a) Your computing system in your organizations has been infected by a piece of malicious code....
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
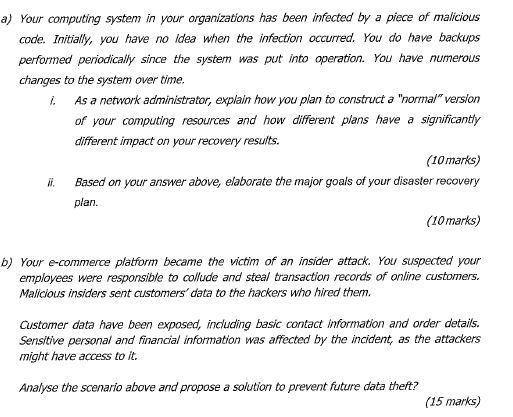
a) Your computing system in your organizations has been infected by a piece of malicious code. Initially, you have no idea when the infection occurred. You do have backups performed periodically since the system was put into operation. You have numerous changes to the system over time. ii. As a network administrator, explain how you plan to construct a "normal" version of your computing resources and how different plans have a significantly different impact on your recovery results. (10 marks) Based on your answer above, elaborate the major goals of your disaster recovery plan. (10 marks) b) Your e-commerce platform became the victim of an insider attack. You suspected your employees were responsible to collude and steal transaction records of online customers. Malicious insiders sent customers' data to the hackers who hired them. Customer data have been exposed, including basic contact information and order details. Sensitive personal and financial information was affected by the incident, as the attackers might have access to it. Analyse the scenario above and propose a solution to prevent future data theft? (15 marks) a) Your computing system in your organizations has been infected by a piece of malicious code. Initially, you have no idea when the infection occurred. You do have backups performed periodically since the system was put into operation. You have numerous changes to the system over time. ii. As a network administrator, explain how you plan to construct a "normal" version of your computing resources and how different plans have a significantly different impact on your recovery results. (10 marks) Based on your answer above, elaborate the major goals of your disaster recovery plan. (10 marks) b) Your e-commerce platform became the victim of an insider attack. You suspected your employees were responsible to collude and steal transaction records of online customers. Malicious insiders sent customers' data to the hackers who hired them. Customer data have been exposed, including basic contact information and order details. Sensitive personal and financial information was affected by the incident, as the attackers might have access to it. Analyse the scenario above and propose a solution to prevent future data theft? (15 marks)
Expert Answer:

Posted Date:
Students also viewed these programming questions
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
A man drops a stone from a high bridge and hears it strike the water below exactly 4 s later. (a) Estimate the distance to the water based on the assumption that the travel time for the sound to...
-
Moe, Johnny, and Raymond form a partnership and contribute the following assets: Johnnys building has a mortgage of $60,000, which the partnership assumes. a. Do any of the partners recognize any...
-
Write the structure of the principal organic product formed in the reaction of 1-propanol with each of the following reagents: (a) Sulfuric acid (catalytic amount), heat at 140C (b) Sulfuric acid...
-
Calculate \(\Delta G_{298}^{0}\) at 1 bar and \(298.15 \mathrm{~K}\) for the following reaction: \[ \mathrm{SO}_{2}(\mathrm{~g})+\frac{1}{2} \mathrm{O}_{2}(\mathrm{~g}) ightarrow...
-
Team Spirit Calendars imprints calendars with college names. The company has fixed expenses of $ 1,095,000 each month plus variable expenses of $ 6.50 per carton of calendars. Of the variable...
-
a) Figure 1 shows the curve y=x+4x and the x-axis. Find the area of the shaded region. y. y= x+4x Figure 1 Figure 2 2 y=6-x2 2 y=2 (5 marks) b) Figure 2 shows the shaded region bounded by the lines y...
-
Determine the amount of the equal monthly mortgage payment on a $450,000 30-year, fully amortizing mortgage, bearing interest at a fixed 6% rate, compounding monthly (payments are made at the...
-
What concerns about project implementation could impact the learning and development of human resources? Explain
-
A hospital has identified nonrandom variations in medical errors. These errors are directly related to patient falls. Draw a flow chart showing under what circumstances a patient might fall. Assume...
-
Look at agencies that offer hope on the various world problems that have been tackled, Tell about how that agency combats a problem that problem.
-
In a simple regression case, we have an equation for b that gives us 36.780 and the variable a gives us -118.532. They ask us: What are the possible sales for year 10 if advertising expenses were...
-
12. Anderson claims that the "code of the street is a kind of social exchange that allows for a certain order in the community." How does the "code" establish and maintain order? How does it erode or...
-
Brenda is a clerk-typist at Armor Industries, Inc., and she works in an office with nine other clerk-typists. The supervisor of the office is Joe. Brenda is a light-complexion, African American...
-
Transform the while loop from the previous exercise into an equivalent for loop (make sure it produces the same output).
-
What are a manager's resources?
-
What are the three levels of management?
-
This stagecoach likely makes a stop near you. Wells Fargo \& Company owns Wells Fargo Bank, which is one of the largest banks in the US with more than 8,800 bank branches in 40-plus states. Community...

Study smarter with the SolutionInn App

