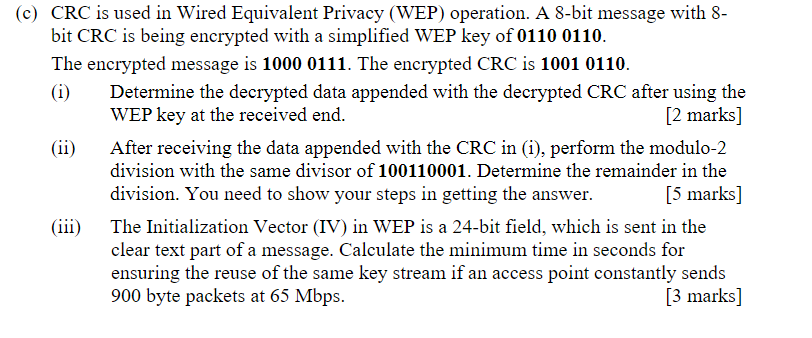
(c) CRC is used in Wired Equivalent Privacy (WEP) operation. A 8-bit message with 8- bit...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
(c) CRC is used in Wired Equivalent Privacy (WEP) operation. A 8-bit message with 8- bit CRC is being encrypted with a simplified WEP key of 0110 0110. The encrypted message is 1000 0111. The encrypted CRC is 1001 0110. (i) (ii) (iii) Determine the decrypted data appended with the decrypted CRC after using the WEP key at the received end. [2 marks] After receiving the data appended with the CRC in (i), perform the modulo-2 division with the same divisor of 100110001. Determine the remainder in the division. You need to show your steps in getting the answer. [5 marks] The Initialization Vector (IV) in WEP is a 24-bit field, which is sent in the clear text part of a message. Calculate the minimum time in seconds for ensuring the reuse of the same key stream if an access point constantly sends 900 byte packets at 65 Mbps. [3 marks] (c) CRC is used in Wired Equivalent Privacy (WEP) operation. A 8-bit message with 8- bit CRC is being encrypted with a simplified WEP key of 0110 0110. The encrypted message is 1000 0111. The encrypted CRC is 1001 0110. (i) (ii) (iii) Determine the decrypted data appended with the decrypted CRC after using the WEP key at the received end. [2 marks] After receiving the data appended with the CRC in (i), perform the modulo-2 division with the same divisor of 100110001. Determine the remainder in the division. You need to show your steps in getting the answer. [5 marks] The Initialization Vector (IV) in WEP is a 24-bit field, which is sent in the clear text part of a message. Calculate the minimum time in seconds for ensuring the reuse of the same key stream if an access point constantly sends 900 byte packets at 65 Mbps. [3 marks]
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
"internet radios" for streaming audio, and personal video recorders and players. Describe design and evaluation processes that could be used by a start-up company to improve the usability of such...
-
obias is a foreman at a factory that manufactures auto parts. When a health a safety inspector visits the plant, Tobias notices the inspector writing down several major labor and safety violations....
-
Suppose the current zero-coupon yield curve for risk-free bonds is as follows: a. What is the price per $100 face value of a two-year, zero-coupon, risk-free bond? b. What is the price per $100 face...
-
Environs Inc. is an architectural firm that designs commercial and business buildings. SAMS Hotel Group LLC signed a contract with Environs, under which Environs would provide architectural services...
-
Priscilla Webster was dining at her favorite Massachusetts seafood restaurant when matters went horribly wrong. She began choking on a fishbone that had been lurking in her seafood chowder. After a...
-
Gold Star Rice, Ltd., of Thailand exports Thai rice throughout Asia. The company grows three varieties of riceFragrant, White, and Loonzain. (The currency in Thailand is the baht. which is denoted by...
-
A student performs a double-slit experiment using two slits spaced 0.20 mm apart and located 1.50 m from the screen. The monochromatic light source creates an interference pattern in which the...
-
7. Uneven CF streams You are evaluating a proposed project for your company. The project is expected to generate the following end-of-year cash flows: -$3,000 0 -$147.53 O $115.38 O-$71.99 O-$22.97...
-
Demand is external to the supply chain and thus is most uncertain in the manufacturing cycle. replenishment cycle. customer order cycle. procurement cycle.
-
The objective of customer order entry is to get the correct orders to customers by the promised due date at the lowest possible cost. maintain a record of the product receipt and to complete a...
-
List the five basic steps of demand forecasting in supply chain management. Which step is more important?
-
One of the characteristics of forecasts is aggregate forecasts are usually more accurate than disaggregate forecasts. disaggregate forecasts are usually more accurate than aggregate forecasts....
-
When designing a regional network configuration, the first step is to meet with all regional managers. the first step is to collect the data in a form that can be used for a quantitative model. the...
-
LILI SDN BHD is a manufacturer and supplier of home cabinets. It has two main Departments that is the Production Department and the Service Department. The Production department has three (3)...
-
As water moves through the hydrologic cycle, water quality changes are common because of natural phenomena or anthropogenic pollution. Using Figure 11.1, describe how water-quality changes occur...
-
A study claims that all adults spend an average of 14 hours or more on chores during a weekend. A researcher wanted to check if this claim is true. A random sample of 200 adults taken by this...
-
Refer to Exercise 6.98. In that exercise, suppose the mean is set to be 8 ounces, but the standard deviation is unknown. The cups used in the machine can hold up to 8.2 ounces, but these cups will...
-
A 20102011 poll conducted by Gallup, (www.gallup.com/poll/148994/Emotional-Health Higher- Among-Older-Americans.aspx) examined the emotional health of a large number of Americans. Among other things,...
-
Go to http://management.about.com/lr/project_time_ management/174690/1/ and click on Project Management on the left side of the screen. When you consider several of the articles on time management in...
-
Consider the following information that you have compiled regarding the steps needed to complete a project. You have identified all relevant steps and have made some determinations regarding...
-
Key in a search with the prompt projects in in which you select a country of interest (e.g., projects in Finland). Many of the projects generated by such a search are government-sponsored...

Study smarter with the SolutionInn App