C++ I need help asap! 2. Suspicious Activity From Logs Application logs are useful in analyzing interaction
Fantastic news! We've Found the answer you've been seeking!
Question:
C++ I need help asap!
Transcribed Image Text:
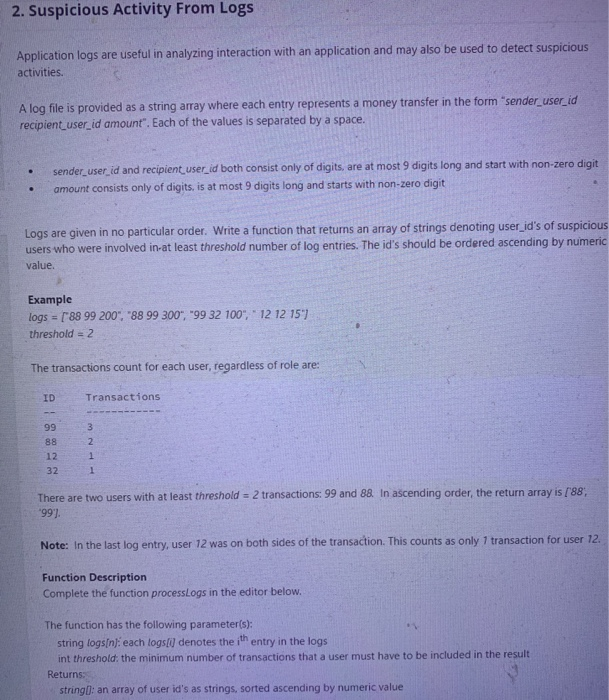
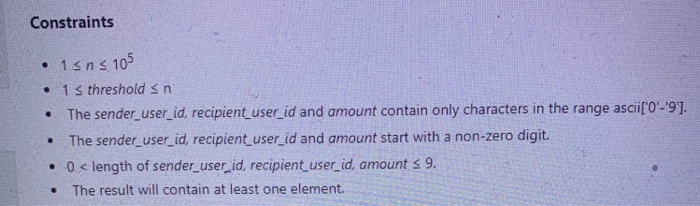
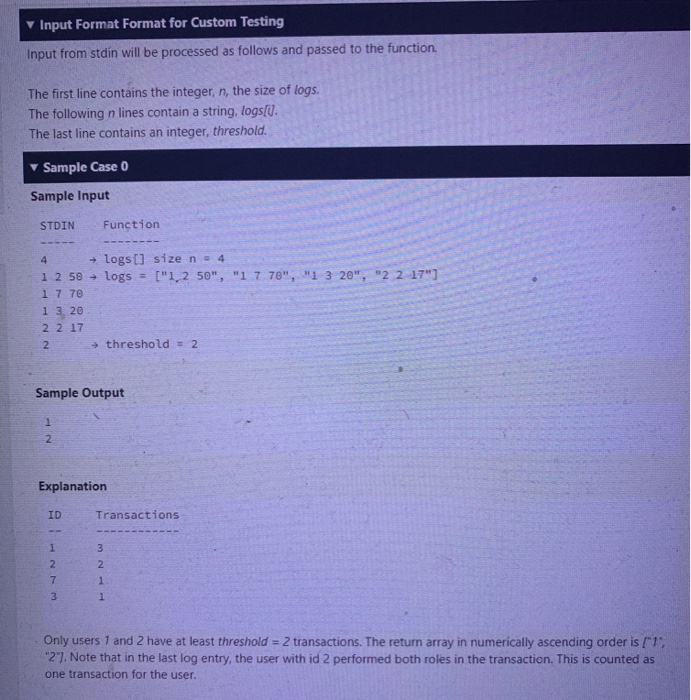
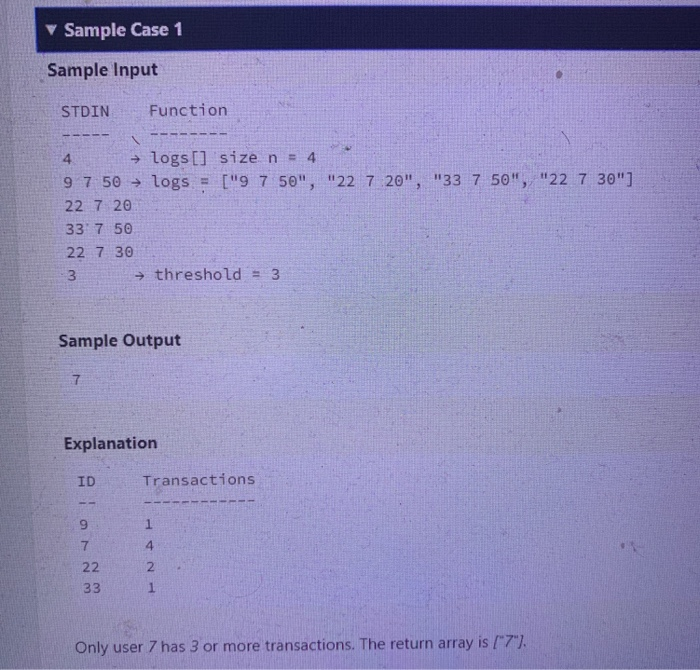
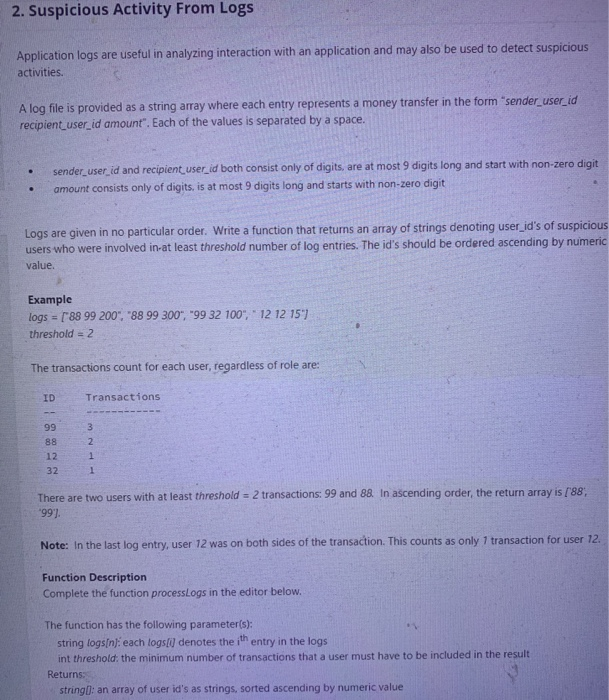
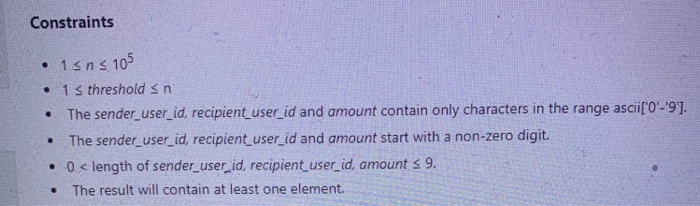
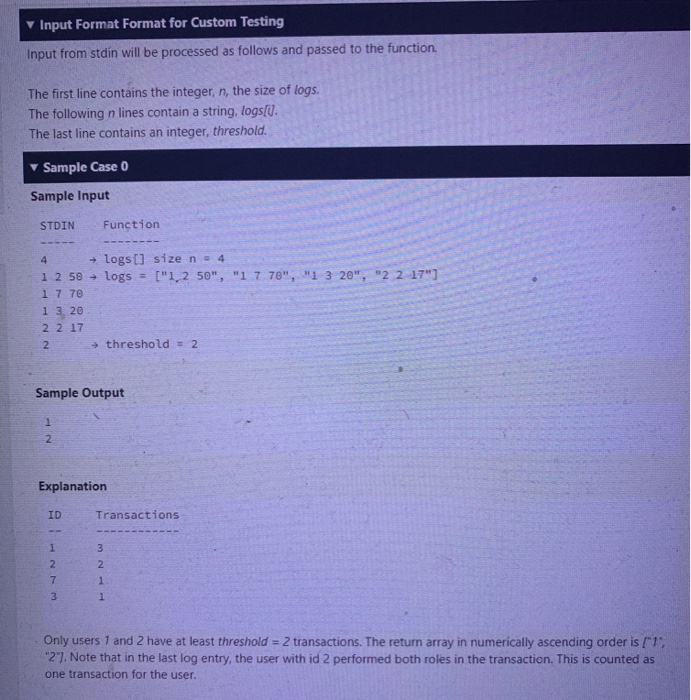
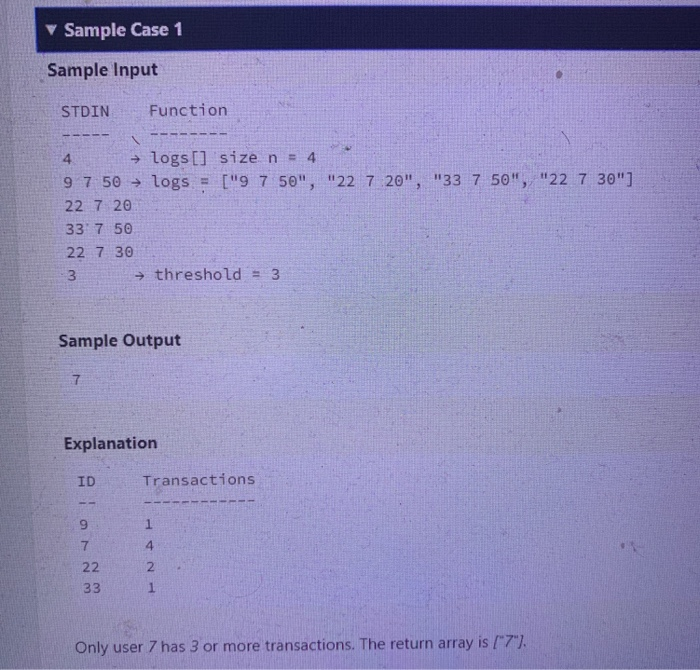
2. Suspicious Activity From Logs Application logs are useful in analyzing interaction with an application and may also be used to detect suspicious activities. A log file is provided as a string array where each entry represents a money transfer in the form sender_user_id recipient_user_id amount . Each of the values is separated by a space. . . sender_user_id and recipient_user_id both consist only of digits, are at most 9 digits long and start with non-zero digit amount consists only of digits, is at most 9 digits long and starts with non-zero digit Logs are given in no particular order. Write a function that returns an array of strings denoting user_id s of suspicious users who were involved in-at least threshold number of log entries. The id s should be ordered ascending by numeric value. Example logs = [ 88 99 200 , 88 99 300 , 99 32 100 , 12 12 151 threshold = 2 The transactions count for each user, regardless of role are: ID 99 88 12 32 Transactions 3 2 1 1 There are two users with at least threshold = 2 transactions: 99 and 88. In ascending order, the return