A simple ROT encryption can be used to obfuscate a string of characters by adding a...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
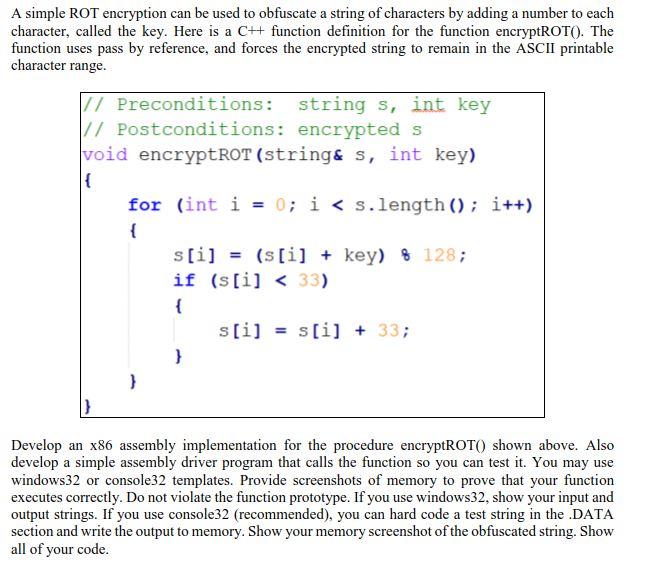
A simple ROT encryption can be used to obfuscate a string of characters by adding a number to each character, called the key. Here is a C++ function definition for the function encryptROT(). The function uses pass by reference, and forces the encrypted string to remain in the ASCII printable character range. // Preconditions: string s, int key // Postconditions: encrypted s void encryptROT (string & s, int key) { for (int i = 0; i < s.length(); i++) { s[i] (s[i] + key) 8 128; if (s[i] < 33) { } s[i] = s[i] + 33; Develop an x86 assembly implementation for the procedure encryptROT() shown above. Also develop a simple assembly driver program that calls the function so you can test it. You may use windows32 or console32 templates. Provide screenshots of memory to prove that your function executes correctly. Do not violate the function prototype. If you use windows32, show your input and output strings. If you use console32 (recommended), you can hard code a test string in the .DATA section and write the output to memory. Show your memory screenshot of the obfuscated string. Show all of your code. A simple ROT encryption can be used to obfuscate a string of characters by adding a number to each character, called the key. Here is a C++ function definition for the function encryptROT(). The function uses pass by reference, and forces the encrypted string to remain in the ASCII printable character range. // Preconditions: string s, int key // Postconditions: encrypted s void encryptROT (string & s, int key) { for (int i = 0; i < s.length(); i++) { s[i] (s[i] + key) 8 128; if (s[i] < 33) { } s[i] = s[i] + 33; Develop an x86 assembly implementation for the procedure encryptROT() shown above. Also develop a simple assembly driver program that calls the function so you can test it. You may use windows32 or console32 templates. Provide screenshots of memory to prove that your function executes correctly. Do not violate the function prototype. If you use windows32, show your input and output strings. If you use console32 (recommended), you can hard code a test string in the .DATA section and write the output to memory. Show your memory screenshot of the obfuscated string. Show all of your code.
Expert Answer:

Related Book For 

International Marketing And Export Management
ISBN: 9781292016924
8th Edition
Authors: Gerald Albaum , Alexander Josiassen , Edwin Duerr
Posted Date:
Students also viewed these programming questions
-
Design a Java class that represents a cache with a fixed size. It should support operations like add, retrieve, and remove, and it should evict the least recently used item when it reaches capacity.
-
Python and most Python libraries are free to download or use, though many users use Python through a paid service. Paid services help IT organizations manage the risks associated with the use of...
-
In Problems 1118, mentally solve each equation. 6x = -24
-
Heroes in movies hide beneath water and breathe through a hollow reed (villains never catch on to this trick). In practice, you cannot inhale in this manner if your lungs are more than 60.0 cm below...
-
North Star prepared the following unadjusted trial balance at the end of its second year of operations ending December 31, 2012. Other data not yet recorded at December 31, 2012: a. Rent expired...
-
What has been the effect of advances in artificial intelligence on the field of robotics?
-
The Seneca Childrens Fund (SCC) is a local charity that runs a summer camp for disadvantaged children. The funds board of directors has been working very hard over recent years to decrease the amount...
-
Techuxia Corporation worked on four jobs during October: Job A256, Job A257, Job A258, and Job A260. At the end of October, the job cost sheets for these jobs contained the following data: Job A256...
-
The 2021 income statement and the 2021 comparative balance sheet of Ghent River Camp, Inc., have just been distributed at a meeting of the camps board of directors. The directors raise a fundamental...
-
How do I make the submit, modify, and delete buttons work? I did the layout but need help in making action events. I also need help in making this GUI app using random access file. How do I do that? ...
-
Do you believe the federal government of Canada should limit the number ofimmigrants it accepts? https://globalnews.ca/news/5397306/canada--poll/immigration
-
How do you promoting the free exercise of speech and religion and resisting the forces of totalitarianism that seek to crush dissenting opinions and beliefs.
-
Write two or three paragraphs regarding what you have learned about the World Federation of the Deaf, its core values, mission, and especially why they are doing the International Week of Deaf.
-
Would you be comfortable having your father make such decisions about your life? What do you think of the idea?
-
Can you provide your own example of a proposition of policy using the topic of Cal state Northridge?
-
The end point of a titration involving the reaction of MnO, to Mn+ can be detected by the O a. Addition of an indicator like phenolphthalien O b. Use of litmus paper Oc. Purple color of the MnO,...
-
Assume that a trial balance is prepared with an account balance of $21,360 listed as $21,630 and an account balance of $1,500 listed as $15,000. Identify the transposition and the slide.
-
Is use of the Internet appropriate only for large companies? Explain.
-
Although licensing and contracting may appear to be desirable, they have drawbacks. What are the drawbacks?
-
The town of Verey, Switzerland, perches among the vineyards above Lake Geneva. Wealthy retirees take in Alpine vistas as they pass their afternoons strolling along the waterfront. The most exciting...
-
With your instructor's consent, identify a company and perform a background review of it to identify high-risk areas for an upcoming audit. Utilize all the electronic sources that have information...
-
CPA firms performing management consulting services can accept contingent fee contracts when: a. The amounts are not material in relationship to the audit billings. b. The consulting services are for...
-
Applying utilitarianism as a concept in addressing ethical situations requires the auditor to perform all of the following except: a. Identify the potential stakeholders that will be affected by the...

Study smarter with the SolutionInn App