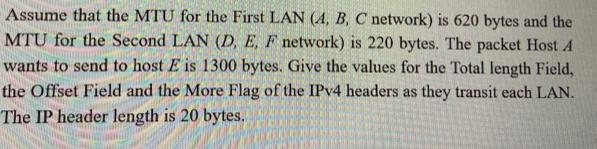
Assume that the MTU for the First LAN (A, B, C network) is 620 bytes and...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
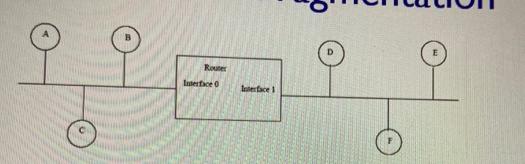
Assume that the MTU for the First LAN (A, B, C network) is 620 bytes and the MTU for the Second LAN (D, E, F network) is 220 bytes. The packet Host A wants to send to host E is 1300 bytes. Give the values for the Total length Field, the Offset Field and the More Flag of the IPv4 headers as they transit each LAN. The IP header length is 20 bytes. Router Interface 0 Interface 1 Assume that the MTU for the First LAN (A, B, C network) is 620 bytes and the MTU for the Second LAN (D, E, F network) is 220 bytes. The packet Host A wants to send to host E is 1300 bytes. Give the values for the Total length Field, the Offset Field and the More Flag of the IPv4 headers as they transit each LAN. The IP header length is 20 bytes. Router Interface 0 Interface 1
Expert Answer:
Answer rating: 100% (QA)
As the packet travels from Host A to Host E it will need to be fragmented t... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these computer network questions
-
A pension fund manager is considering three mutual funds. The first is a stock fund, the second is a long-term government and corporate bond fund, and the third is a T- bill money market fund that...
-
KYC's stock price can go up by 15 percent every year, or down by 10 percent. Both outcomes are equally likely. The risk free rate is 5 percent, and the current stock price of KYC is 100. (a) Price a...
-
A text editor such as pico can be used to write a program in C language in Unix environment. The program will have to be compiled in accordance to C compilation model before it can be executed. (a)...
-
Solve each of the linear systems in Problems 13 through 20 to determine whether the critical point (0, 0) is stable, asymptotically stable, or unstable. Use a computer system or graphing calculator...
-
According to an article in the New York Times on August 9, 2008, economists were predicting that the average interest rate for a 30-year mortgage would increase from 6.7% to 7.1% during the next year...
-
Suppose nation A can produce 80 units of X by using all its resources to produce X or 60 units of Y devoting all its resources to Y. Comparable figures for nation B are 60 units of X and 60 units of...
-
What is machine learning and why do organizations use it?
-
Wichitas famous Sethi Restaurant is open 24 hours a day. Servers report for duty at 3 a. m., 7 a. m., 11 a. m., 3 p. m., 7 p. m., or 11 p. m., and each works an 8- hour shift. The following table...
-
Using the rules for adding capacitors in series and parallel, compare the measurements of the individual capacitors to the capacitors in series and in parallel for both methods (for the time constant...
-
This problem continues the process of preparing the Kipley Company's Employee Payroll Register for the pay period ending January 8th, 20--. In previous chapters, gross wages were computed for each...
-
De Beers has five potential customers: Raquel, Jackie, Joan, Mia, and Sophia. Each of these customers will buy at most one diamond-and only if the price is just equal to, or lower than, her...
-
What is a class action and when do parties use them?
-
What is the origin of the word tort, and what does it mean?
-
What is the purpose of environmental impact assessment review?
-
Why is the determination of the relevant market essential to the application of competition law?
-
What is the main justification for the principle of vicarious liability?
-
Which of the following is not feature of Perfect Competition? A . Firm is a price maker B . Free entry and exit C . Perfect knowledge of the market conditions to buyers and sellers D . Large number...
-
Determine whether the lines are parallel, perpendicular, or neither. 2x + 3y = -12, 2y - 3x = 8
-
Suppose Bob initiates a TCP connection to Trudy who is pretending to be Alice. During the handshake, Trudy sends Bob Alice's certificate. In what step of the SSL handshake algorithm will Bob discover...
-
Consider the previous problem, but suppose that D has the value a. 1001000101. b. 1010001111 . c. 0101010101.
-
In this problem. we are interested in finding out the efficiency of a BitTorrent- like P2P file sharing system . Consider two peers Bob and Alice. They join a torrent with M peers in total (including...
-
According to the monetary approach to the balance of payments, what type of economic policies would help a country resolve a balance of trade deficit?
-
We discussed risk aversion as being descriptive of investor behavior. Can Do you think of any real-world behavior that you might consider to be evidence of the existence of risk preferrers?
-
Pick three developing countries and create a country risk index for them. Rank them ordinally in terms of factors that you can observe (exports, GDP growth, reserves, etc.) by looking at...

Study smarter with the SolutionInn App


