Accountants are often called upon to create an inventory of organizational risks. This may include items...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
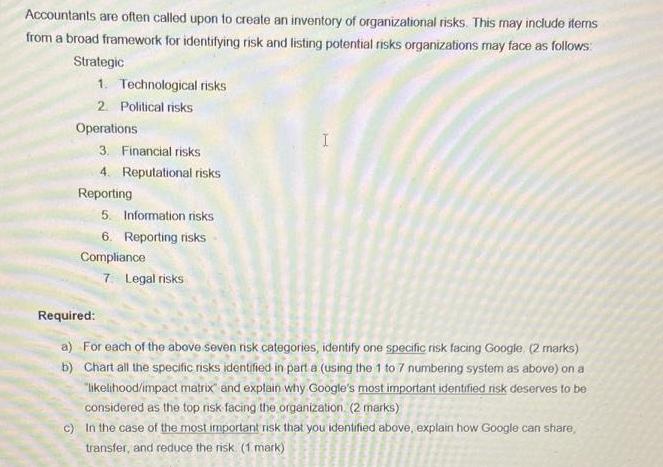
Accountants are often called upon to create an inventory of organizational risks. This may include items from a broad framework for identifying risk and listing potential risks organizations may face as follows: Strategic 1. Technological risks 2. Political risks Operations 3. Financial risks 4. Reputational risks Reporting 5. Information risks 6. Reporting risks Compliance 7 Legal risks I Required: b) a) For each of the above seven nsk categories, identify one specific risk facing Google (2 marks) Chart all the specific risks identified in part a (using the 1 to 7 numbering system as above) on a "likelihood/impact matrix and explain why Google's most important identified risk deserves to be considered as the top risk facing the organization (2 marks) c) In the case of the most important risk that you identified above, explain how Google can share, transfer, and reduce the risk (1 mark) Accountants are often called upon to create an inventory of organizational risks. This may include items from a broad framework for identifying risk and listing potential risks organizations may face as follows: Strategic 1. Technological risks 2. Political risks Operations 3. Financial risks 4. Reputational risks Reporting 5. Information risks 6. Reporting risks Compliance 7 Legal risks I Required: b) a) For each of the above seven nsk categories, identify one specific risk facing Google (2 marks) Chart all the specific risks identified in part a (using the 1 to 7 numbering system as above) on a "likelihood/impact matrix and explain why Google's most important identified risk deserves to be considered as the top risk facing the organization (2 marks) c) In the case of the most important risk that you identified above, explain how Google can share, transfer, and reduce the risk (1 mark)
Expert Answer:
Answer rating: 100% (QA)
Answer Required identify 2 3 0 Technical risks busines Any important harm to ... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these accounting questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Research various global financial services organizations (for example, UBS AG, E-Trade, Schwab, ING, Bank of America, HSBC, RBS) through their company websites and other publicly available...
-
A man drops a stone from a high bridge and hears it strike the water below exactly 4 s later. (a) Estimate the distance to the water based on the assumption that the travel time for the sound to...
-
Ninna Company manufactures wooden shelves. An accountant for Ninna just completed the variance report for the current month. After printing the report, his computers hard drive crashed, effectively...
-
Which of the following omissions best describes a corporate governance shortcoming of Zeros board of directors? The boards failure to: A. address the potential conflicts of interest between managing...
-
a. Longitudinal vibration of a bar b. Torsional vibration of a shaft c. Transverse vibration of a string \(c=\left(\frac{E}{ho} ight)^{1 / 2}\) Data:- \(c^{2} \frac{\partial^{2} w}{\partial...
-
1. George just hit the jackpot in Las Vegas and won $ 55,000! If he invests it now, at a 12% interest rate, how much will it be worth 15 years from now? 2. Zach would like to have $ 4,000,000 saved...
-
Explain PowerShell included in SQL Server 2008??????
-
A tennis ball is mounted on a spring that is suspended from a ceiling in John's dorm room. For entertainment, stress relief, boredom or just for a pure conversation piece, the tennis ball can be...
-
After the dosage of phenoxybenzamine was established, what was the goal of adding a low dose of ropranolol? What might have happened if Mrs. Ames had been given propranolol alone?
-
If, during a stride, the stretch causes her center of mass to lower by \(10 \mathrm{~mm}\), what is the stored energy? A. \(3.0 \mathrm{~J}\) B. \(6.0 \mathrm{~J}\) C. \(9.0 \mathrm{~J}\) D. \(12...
-
What is the present value of the following future amounts? a. $805 to be received 10 years from now discounted back to the present at 10 percent b. $376 to be received 5 years from now discounted...
-
At what annual rate would the following have to be invested? a. \($820\) to grow to \($1,988.12\) in 13 years b. \($320\) to grow to \($423.10\) in 6 years c. \($57\) to grow to \($290.30\) in 18...
-
An ideal gas is heated from \(25^{\circ} \mathrm{C}\) to \(145^{\circ} \mathrm{C}\). The mass of the gas is \(2 \mathrm{~kg}\). Determine: (i) specific heats, (ii) change in internal energy, (iii)...
-
Obaidullah Hamzah, who recently sold his Ford Mustang, placed $15,000 in a savings account paying annual compound interest of 7 percent. a. Calculate the amount of money that will be accrued if he...
-
How would a business grant accelerate your baking business if you had one and help you achieve your business goal/s? Please be as specific as possible
-
In the circuit shown in Figure 4, a battery supplies a constant voltage of 40 V, the inductance is 2 H, the resistance is 10, and l(0) = 0. (a) Find l(t). (b) Find the current after 0.1s.
-
Emphasize that the International Information Systems Security Certification Consortium (ISC)2 is considered the foremost organization offering information security certifications today.
-
I. Discuss the concept of deperimeterization and how it applies to information security. II. Emphasize the importance of remote access to systems and how COVID-19 accelerated the need for protected...
-
Discuss the BrewerNash Model, which is designed to prevent a conflict of interest between two parties. Point out that this model is sometimes known as a Chinese Wall.
-
Find the response of a simple pendulum numerically by solving the exact equation: \[\ddot{\theta}+\frac{g}{l} \sin \theta=0\] with \(\frac{g}{l}=0.01\) and plot the response, \(\theta(t)\), for \(0...
-
Using MATLAB function ode23, solve the differential equation \(5 \ddot{x}+4 \dot{x}+3 x=6 \sin t\) with \(x(0)=\dot{x}(0)=0\).
-
Find the response of a simple pendulum numerically by solving the nonlinear equation: \[\ddot{\theta}+\frac{g}{l}\left(\theta-\frac{\theta^{3}}{6} ight)=0\] with \(\frac{g}{l}=0.01\) and plot the...

Study smarter with the SolutionInn App


