? (2) Alice and Bob has designed a public key cryptosystem based on the ElGamal. Bob has
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
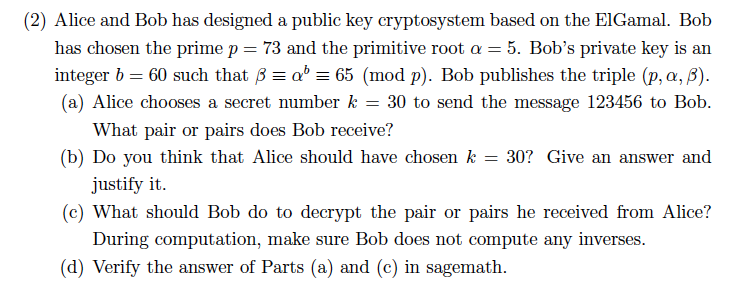
(2) Alice and Bob has designed a public key cryptosystem based on the ElGamal. Bob has chosen the prime p = 73 and the primitive root a = 5. Bob's private key is an integer b = 60 such that ß = a¹ = 65 (mod p). Bob publishes the triple (p, a, ß). (a) Alice chooses a secret number k = 30 to send the message 123456 to Bob. What pair or pairs does Bob receive? (b) Do you think that Alice should have chosen k = 30? Give an answer and justify it. (c) What should Bob do to decrypt the pair or pairs he received from Alice? During computation, make sure Bob does not compute any inverses. (d) Verify the answer of Parts (a) and (c) in sagemath. (2) Alice and Bob has designed a public key cryptosystem based on the ElGamal. Bob has chosen the prime p = 73 and the primitive root a = 5. Bob's private key is an integer b = 60 such that ß = a¹ = 65 (mod p). Bob publishes the triple (p, a, ß). (a) Alice chooses a secret number k = 30 to send the message 123456 to Bob. What pair or pairs does Bob receive? (b) Do you think that Alice should have chosen k = 30? Give an answer and justify it. (c) What should Bob do to decrypt the pair or pairs he received from Alice? During computation, make sure Bob does not compute any inverses. (d) Verify the answer of Parts (a) and (c) in sagemath.
Expert Answer:
Answer rating: 100% (QA)
a Bob receives the pair 55 8 956 Alices message is 123456 She computes 55 530 mod 73 and 8956 7330 m... View the full answer

Related Book For 

Posted Date:
Students also viewed these mathematics questions
-
Using the RSA public key cryptosystem, with a = 1, b = 2, etc., a. If p = 7 and q = 11, list five legal values for d. b. If p = 13, q = 31, and d = 7, find e. c. Using p = 5, q = 11, and d = 27, find...
-
Using the RSA public key cryptosystem, with a = 1, b = 2 . . . y = 25, z = 26. (a) If p = 5 and q = 13, list five legal values for d. (b) If p = 5, q = 31, and d = 37, find e. (c) Using p = 3, q =...
-
1. Distinguish change management from change leadership? 2. Discuss competencies required by person oriented and task oriented leadership behaviors. 3. With the use of examples explain how change can...
-
1. how transfer pricing can be used to minimize taxes in a multinational corporation. Include a short numerical illustration. 2. wHAT are the arguments for and against the international convergence...
-
Describe the four elements in a SWOT analysis.
-
How did Galleon Investment Group consistently achieve above-market returns?
-
In a single stage impulse turbine, nozzle angle is \(20^{\circ}\) and blade angles are equal. The velocity coefficient for blades is 0.85 . calculate the maximum blade efficiency possible. If the...
-
A satisfied customer is the most important goal of this company! was the opening remark of the corporate president, Alice Nunes, at the monthly executive committee meeting of Santiago Company. The...
-
A boat (with a flat bottom) and its cargo weigh 5,200 N. The area of the boat's bottom is 8 m 2 . How far below the surface of the water is the boat's bottom when it is floating in water? Answer in...
-
Jackie Wengler, owner of Wengler Home Decorating Service, has requested that you prepare from the following balances (a) An income statement for June 201X, (b) A statement of owner?s equity for June,...
-
IE is the amount of energy required to remove the outermost electron from an atom to create a positive ion. Electrons are always removed from an atom/ion one at a time and so most atoms (all except...
-
When considering all of the parts of the balance of payments for a nation, what item might you want to look at to determine if a nation has a trade surplus or deficit?
-
1. How do the risks associated with network systems compare with the risks associated with centralized IT functions? 2. What is the relationship between tolerable misstatement, inherent risk, and...
-
Assume you are interested in assessing how soon a company might need to make significant capital expenditures to replace property, plant, and equipment. What financial statement ratio would you use...
-
Emergency procedures, protective equipment, and proper methods of containment and cleanup are listed under what is the section of the Safety Data Sheet?
-
Below is the balance sheet that you prepared for JB Hi-Fi as at 30 June 2022, as part of the tutorial activity discussed in week 2. All numbers are in millions of Australian Dollars. JB Hi-Fi Balance...
-
2. Calculate: (a) 10101111+11011011 (b) 00001101+00000111 (c) A49+6BD
-
Wilsons Auto Repair ended 2011 with Accounts Receivable of $85,000 and a credit balance in Allowance for Uncollectible Accounts balance of $11,000. During 2012, Wilsons Auto Repair had the following...
-
John wants to have an original domain name and uses a randomized program to generate a secondary domain name for him. He wants to register this domain name in the com generic domain. The domain name...
-
Multiplexing STS-1 multiple data streams, called tributaries, plays an important role in SONET. A 3:1 multiplexer multiplexes three input STS-1 tributaries onto one output STS-3 stream. This...
-
Figure 4-24 shows several physical layer protocols. Which of these is closest to the Bluetooth physical layer protocol? What is the biggest difference between the two? Figure 4-24 Upper layers...
-
Input the other metrics from the individual tax returns (e.g., income from wages and salaries, interest earned, and estimated tax payments). a. Review the dollars horizontally across the three years...
-
Input the IRS Schedules C from the 20132015 income tax returns into a spreadsheet. a. Add percent columns to the right of dollar column for each year. b. Calculate common-sized percentages in the...
-
Go to a business library or university librarian and locate RMA Annual Financial Statement Studies or a similar publication and locate convenience stores and comparable ratios (e.g., cost of goods...

Study smarter with the SolutionInn App


