commonwealth bank network design 1. Rainbow table attacks are a type of attack that attempts to discover
Fantastic news! We've Found the answer you've been seeking!
Question:
commonwealth bank network design 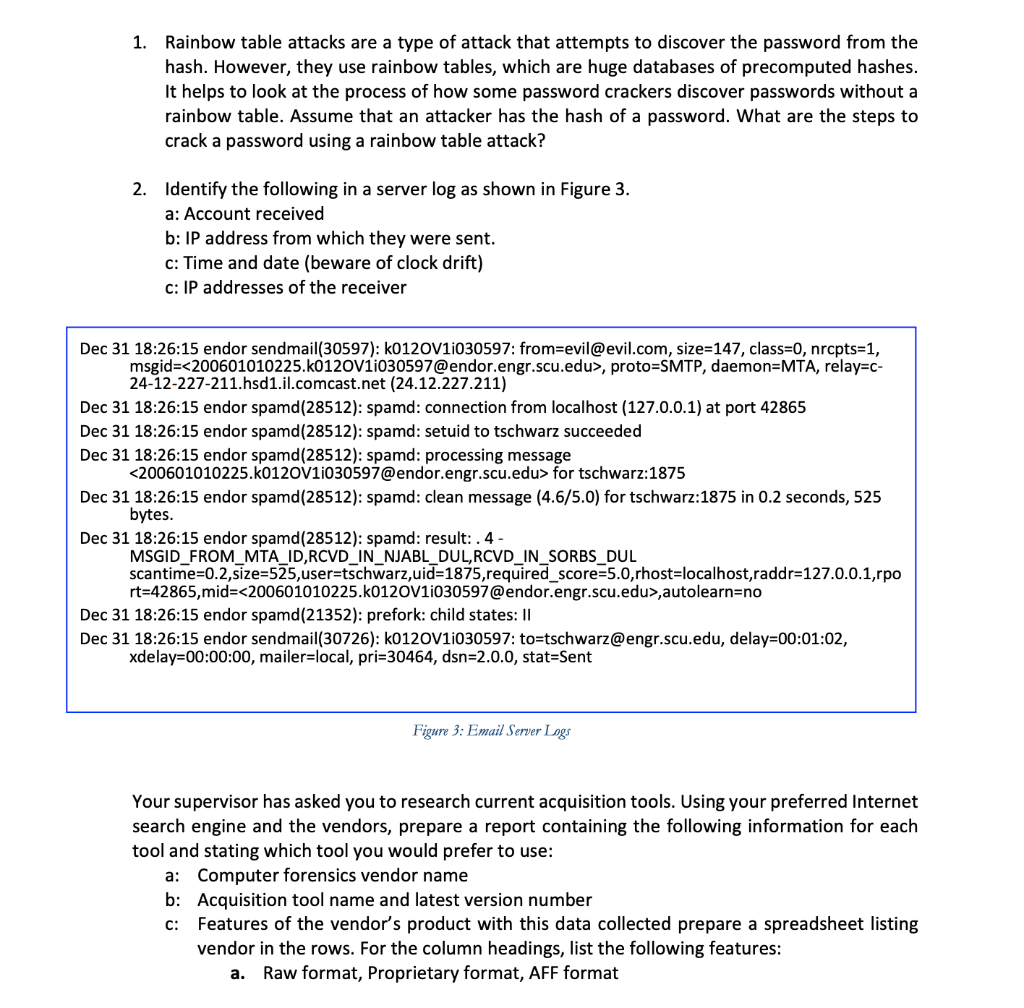
Transcribed Image Text:
1. Rainbow table attacks are a type of attack that attempts to discover the password from the hash. However, they use rainbow tables, which are huge databases of precomputed hashes. It helps to look at the process of how some password crackers discover passwords without a rainbow table. Assume that an attacker has the hash of a password. What are the steps to crack a password using a rainbow table attack? 2. Identify the following in a server log as shown in Figure 3. a: Account received b: IP address from which they were sent. c: Time and date (beware of clock drift) c: IP addresses of the receiver Dec 31 18:26:15 endor sendmail(30597): k0120V1i030597: from=evil@evil.com, size=147, class=0, nrcpts=1, proto-SMTP, daemon=MTA, relay=c- msgid= <200601010225.k0120V1i030597@endor.engr.scu.edu>, 24-12-227-211.hsd1.il.comcast.net (24.12.227.211) Dec 31 18:26:15 endor spamd (28512): spamd: connection from localhost (127.0.0.1) at port 42865 Dec 31 18:26:15 endor spamd (28512): spamd: setuid to tschwarz succeeded Dec 31 18:26:15 endor spamd (28512): spamd: processing message <200601010225.k0120V1i030597@endor.engr.scu.edu> for tschwarz:1875 Dec 31 18:26:15 endor spamd (28512): spamd: clean message (4.6/5.0) for tschwarz:1875 in 0.2 seconds, 525 bytes. Dec 31 18:26:15 endor spamd (28512): spamd: result: . 4 - MSGID_FROM_MTA_ID,RCVD_IN_NJABL_DUL, RCVD_IN_SORBS_DUL scantime=0.2,size=525,user=tschwarz,uid=1875, required_score=5.0,rhost-localhost, raddr=127.0.0.1,rpo rt=42865,mid= <200601010225.k0120V1i030597@endor.engr.scu.edu>,autolearn=no Dec 31 18:26:15 endor spamd (21352): prefork: child states: II Dec 31 18:26:15 endor sendmail(30726): k0120V1i030597: to-tschwarz@engr.scu.edu, delay=00:01:02, xdelay=00:00:00, mailer-local, pri=30464, dsn=2.0.0, stat=Sent Figure 3: Email Server Logs Your supervisor has asked you to research current acquisition tools. Using your preferred Internet search engine and the vendors, prepare a report containing the following information for each tool and stating which tool you would prefer to use: a: Computer forensics vendor name b: Acquisition tool name and latest version number C: Features of the vendor's product with this data collected prepare a spreadsheet listing vendor in the rows. For the column headings, list the following features: a. Raw format, Proprietary format, AFF format 1. Rainbow table attacks are a type of attack that attempts to discover the password from the hash. However, they use rainbow tables, which are huge databases of precomputed hashes. It helps to look at the process of how some password crackers discover passwords without a rainbow table. Assume that an attacker has the hash of a password. What are the steps to crack a password using a rainbow table attack? 