Can you please solve this in python? 2. Testing Encryption Validity Encryption is the process of converting
Fantastic news! We've Found the answer you've been seeking!
Question:
Can you please solve this in python?
Transcribed Image Text:
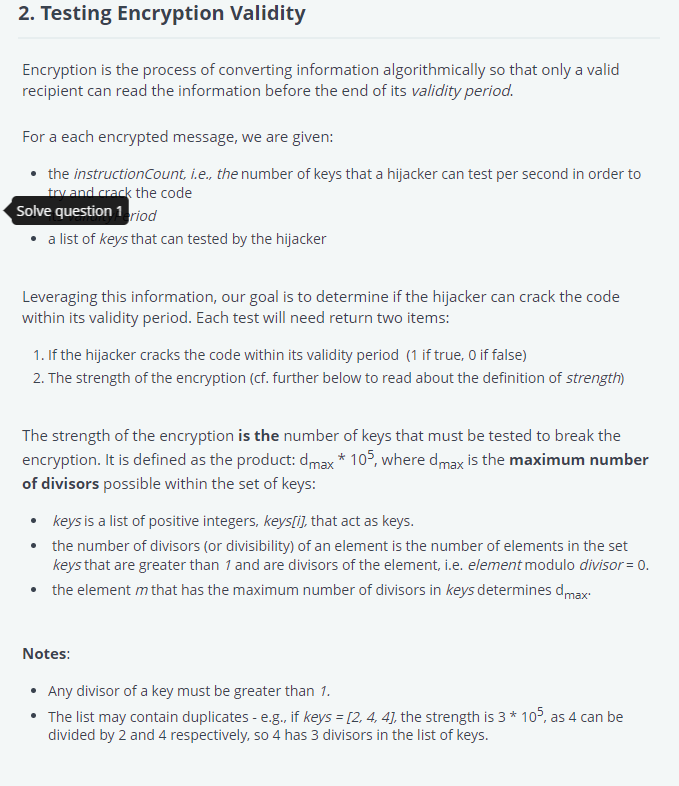
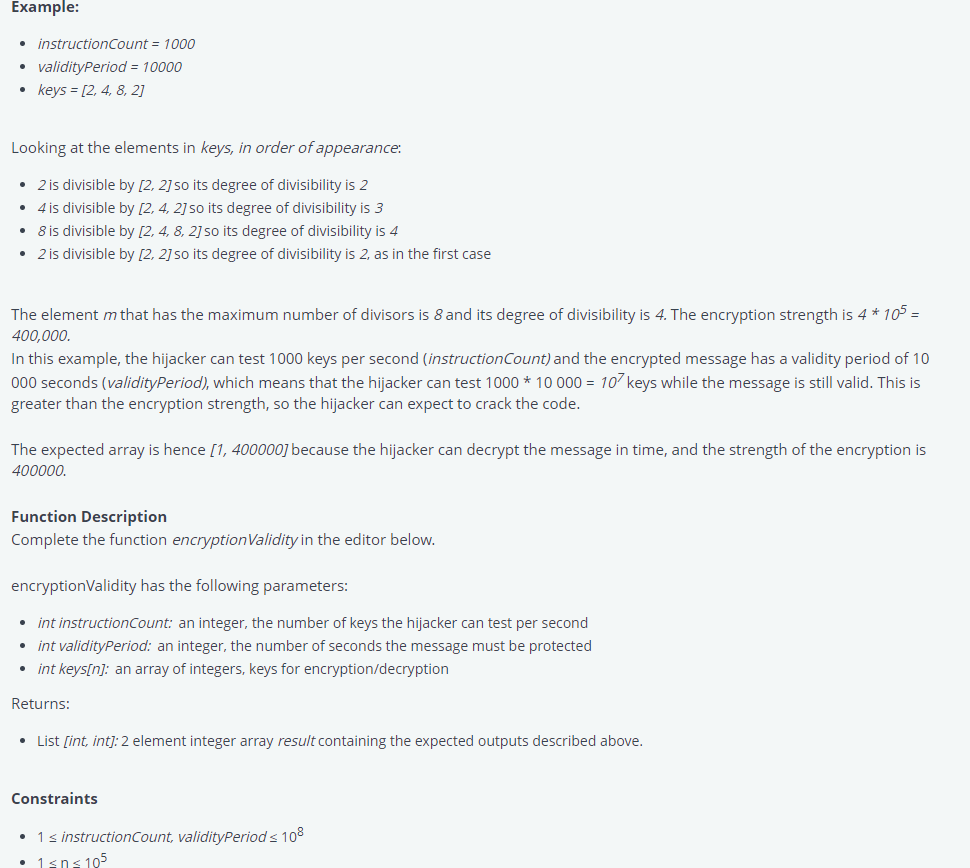
2. Testing Encryption Validity Encryption is the process of converting information algorithmically so that only a valid recipient can read the information before the end of its validity period. For a each encrypted message, we are given: • the instructionCount, i.e., the number of keys that a hijacker can test per second in order to try and crack the code Solve question 1eriod • a list of keys that can tested by the hijacker Leveraging this information, our goal is to determine if the hijacker can crack the code within its validity period. Each test will need return two items: 1. If the hijacker cracks the code within its validity period (1 if true, 0 if false) 2. The strength of the encryption (cf. further below to read about the definition of strength) The strength of the encryption is the number of keys that must be tested to break the encryption. It is defined as the product: dmax * 105, where dmax is the maximum number of divisors possible within the set of keys: • keys is a list of positive integers, keys[i], that act as keys. • the number of divisors (or divisibility) of an element is the number of elements in the set keys that are greater than 1 and are divisors of the element, i.e. element modulo divisor = 0. • the element m that has the maximum number of divisors in keys determines dmax Notes: • Any divisor of a key must be greater than 1. • The list may contain duplicates - e.g., if keys = [2, 4, 4], the strength is 3 * 105, as 4 can be divided by 2 and 4 respectively, so 4 has 3 divisors in the list of keys. 2. Testing Encryption Validity Encryption is the process of converting information algorithmically so that only a valid recipient can read the information before the end of its validity period. For a each encrypted message, we are given: • the instructionCount, i.e., the number of keys that a hijacker can test per second in order to try and crack the code Solve question 1eriod • a list of keys that can tested by the hijacker Leveraging this information, our goal is to determine if the hijacker can crack the code within its validity period. Each test will need return two items: 1. If the hijacker cracks the code within its validity period (1 if true, 0 if false) 2. The strength of the encryption (cf. further below to read about the definition of strength) The strength of the encryption is the number of keys that must be tested to break the encryption. It is defined as the product: dmax * 105, where dmax is the maximum number of divisors possible within the set of keys: • keys is a list of positive integers, keys[i], that act as keys. • the number of divisors (or divisibility) of an element is the number of elements in the set keys that are greater than 1 and are divisors of the element, i.e. element modulo divisor = 0. • the element m that has the maximum number of divisors in keys determines dmax Notes: • Any divisor of a key must be greater than 1. • The list may contain duplicates - e.g., if keys = [2, 4, 4], the strength is 3 * 105, as 4 can be divided by 2 and 4 respectively, so 4 has 3 divisors in the list of keys.
