COMP/ECPE 177: Course Project 2: Traceroute In this course project, you will develop a Python script...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
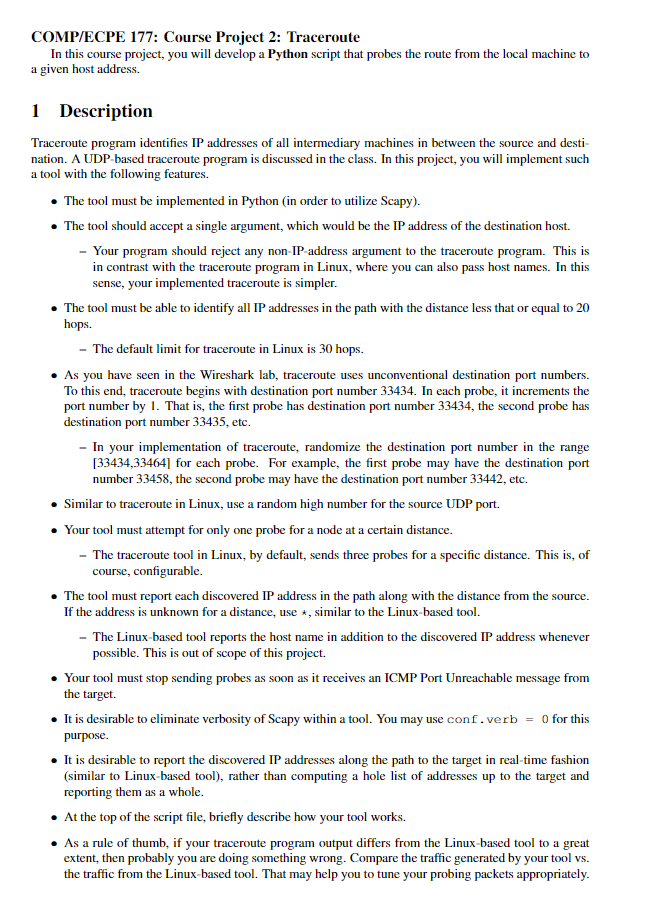
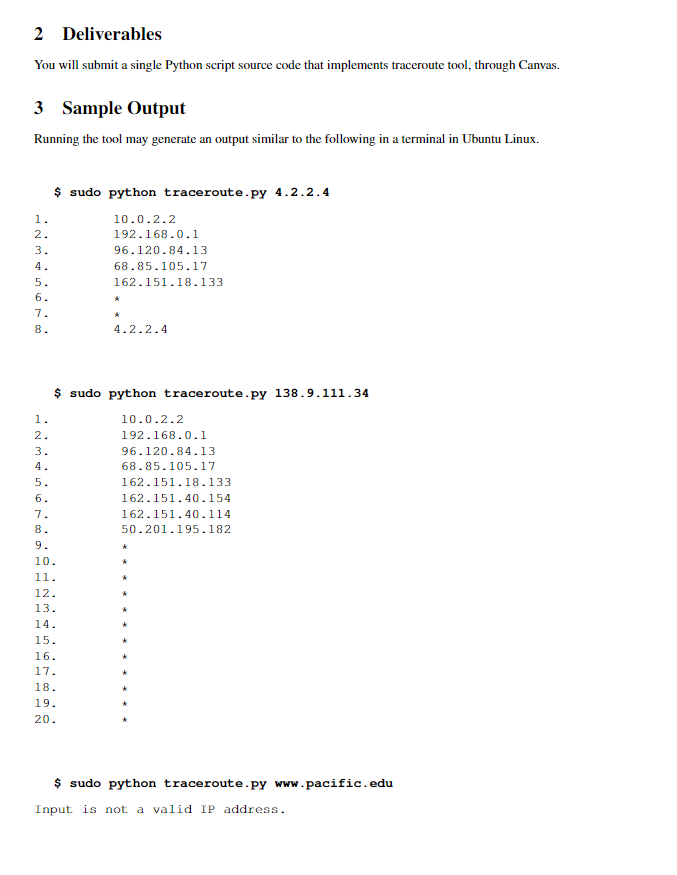
COMP/ECPE 177: Course Project 2: Traceroute In this course project, you will develop a Python script that probes the route from the local machine to a given host address. 1 Description Traceroute program identifies IP addresses of all intermediary machines in between the source and desti- nation. A UDP-based traceroute program is discussed in the class. In this project, you will implement such a tool with the following features. The tool must be implemented in Python (in order to utilize Scapy). The tool should accept a single argument, which would be the IP address of the destination host. - Your program should reject any non-IP-address argument to the traceroute program. This is in contrast with the traceroute program in Linux, where you can also pass host names. In this sense, your implemented traceroute is simpler. The tool must be able to identify all IP addresses in the path with the distance less that or equal to 20 hops. - The default limit for traceroute in Linux is 30 hops. As you have seen in the Wireshark lab, traceroute uses unconventional destination port numbers. To this end, traceroute begins with destination port number 33434. In each probe, it increments the port number by 1. That is, the first probe has destination port number 33434, the second probe has destination port number 33435, etc. - In your implementation of traceroute, randomize the destination port number in the range [33434,33464] for each probe. For example, the first probe may have the destination port number 33458, the second probe may have the destination port number 33442, etc. Similar to traceroute in Linux, use a random high number for the source UDP port. Your tool must attempt for only one probe for a node at a certain distance. - The traceroute tool in Linux, by default, sends three probes for a specific distance. This is, of course, configurable. The tool must report each discovered IP address in the path along with the distance from the source. If the address is unknown for a distance, use, similar to the Linux-based tool. The Linux-based tool reports the host name in addition to the discovered IP address whenever possible. This is out of scope of this project. Your tool must stop sending probes as soon as it receives an ICMP Port Unreachable message from the target. It is desirable to eliminate verbosity of Scapy within a tool. You may use conf.verb = 0 for this purpose. It is desirable to report the discovered IP addresses along the path to the target in real-time fashion (similar to Linux-based tool), rather than computing a hole list of addresses up to the target and reporting them as a whole. At the top of the script file, briefly describe how your tool works. As a rule of thumb, if your traceroute program output differs from the Linux-based tool to a great extent, then probably you are doing something wrong. Compare the traffic generated by your tool vs. the traffic from the Linux-based tool. That may help you to tune your probing packets appropriately. 2 Deliverables You will submit a single Python script source code that implements traceroute tool, through Canvas. 3 Sample Output Running the tool may generate an output similar to the following in a terminal in Ubuntu Linux. 1. 2. 3. 4. 5. 6. 7. 8. HN 1. 2. $ sudo python traceroute.py 4.2.2.4 10.0.2.2 192.168.0.1 96.120.84.13 68.85.105.17 162.151.18.133 3. 4. $ sudo python traceroute.py 138.9.111.34 5. 6. 7. 8. 9. 10. 11. 12. 13. 14. 15. 4.2.2.4 16. 17. 18. 19. 20. 