array is [ 88, 99 ]. Note: In the last log entry, user 12 was on both sides of the transaction. This counts as only 1 transaction for user 12. Function Description Complete the function processLogs in the editor below. The function has the following parameter(s): string logs[n]: each logs[i] denotes the ith entry in the logs int threshold: the minimum number of transactions that a user must have to be included in the result Returns: string]: an array of user id s as strings, sorted ascending by numeric value Constraints • 1 ≤ n ≤ 105 • . . ● 1 ≤ threshold ≤ n The sender_user_id, recipient_user_id and amount contain only characters in the range ascii[ 0 - 9 ]. The sender_user_id, recipient_user_id and amount start with a non-zero digit. 0 length of sender_user_id, recipient_user_id, amount ≤ 9. < The result will contain at least one element. ▾ Input Format Format for Custom Testing Input from stdin will be processed as follows and passed to the function. The first line contains the integer, n, the size of logs. The following n lines contain a string, logs[i]. The last line contains an integer, threshold. ▾ Sample Case 0 Sample Input STDIN ---- 4 1 2 50- 1 7 70 13, 20 22 17 2 1 2 Function →logs [] size n = 4 logs = [ 1,2 50 , 1 7 70 , 1 3 20 , 2 2 17 ] Sample Output ID @22713 Explanation threshold = 2 Transactions 3 2 1. 1 Only users 1 and 2 have at least threshold = 2 transactions. The return array in numerically ascending order is [ 1 , 2 ]. Note that in the last log entry, the user with id 2 performed both roles in the transaction. This is counted as one transaction for the user. Sample Case 1 Sample