch an... View the full answer

Related Book For 

Business Data Networks and Security
ISBN: 978-0134817125
11th Edition
Authors: Raymond R. Panko, Julia L. Panko
Posted Date:
Students also viewed these computer network questions
-
When Does a Bilateral Agreement Go into Effect? Suppose in the previous example, Sailors Maritime had said to Barnes and Layton, We will consider your written acceptance of this new proposal as...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
On December 1, 2016, Masipag sold land in exchange for a P180,000 non-interest, 1-year promissory note. The 10% interest rate was going market rate for similar notes. Masipag had paid P66,000 to...
-
Forsyth Company manufactures one product, it does not maintain any beginning or ending inventories, and its uses a standard cost system. During the year, the company produced and sold 10,000 units at...
-
Show that the Lagrangian \(L=\left(q_{1} \dot{q}_{2}-q_{2} \dot{q}_{1} ight)^{2}-a\left(q_{1}-q_{2} ight)^{4}\) is invariant under the transformations and construct the corresponding conserved...
-
The following tentative auditor's report was drafted by a staff accountant and submitted to a partner in the public accounting firm of Bettrioni & Bee. AUDITOR'S REPORT To the Audit Committee of...
-
1. Identify the ethical issues involved in the case from a consequentialist and deontological perspective (refer to Chapter 2). 2. Identify the management issues involved in the case. For example,...
-
Please help. The following statements are the general principles in the accounting for share??based transactions, except: 0 a. IFRS 2 requires that the intrinsic value ofthe equity instruments is...
-
An exercise advocate wants to determine the effect that walking rigorously has on weight loss. The researcher recruits participants to engage in a weeklong study. The researcher instructs...
-
What are the primary types of activities associated with your job? Which of these activities are most likely to be automated in the next 10 years? How do you think this might impact you?
-
True or False: A worn sleeve bearing will usually be indicated by harmonics of a fundamental frequency that is less than half the shaft speed.
-
Report writing is very time-consuming. What should be added to a trending database to quickly interrogate vibration data yet yield a quality report?
-
True or False: The rotor can be turning very slowly in sleeve bearings for an accurate motor end bracket impact analysis.
-
Explain the working of Cochran boiler and fusible plug with neat sketches.
-
True or False: Balancing a rotor suspected of running near a resonant frequency calls for care when increasing the size of the trial weight indicated by a balance program.
-
In 2020 the money purchase limit, or maximum combined contribution an employee and employer can contribute into an RPP, was $27,830 (18% of $154,611). What are the implications to someone whose...
-
The swap spread is the difference between the swap rate and the equivalent-maturity Treasury bond yield. Explain why a widening swap spread may be a signal of deteriorating economic conditions. Plot...
-
a. Why do MANs have higher typical speeds than broader-scope WANs? 3a.) MAN speeds are faster than WAN speeds. This is because of ________. a. Technological limitations b. Regulatory limitations c....
-
What problem is caused by the way that IPv4 handles options?
-
a. What kind of attack may succeed against a system with no technological vulnerabilities? 6a.) What kind of attack is most likely to succeed against a system with no technological vulnerabilities?...
-
Assume that Microsoft Corporation acquired 90 percent of the outstanding common stock of Powerline Technologies for \($3,000,000\) cash plus 200,000 shares of Microsoft's \($10\) par value common...
-
Blue S.A., a French telecommunications company, acquired a 45 percent interest in E-Minus for 65,000,000. Blue consolidates E-Minus because it has special voting rights that allow it to control...
-
Consider the following data: Required Use the above data to prepare the operating cash flow section of a consolidated statement of cash flows, using the indirect method. Consolidated net income.......

Study smarter with the SolutionInn App