10.0.2.2 192.168.0.1 96.120.84.13 68.85.105.17 162.151.18.133 162.151.40.154 162.151.40.114 50.201.195.182 $ sudo python traceroute.py www.pacific.edu Input is not a valid IP address. COMP/ECPE 177: Course Project 2: Traceroute In this course project, you will develop a Python script that probes the route from the local machine to a given host address. 1 Description Traceroute program identifies IP addresses of all intermediary machines in between the source and desti- nation. A UDP-based traceroute program is discussed in the class. In this project, you will implement such a tool with the following features. The tool must be implemented in Python (in order to utilize Scapy). The tool should accept a single argument, which would be the IP address of the destination host. - Your program should reject any non-IP-address argument to the traceroute program. This is in contrast with the traceroute program in Linux, where you can also pass host names. In this sense, your implemented traceroute is simpler. The tool must be able to identify all IP addresses in the path with the distance less that or equal to 20 hops. - The default limit for traceroute in Linux is 30 hops. As you have seen in the Wireshark lab, traceroute uses unconventional destination port numbers. To this end, traceroute begins with destination port number 33434. In each probe, it increments the port number by 1. That is, the first probe has destination port number 33434, the second probe has destination port number 33435, etc. - In your implementation of traceroute, randomize the destination port number in the range [33434,33464] for each probe. For example, the first probe may have the destination port number 33458, the second probe may have the destination port number 33442, etc. Similar to traceroute in Linux, use a random high number for the source UDP port. Your tool must attempt for only one probe for a node at a certain distance. - The traceroute tool in Linux, by default, sends three probes for a specific distance. This is, of course, configurable. The tool must report each discovered IP address in the path along with the distance from the source. If the address is unknown for a distance, use, similar to the Linux-based tool. The Linux-based tool reports the host name in addition to the discovered IP address whenever possible. This is out of scope of this project. Your tool must stop sending probes as soon as it receives an ICMP Port Unreachable message from the target. It is desirable to eliminate verbosity of Scapy within a tool. You may use conf.verb = 0 for this purpose. It is desirable to report the discovered IP addresses along the path to the target in real-time fashion (similar to Linux-based tool), rather than computing a hole list of addresses up to the target and reporting them as a whole. At the top of the script file, briefly describe how your tool works. As a rule of thumb, if your traceroute program output differs from the Linux-based tool to a great extent, then probably you are doing something wrong. Compare the traffic generated by your tool vs. the traffic from the Linux-based tool. That may help you to tune your probing packets appropriately. 2 Deliverables You will submit a single Python script source code that implements traceroute tool, through Canvas. 3 Sample Output Running the tool may generate an output similar to the following in a terminal in Ubuntu Linux. 1. 2. 3. 4. 5. 6. 7. 8. HN 1. 2. $ sudo python traceroute.py 4.2.2.4 10.0.2.2 192.168.0.1 96.120.84.13 68.85.105.17 162.151.18.133 3. 4. $ sudo python traceroute.py 138.9.111.34 5. 6. 7. 8. 9. 10. 11. 12. 13. 14. 15. 4.2.2.4 16. 17. 18. 19. 20. 10.0.2.2 192.168.0.1 96.120.84.13 68.85.105.17 162.151.18.133 162.151.40.154 162.151.40.114 50.201.195.182 $ sudo python traceroute.py www.pacific.edu Input is not a valid IP address.