Input STDIN ‒‒‒‒- 4 →logs [] size n = 4 9 7 50 logs = [ 9 7 50 , 22 7 20 , 33 7 50 , 22 7 30 ] 22 7 20 33 7 50 22 7 30 3 7 Sample Output ID Function Explanation -- 9 → threshold = 3 7 22 33 Transactions 1 4 2 Only user 7 has 3 or more transactions. The return array is [ 7 ]. 2. Suspicious Activity From Logs Application logs are useful in analyzing interaction with an application and may also be used to detect suspicious activities. A log file is provided as a string array where each entry represents a money transfer in the form sender_user_id recipient_user_id amount . Each of the values is separated by a space. . . sender_user_id and recipient_user_id both consist only of digits, are at most 9 digits long and start with non-zero digit amount consists only of digits, is at most 9 digits long and starts with non-zero digit Logs are given in no particular order. Write a function that returns an array of strings denoting user_id s of suspicious users who were involved in-at least threshold number of log entries. The id s should be ordered ascending by numeric value. Example logs = [ 88 99 200 , 88 99 300 , 99 32 100 , 12 12 151 threshold = 2 The transactions count for each user, regardless of role are: ID 99 88 12 32 Transactions 3 2 1 1 There are two users with at least threshold = 2 transactions: 99 and 88. In ascending order, the return array is [ 88, 99 ]. Note: In the last log entry, user 12 was on both sides of the transaction. This counts as only 1 transaction for user 12. Function Description Complete the function processLogs in the editor below. The function has the following parameter(s): string