2. Identify the following in a server log as shown in Figure 3. a: Account received b: IP address from which they were sent. c: Time and date (beware of clock drift) c: IP addresses of the receiver Dec 31 18:26:15 endor sendmail(30597): k0120V1i030597: from=evil@evil.com, size=147, class=0, nrcpts=1, proto-SMTP, daemon=MTA, relay=c- msgid= <200601010225.k0120V1i030597@endor.engr.scu.edu>, 24-12-227-211.hsd1.il.comcast.net (24.12.227.211) Dec 31 18:26:15 endor spamd (28512): spamd: connection from localhost (127.0.0.1) at port 42865 Dec 31 18:26:15 endor spamd (28512): spamd: setuid to tschwarz succeeded Dec 31 18:26:15 endor spamd (28512): spamd: processing message <200601010225.k0120V1i030597@endor.engr.scu.edu> for tschwarz:1875 Dec 31 18:26:15 endor spamd (28512): spamd: clean message (4.6/5.0) for tschwarz:1875 in 0.2 seconds, 525 bytes. Dec 31 18:26:15 endor spamd (28512): spamd: result: . 4 - MSGID_FROM_MTA_ID,RCVD_IN_NJABL_DUL, RCVD_IN_SORBS_DUL scantime=0.2,size=525,user=tschwarz,uid=1875, required_score=5.0,rhost-localhost, raddr=127.0.0.1,rpo rt=42865,mid= <200601010225.k0120V1i030597@endor.engr.scu.edu>,autolearn=no Dec 31 18:26:15 endor spamd (21352): prefork: child states: II Dec 31 18:26:15 endor sendmail(30726): k0120V1i030597: to-tschwarz@engr.scu.edu, delay=00:01:02, xdelay=00:00:00, mailer-local, pri=30464, dsn=2.0.0, stat=Sent Figure 3: Email Server Logs Your supervisor has asked you to research current acquisition tools. Using your preferred Internet search engine and the vendors, prepare a report containing the following information for each tool and stating which tool you would prefer to use: a: Computer forensics vendor name b: Acquisition tool name and latest version number C: Features of the vendor's product with this data collected prepare a spreadsheet listing vendor in the rows. For the column headings, list the following features: a. Raw format, Proprietary format, AFF format
Expert Answer:
Answer rating: 100% (QA)
SOLUTION 1 Rainbow Table Attack To crack a password using a rainbow table attack the attacker would need to have the hash of the password The steps to ... View the full answer

Related Book For 

Posted Date:
Students also viewed these electrical engineering questions
-
Commonwealth Bank has $400,000 of 9% debenture bonds outstanding. The bonds were issued at 104 in 2010 and mature in 2030. Requirements 1. How much cash did Commonwealth Bank receive when it issued...