Expert Answer:

Related Book For 

Modern Database Management
ISBN: 978-0133544619
12th edition
Authors: Jeff Hoffer, Ramesh Venkataraman, Heikki Topi
Posted Date:
Students also viewed these computer network questions
-
Follow the submission instructions for each exercise and ensure that you meet the deadline, use the correct submission process and submit your work to the correct place. For some laboratory tasks you...
-
Design a Java class that represents a cache with a fixed size. It should support operations like add, retrieve, and remove, and it should evict the least recently used item when it reaches capacity.
-
Question 4 Tic-tac-toe (also known as noughts and crosses) is a game for two players, X and O, who take turns marking the spaces in a 3x3 grid. The player who succeeds in placing three of their marks...
-
Animal Days Incorporated operates a kennel designed to board and pamper up to 10 household cats and dogs while the pet owners are away. Pet owners pay a per-day fee. Variable indirect costs for the...
-
Emerson Processing borrowed $900,000 for installing energy-efficient lighting and safety equipment in its La Grange manufacturing facility. The terms of the loan were such that the company could pay...
-
Explain when it is appropriate to use a randomized block design.
-
A bond trader purchased each of the following bonds at a yield to maturity of 8%. Immediately after she purchased the bonds, interest rates fell to 7%. What is the percentage change in the price of...
-
7 Find the derivative of f (w) = w8+ 7w. What is the domain of f' (w)? Enclose numerators and denominators in parentheses. For example (a - b)/ (1 + n). Enter the domain in interval notation. For o,...
-
Fast Deliveries, Inc. (FDI), was organized in December last year and had limited activity last year. The resulting bala sheet at the beginning of the current year is provided below: Assets: Cash...
-
5. Do this problem by hand. Assume x(0) = [0 0 0]. Consider the following linear system: 3 24 -10 0 5 -4 2 7 21 X2 13 - -53 ||xG) -x-1) || ||x6||a 27 (a) Perform 3 iterations of the Jacobi method. At...
-
Ashleigh Batista is 42 years old and divorced. Her net income for 2023 is $84,400. She has retained the family home and custody of both children, who live with her. Her son is 23 years old, has no...
-
K Solve using the substitution method. y = 3x+5 2x+y= -5
-
Verify that the following matrix has one negative and two positive eigenvalues. M = 12 1 3 12 122
-
Calculate the nominal interest rate of Stephanie's loan of $12,000.00 if it accumulated to $13,496.42 in 7 years and interest is compounded monthly. Nominal interest rate: %
-
ELMI Corporation acquired a barn and three acres of land for a lump-sum price of $2,400,000. The barn contained used but fully-functional farming equipment. According to independent appraisals, the...
-
You have been asked by the Payroll Manager, Linda Laporte, to create a short job aid to assist the payroll practitioners with reconciling the Revenu Qubec (RQ) account. Your organization is a monthly...
-
H.J. Heinzs annual dividends were as follows: 1990 ..............$0.540 1991.............. 0.620 1992 .............. 0.700 1993.............. 0.780 1994 .............. 0.860 1995 .............. 0.940...
-
Millennium College (see Problem and Exercise 9-28) now wants to include new data about course sections: the department offering the course, the academic unit to which the department reports, and the...
-
Review Figure 2-8 and Figure 2-22. Figure 2-8 Figure 2-22 a. Identify any attributes in Figure 2-22 that might be composite attributes but are not shown that way. Justify your suggestions. Redraw the...
-
Ask a database administrator or database or system analyst in a local company to show you an EER (or E-R) diagram for one of the organization's primary databases. Does this organization model have...
-
What is the relation between degrees Fahrenheit and degrees Rankine? And the relation between degrees Celsius and Kelvin?
-
State Newton's second law as you would apply it to a control mass.
-
Define a 1-pound force in terms of the acceleration it will give to a 1-pound mass. Give a similar definition for a newton in the SI system.

Study smarter with the SolutionInn App