logs[n]: each logs[i] denotes the ith entry in the logs int threshold: the minimum number of transactions that a user must have to be included in the result Returns: string]: an array of user id s as strings, sorted ascending by numeric value Constraints • 1 ≤ n ≤ 105 • . . ● 1 ≤ threshold ≤ n The sender_user_id, recipient_user_id and amount contain only characters in the range ascii[ 0 - 9 ]. The sender_user_id, recipient_user_id and amount start with a non-zero digit. 0 length of sender_user_id, recipient_user_id, amount ≤ 9. < The result will contain at least one element. ▾ Input Format Format for Custom Testing Input from stdin will be processed as follows and passed to the function. The first line contains the integer, n, the size of logs. The following n lines contain a string, logs[i]. The last line contains an integer, threshold. ▾ Sample Case 0 Sample Input STDIN ---- 4 1 2 50- 1 7 70 13, 20 22 17 2 1 2 Function →logs [] size n = 4 logs = [ 1,2 50 , 1 7 70 , 1 3 20 , 2 2 17 ] Sample Output ID @22713 Explanation threshold = 2 Transactions 3 2 1. 1 Only users 1 and 2 have at least threshold = 2 transactions. The return array in numerically ascending order is [ 1 , 2 ]. Note that in the last log entry, the user with id 2 performed both roles in the transaction. This is counted as one transaction for the user. Sample Case 1 Sample Input STDIN ‒‒‒‒- 4 →logs [] size n = 4 9 7 50 logs = [ 9 7 50 , 22 7 20 , 33 7 50 , 22 7 30 ] 22 7 20 33 7 50 22 7 30 3 7 Sample Output ID Function Explanation -- 9 → threshold = 3 7 22 33 Transactions 1 4 2 Only user 7 has 3 or more transactions. The return array is [ 7 ].
