Authentication is completed when the sender Multiple Choice use the sender's public key to successfuly decrypt...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
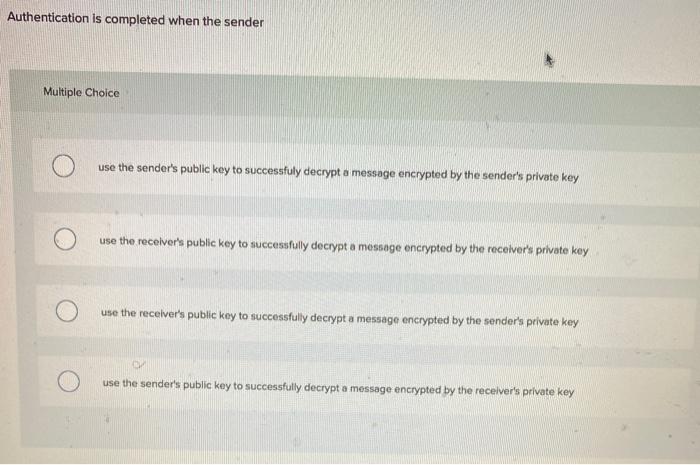
Authentication is completed when the sender Multiple Choice use the sender's public key to successfuly decrypt a message encrypted by the sender's private key use the receiver's public key to successfully decrypt a message encrypted by the receiver's private key use the receiver's public key to successfully decrypt a message encrypted by the sender's private key use the sender's public key to successfully decrypt a message encrypted by the receiver's private key Authentication is completed when the sender Multiple Choice use the sender's public key to successfuly decrypt a message encrypted by the sender's private key use the receiver's public key to successfully decrypt a message encrypted by the receiver's private key use the receiver's public key to successfully decrypt a message encrypted by the sender's private key use the sender's public key to successfully decrypt a message encrypted by the receiver's private key
Expert Answer:
Answer rating: 100% (QA)
The detailed answer for the above question is provided below The correct answer is use th... View the full answer

Related Book For 

Posted Date:
Students also viewed these accounting questions
-
The chapter described how public key authentication is used for message-by-message authentication in digital signatures. However, public key authentication is widely used for initial authentication....
-
The Coded message the follows is an encrypted message from Brutus to the Roman Senate. It was produced using the Caesar cipher method, in which each letter is shifted by a fixed number of places...
-
The coded message that follows is an encrypted message from Brutus to the Roman Senate. It was produced using the Caesar cipher method, in which each letter is shifted by a fixed number of places...
-
Suppose that \(\mathrm{x}\) is a linked-list Node. What is the effect of the following code fragment? \(t\). next \(=x\). next; \(x \cdot\) next \(=t ;\)
-
Situation Gilmatt Company developed a new product that it planned to sell directly to customers and to promote heavily because of stiff competition in the market place. Its marketing department did...
-
Sulfur is formed in volcanic gases when sulfur dioxide reacts with hydrogen sulfide. The same reaction has been proposed as a method of removing sulfur dioxide from the gases emitted from coal-fired...
-
Question: Donald Waide had a contracting business. He bought most of his supplies from Paul Bingham's supply center. Waide fell behind on his bills, and Bingham told Waide that he would extend no...
-
Musixscore.com is an online service providing sheet music to customers. On the browse music Web page, customers select a genre of music from a drop-down list. The Web page uses Ajax to obtain a list...
-
Problem 2 The controller of PenPen Company is attempting to determine the amount of cash to be reported on its December 31, 2019 balance sheet. The following information is provided: a. Commercial...
-
Spring Manufacturing Company makes two components identified as C12 and D57. Selected budgetary data for 2022 follow: The firm expects the average wage rate to be $25 per hour in 2022. Spring...
-
Tony's Trinkets wants to enter a foreign market but does not understand the culture. What entry technique should Tony's Trinkets use? Report an Error Licensing Direct investment Joint venture...
-
Find the probability that x > 56.
-
X ~ N(4, 5) Find the maximum of x in the bottom quartile.
-
X ~ N(6, 2) Find the probability that x is between three and nine.
-
Visit the International City/County Management Association and the CompassPoint Nonprofi t websites. What kinds of professional development programs are available through those organizations? Which...
-
What guides your behavior now? Will you use one of the ethical guides from the text? If yes, which one and why?
-
Diversifiable risk, also known as unsystematic risk, is defined as firm-specific risk and hence impacts the price of that individual stock rather than affecting the whole industry or sector in which...
-
Read the following description and Write a response of it. The discretion of public administrators can be decreased, but not altogether eliminated. Officials will use their discretion in any given...
-
a) Why must you know a server's role to know how to protect it? b) Why is it important to minimize both main applications and subsidiary applications? c) Why are security baselines needed for...
-
The ACL in Figure 6-10 is in effect. A packet containing a TCP ACK segment reaches a stateful packet inspection firewall from the outside. What actions will the SPI firewall take? Explain.
-
A company is warned by its credit card companies that it will be classified as a high-risk firm unless it immediately reduces the number of fraudulent purchases made by its e-commerce clients. Come...
-
List three classes of short-term liability and two classes of long-term liability that will appear in the typical balance sheet.
-
Why is the matching principle important when preparing a profit and loss account and balance sheet?
-
What do you understand by Cronhelm's additivity principle and why does this prin- ciple tend to lead to the understatement of the net asset value of a company as shown in its balance sheet?

Study smarter with the SolutionInn App


