b. TCP connections are full-duplex. This means that the two endpoints can each transmit data over...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
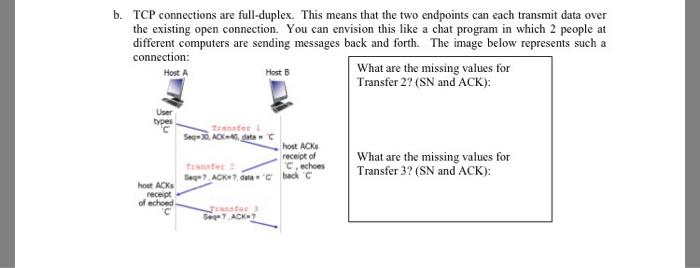
b. TCP connections are full-duplex. This means that the two endpoints can each transmit data over the existing open connection. You can envision this like a chat program in which 2 people at different computers are sending messages back and forth. The image below represents such a connection: Host A Host B What are the missing values for Transfer 2? (SN and ACK): User types host ACKS receipt of echoed. Transfer 1 Seq-30, ACX-40, Transfer host ACKS receipt of 'C, echoes Seg? ACK?, data C back C Transfor 3 Sea-7,ACK-7 What are the missing values for Transfer 3? (SN and ACK): b. TCP connections are full-duplex. This means that the two endpoints can each transmit data over the existing open connection. You can envision this like a chat program in which 2 people at different computers are sending messages back and forth. The image below represents such a connection: Host A Host B What are the missing values for Transfer 2? (SN and ACK): User types host ACKS receipt of echoed. Transfer 1 Seq-30, ACX-40, Transfer host ACKS receipt of 'C, echoes Seg? ACK?, data C back C Transfor 3 Sea-7,ACK-7 What are the missing values for Transfer 3? (SN and ACK):
Expert Answer:

Related Book For 

Corporate Finance
ISBN: 978-0077861759
10th edition
Authors: Stephen Ross, Randolph Westerfield, Jeffrey Jaffe
Posted Date:
Students also viewed these programming questions
-
Python and most Python libraries are free to download or use, though many users use Python through a paid service. Paid services help IT organizations manage the risks associated with the use of...
-
the Q question 1)Building a MultiThreaded Web Server In this lab we will develop a Web server in two steps. In the end, you will have built a multithreaded Web server that is capable of processing...
-
Use the percentages in Figure 7.3 and the values in Figure 7.4 to answer the following questions: What percentage of SAT takers score between 500 and 600? Figure 7.3 Normal Curve Percentages, to Two...
-
In December 2013, Carl Corporation sold land it held as an investment. The corporation received $50,000 in 2013 and a note payable (with adequate interest) for $150,000 to be paid in 2015. Carl...
-
If 500 newborns are screened at the inner-city hospital, then what is the exact binomial probability of exactly 5 HIV-positive test results? Infectious Disease Newborns were screened for human...
-
A spurious relationship occurs when two independent variables are incorrectly identified as being related. A simple test of independence is based on the estimated correlation coefficient,...
-
Use the constant-growth model (Gordon growth model) to find the value of each firm shown in the following table. Required return Dividend growth rate 8% Dividend expected next year $1.20 4.00 0.65...
-
Here my is papr i have gathered information help expand more the questions to papr 5 pg. Our coffee shop chain expansion plan is comprehensively designed to enhance productivity, improve competitive...
-
1. What is the cost of debt for Sunrise Bakery? 2. What is their cost of equity? 3. What is the WACC? 4. Which cost of capital should be used to evaluate the feasibility of the oven purchase? 5....
-
Consider a chain of processes P1, P2, .., Pn implementing a multi-tiered Client/Server architecture. Process Pi is the client of process Pi+1 and Pi will return a reply to Pi-1 only after receiving a...
-
Consider a regulators objective formulized as: (a) Show that at most one of the four constraints (incentive compatibility and participation) can be binding in this case, that the high cost firms fee...
-
Add code to Merge to produce a trace like the following: % java Merge < tiny.txt was had him and you his the but had was and him and had him was his you but the but his the you and but had him his...
-
Write a program that takes the name of an image file as a command-line argument and applies a glass filter: set each pixel \(p\) to the color of a random neighboring pixel (whose pixel coordinates...
-
Implement the method contains() for HashST.
-
Use tilde notation to simplify each of the following formulas, and give the order of growth of each: a. \(n(n-1)(n-2)(n-3) / 24\) b. \((n-2)(\lg n-2)(\lg n+2)\) c. \(n(n+1)-n^{2}\) d. \(n(n+1) / 2+n...
-
Westcock Shipbuilding Ltd. has a December 31 year end. On January 1, 2017, the company had the following shareholder's equity accounts. Preferred shares, $4 non-cumulative, unlimited number...
-
A Bloomberg Businessweek subscriber study asked, In the past 12 months, when traveling for business, what type of airline ticket did you purchase most often? A second question asked if the type of...
-
The Morgan Corporation has two different bonds currently outstanding. Bond M has a face value of $30,000 and matures in 20 years. The bond makes no payments for the first six years, then pays $800...
-
Explain why diversification per se is probably not a good reason for merger.
-
If a firm is buying call options on pork belly futures as a hedging strategy, what must be true about the firms exposure to pork belly prices?
-
List eight environmental quality control elements audit firms should implement to help ensure that high quality audits are performed by the firm.
-
Describe briefly the key features of the Joint Monitoring Unit's monitoring process.
-
List six factors of the law relating to the liability of auditors to third parties that have emerged from cases settled subsequent to the Caparo decision, and identify the common theme that can be...

Study smarter with the SolutionInn App