-
Australia's Commonwealth Bank lost data of 20m accounts Australia's Commonwealth Bank has admitted losing the bank records of almost 20 million people. Names, addresses, account numbers and...
-
In 2007, First Commonwealth Bank deposited a good sum of money in the bank account of an Altoona couple by mistake. After realizing its mistake, it sued the retired couple to get the money back. The...
-
According to a study performed by the NCAA, the average rate of injuries occurring in collegiate womens soccer is 8.6 per 1000 participants (www.fastsports.com/tips/tip12/). a. Using the Poisson...
-
Yang Company reported net income of $37,925 and net sales of $390,000 for the current year. Calculate the companys profit margin and interpret the result. Assume that its competitors earn an average...
-
Starting from Equation 38.32, derive Equation 38.33. Equation 38.32 Equation 38.33 e2 = }m| 4 e2 \ma;? 4ap E, =mv, 2,2 m'n- e? 2 En n 1 4 2a 4
-
In some instances, a temporary restraining order can be granted ex parte (i.e., without notice to the other side) until a hearing for a preliminary injunction can be held. Further investigate CCP 527...
-
Assume that Atlas Sporting Goods Inc. has $840,000 in assets. If it goes with a low-liquidity plan for the assets, it can earn a return of 15 percent, but with a high-liquidity plan the return will...
-
King Company has two divisions whose most recent financial statements are shown below: Commercial Division Residential Division Unit sales Sales Less: cost of goods sold: Unit-level production costs...
-
The following is the statement of financial position of TT and Co. (see Self-Assessment Question 3.1 on page 113) at the end of its first year of trading: Statement of financial position as at 31...
-
AMS Company has unexpectedly generated a one-time extra $5 million in cash flow this year. After announcing the extra cashflow, AMS's stock price was $55 per share (it has 1 million...
-
What is expected rate of return on this portfolio,\5 points) What is the standard deviation of this portfolio? Tyler has a portfolio comprised of $8,000 of stock A and $12,000 of stock B. Portfolio...
-
You have a convex lens with a focal length of 11.3cm. You want to use it to project an image from your cell phone's screen onto a wall that is 198cm away from the lens. How big the image would be on...
-
What are the key performance indicators (KPIs) that best measure operational excellence within a lean manufacturing environment, and how do they inform continuous improvement strategies?
-
A 23.5kg box is sitting on a concrete floor and is pushed with a force of 100N. If the coefficient of friction between the wood and concrete is 0.5, what is the force of friction on the box? For this...
-
A gardener pushes down along the handle of a lawn mover of 20 kg mass with a force of 150 N. The handle makes an angle of 60 to the vertical. Calculate the instantaneous acceleration of the mower if...
-
Prepare a 5-year forecast of Net Operating Income in a format similar to Real Estate Finance and Investments, Exhibit 10-18, or Exhibit 11-16.( McGraw-Hill Student Resources Excel Templates )...
-
If a force of F = 50 Ib is applied to the pads at A and C, determine the smallest dimension d required for equilibrium if the spring has an unstretched length of 1 ft. B 1 ft 1 ft F k = 15016/fr 1ft...
-
How do the repressor and the cro protein affect the transcription from PR and PRM? Explain where these proteins are binding to cause their effects.
-
Transcription factors such as the glucocorticoid receptor and the CREB protein form homodimers and activate transcription. Other transcription factors form heterodimers. For example, a transcription...
-
Cell biology textbooks often discuss cellular proteins encoded by genes that are members of a gene family. Examples of such proteins include myosins and glucose transporters. Look through a cell...
-
The assumptions are as follows: Company A records an uncertain tax liability of \($50\) million as of the reporting date. Company A expects to settle the amount in the fourth quarter of the...
-
Find the P-value for the following values of the test statistic t, sample size n, and alternate hypothesis H1. If you use Table A.3, you may specify that P is between two values. a. t = 2.584, n =...
-
A company is computing intraperiod tax allocation for the current year and has accumulated the following income and loss items: The tax rate for the current year is 21%. Tax credits of $100,000 are...

Study smarter with the SolutionInn App