Expert Answer:
Answer rating: 100% (QA)
def cancrackcodeinstructionCount keys validityPeriod Find the maximum number ... View the full answer

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these electrical engineering questions
-
Can you please solve the below question (Task 1)? Task 1: Numerical Solution of Differential Equations Solve the equations, dy dx dy dx = 2 sin(x) + y, y(0) = 1 = x + 3x + 2-2y, y(0) = -1 using...
-
Solve this in C++ asap! BookTester.cpp is given and cannot be modified. Require Book.h Book.cpp Chapter.hChapter.cpp BookTester.cpp #include#include#include"Chapter.h"#include"Book.h"using namespace...
-
: Write code in the next cell to do the following: 1. Asks the user for their first, middle, and last names and stores each in a new variable. 2. Computes the length of the name not including spaces...
-
How are the square numbers embedded in Pascals triangle?
-
Excerpts from The ABC Company statement of cash flows, as adapted, appear as follows: As the chief executive officer of The ABC Company, your duty is to write the management letter to your...
-
Why isnt flash RAM commonly used to implement primary storage?
-
How many degrees of freedom are there? Exercises 49 refer to the following data: Electric motors are assembled on four different production lines. Random samples of motors are taken from each line...
-
Preparing an Income Statement, Statement of Retained Earnings, and Balance Sheet Assume that you are the president of Influence Corporation. At the end of the first year (June 30, 2011) of...
-
Because existing staff are fully scheduled, if the firm is awarded the contract, it must hire one new staff member at a salary of $52,000 to handle the additional workload. The managing partner is...
-
To answer this question, you must obtain data from the Bureau of Economic Analysis (BEA), http://www.bea.gov, on the U.S. balance of payment (BOP) tables. Go to interactive tables to obtain annual...
-
Which of the following IRS pronouncement citations is INCORRECT: a. Notice 0710 2007 CB 324 b. Publication 519 c. Rev Proc 201114 2011 IRB 532 d. Action on Decision 2010002 e all of these citations...
-
The market has the following supply: P = 0.6Q + 32 Demand in the same market is: P = -0.6Q + 101 Price is in ISK. a) What is the ideal position, the equilibrium position in the market? Price and...
-
Delta Company produces a single product. The cost of producing and selling a single unit of this product at the company's normal activity level of 96,000 units per year is: Direct materials Direct...
-
Objects A and B collide in an isolated system. The vector arrows represent the before- and after-collision momentum of objects A and B. Which vector represents the momentum of object B before the...
-
You are working in your kitchen preparing lunch for your family. You have decided to make egg salad sandwiches and are boiling six eggs, each of mass 60.2 g, in 0.850 L of water at 100C. You wish to...
-
Nickleson Company had an unadjusted cash balance of $5,009 as of May 31. The company's bank statement, also dated May 31, included a $70 NSF check written by one of Nickleson's customers. There were...
-
When it comes to pricing a product, why is it important to identify the target group?
-
Which of the following is NOT a magnetic dipole when viewed from far away? a) A permanent bar magnet. b) Several circular loops of wire closely stacked together with the same current running in each...
-
Jim is fired from his job as a waiter and decides to take an extended trip to Europe. After touring Europe for 3 months, Jim returns to look for a new job as a waiter. Are his job-hunting expenses...
-
Ulysses and Penelope are married and file separate returns for 2012. Penelope itemizes her deductions on her return. Ulysses' adjusted gross income was $17,400, his itemized deductions were $2,250,...
-
Quince Corporation has taxable income of $450,000 for its 2012 calendar tax year. Calculate the corporation's income tax liability for 2012 before tax credits. $_________
-
Try-Hard Company was organized in early January of 19X7. The company is in the business of taking computer chips from discarded personal computers and making vases and other items that are used to...
-
How do auditors often determine their anticipated reliance on the internal control structure?
-
Prior to beginning the field work on a new audit engagement in which a CPA does not possess expertise in the industry in which the client operates, the CPA should a. Reduce audit risk by lowering the...

Study smarter with the SolutionInn App