Expert Answer:
Answer rating: 100% (QA)
Answer def processLogslogs threshold Create a dictionary to store the transactio... View the full answer

Related Book For 

Canadian Income Taxation Planning And Decision Making
ISBN: 9781259094330
17th Edition 2014-2015 Version
Authors: Joan Kitunen, William Buckwold
Posted Date:
Students also viewed these electrical engineering questions
-
The ER Model for Arkansas, Inc. database is based on the following business rules. - A department hires many employees. Each employee is hired by one department. - An employee is assigned to more...
-
Need help asap with physics questions 1. a) Write down the three lepton conservation laws, taking care to define all the terms. {3} b) For the neutrinos in the following reactions, assign the...
-
In this assignment, you will have to write a doubly-linkedlist-based partial implementation of the List interface. Unlike theexisting java.util.LinkedList, your implementation is to optimizethe...
-
Use the trapezium rule, with interval-halving and extrapolation, to evaluate 0 log(cosh x) dx to 4dp
-
Gloria maintains a checking account at First Bank. On the third day of January, the bank sent her a statement of her account for December accompanied by the checks that the bank had paid. One of the...
-
The McCartheys owned stock in a corporation that controlled the Salt Lake City Tribune. When that company merged with another company, as part of the deal, the McCartheys were told that they would...
-
You have been asked to value the practice of Dr. Vong, a pediatrician in your town, and are provided with the following facts: The practice generated $800,000 in revenues last year, and these...
-
Outdoor Life manufactures snowboards. Its cost of making 2,000 bindings is as follows: Suppose Lancaster will sell bindings to Outdoor Life for $14 each. Outdoor Life would pay $3 per unit to...
-
Required information [The following information applies to the questions displayed below] Shadee Corporation expects to sell 550 sun shades in May and 330 in June. Each shade sells for $140. Shadee's...
-
Kenmare Architects Ltd. (KAL) was incorporated and commenced operations on January 1, 2014. Sheila Kenmare, the company's only employee, consults with various clients and uses expensive equipment to...
-
ch 1extra # 7 1. Identify the two basic categories of items on an income statement. 2. What do we call the bottom line of the income statement? 1. Identify the two basic categories of items on an...
-
How can leaving or separation in an organization, whether by choice or not, be handled as smoothly as possible by HR? Explain.
-
On March 1, 2021, Navy Corporation used excess cash to purchase U.S. Treasury bonds for $109,000 plus accrued interest. The bonds were purchased at face value. The appropriate interest rate is 6%....
-
Define the following terms: capital goods, consumer goods and services, consumption, demand, distribution, economic goods, economic resources, economic services, economic need, economy, elastic...
-
1. How can j crew ( clothing brand) Increasing its online presence in order to reach a larger audience 2. How can j crew Offer more affordable products in order to appeal to a wider range of...
-
How does globalization impact local cultural identities, and what does this mean for the preservation or transformation of cultural heritage ?
-
In a condenser, cold water from a sea is used for cooling steam. 0 . 0 0 5 m ^ 3 / s of steam enters the condenser with unknown conditions, and then it leaves the condenser as saturated mixture. 0 ....
-
(a) As Section 17.3 discusses, high-frequency sound waves exhibit less diffraction than low-frequency sound waves do. However, even high-frequency sound waves exhibit much more diffraction under...
-
Mavis Corporation, a Canadian company, is a major wholesaler of womens shoes. The company has a history of substantial profits. In 20X7, its net income before tax amounted to $700,000. Mavis...
-
If a group of business assets is sold with specific values attached to each item, what difference, if any, does it make whether the terms of payment (that is, the amount of cash and deferred...
-
Sanford Pipe Ltd. is a Canadian corporation operating a profitable business in eastern Canada. Four years ago, the company attempted to expand its operations to northern Mexico. At that time, Sanford...
-
What is not especially helpful for spotting kiting a. Confirming accounts receivables. b. Look for frequent deposits and checks in the same amount. c. Check for large deposits on Fridays. d. Look for...
-
What is a land flip?
-
Outline the typical kickback scheme.

Study smarter with the SolutionInn App