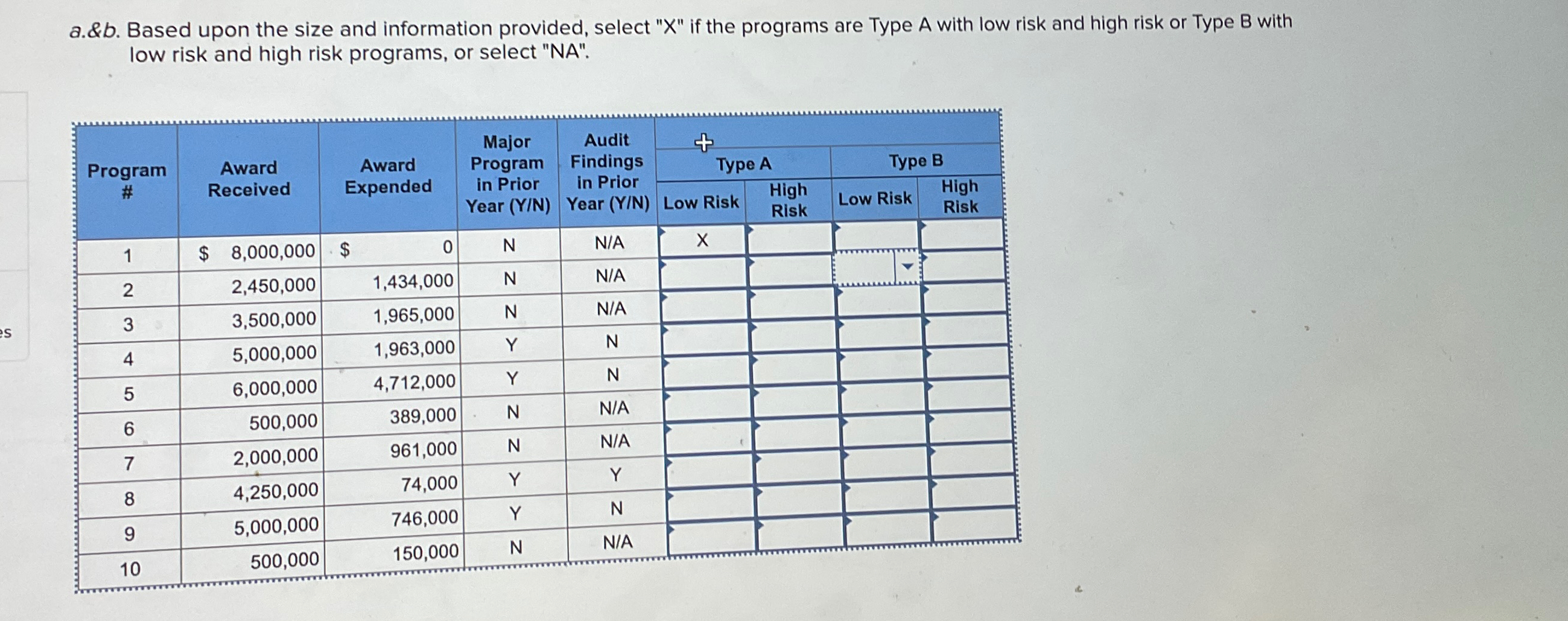
a.&b. Based upon the size and information provided, select X if the programs are Type A...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
a.&b. Based upon the size and information provided, select "X" if the programs are Type A with low risk and high risk or Type B with low risk and high risk programs, or select "NA". Program # Award Received Award Major Program Audit Findings + Type A Expended in Prior in Prior Year (Y/N) Year (Y/N) Low Risk High Risk Type B High Low Risk Risk 1 $ 8,000,000 $ 0 N N/A X 23 2,450,000 1,434,000 N N/A es 3,500,000 1,965,000 N N/A 4 5,000,000 1,963,000 Y N 5 6,000,000 4,712,000 Y N 6 500,000 389,000 N N/A 7 2,000,000 961,000 N N/A 8 4,250,000 74,000 Y Y 9 5,000,000 746,000 Y N 10 500,000 150,000 N N/A a.&b. Based upon the size and information provided, select "X" if the programs are Type A with low risk and high risk or Type B with low risk and high risk programs, or select "NA". Program # Award Received Award Major Program Audit Findings + Type A Expended in Prior in Prior Year (Y/N) Year (Y/N) Low Risk High Risk Type B High Low Risk Risk 1 $ 8,000,000 $ 0 N N/A X 23 2,450,000 1,434,000 N N/A es 3,500,000 1,965,000 N N/A 4 5,000,000 1,963,000 Y N 5 6,000,000 4,712,000 Y N 6 500,000 389,000 N N/A 7 2,000,000 961,000 N N/A 8 4,250,000 74,000 Y Y 9 5,000,000 746,000 Y N 10 500,000 150,000 N N/A
Expert Answer:

Posted Date:
Students also viewed these finance questions
-
Evaluate the limit of the sequence or state that it does not exist. an || 1 + 32n n
-
Consider an N-point sequence x[n] with DFT X[k], k = 0, 1, ?, N ? 1. The following algorithm computes the even-indexed DFT values X[k], k 0 , 2, ?. , N ? 2, for N even, using only a single N/2 ?point...
-
A vector v has initial point P = (0,-4,3) and terminal point Write Q = (6, -5, -1). Write v in the from v = ai + bj + ck.
-
This project demonstrates how Excel can be used to create a variety of useful documents for small businesses. a. Read the article A Do-It-Yourself Automated Invoicing System, by Jacob M. Rose, which...
-
Presented below are four independent situations. (a) On December 31, 2011, Beard Inc. sold computer equipment to Barber Co. and immediately leased it back for 10 years. The sales price of the...
-
Problem 11-13 Scenario Analysis (LO2) Consider the following scenario analysis: Scenario Recession Normal economy Boom Rate of Return Probability 0.20 Stocks Bonds -5% 19% 0.60 20% 10% 0.20 27% 4% a....
-
Questions 1- Choose: Relation which means eating at same table is called ............ in which one symbiont get benefits and cause no harm to host. A- Commensalism b- Mutualism c-...
-
What is an actuator? List various types of actuators.
-
What is a regulator?
-
How are upper and lower tolerance limits established for a design range?
-
What are some methods to mitigate risk during System Deployment?
-
How should a site survey be conducted?
-
a) You have been provided with Plate Count Agar that has 154 colonies on the plate. The agar plate was inoculated with 0.1ml of 10 -5 serial dilution of a pond water sample. Calculate the total...
-
Transform the while loop from the previous exercise into an equivalent for loop (make sure it produces the same output).
-
What are the advantages and disadvantages of biometric security devices, such as fingerprint readers, in comparison with other security measures such as passwords and locked doors?
-
Which preventive, detective, and/or corrective controls would best mitigate the following threats? a. An employees laptop was stolen at the airport. The laptop contained personally identifying...
-
EXCEL Problem Objective: learn how to protect spreadsheets. Required: a. Read the article Keeping Secrets: How to protect your computer from snoops and spies, by Theo Callahan in the July 2007 issue...

Study smarter with the SolutionInn App

