Consider a local area network that can transmit datagrams with the MTU size of 500 bytes....
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
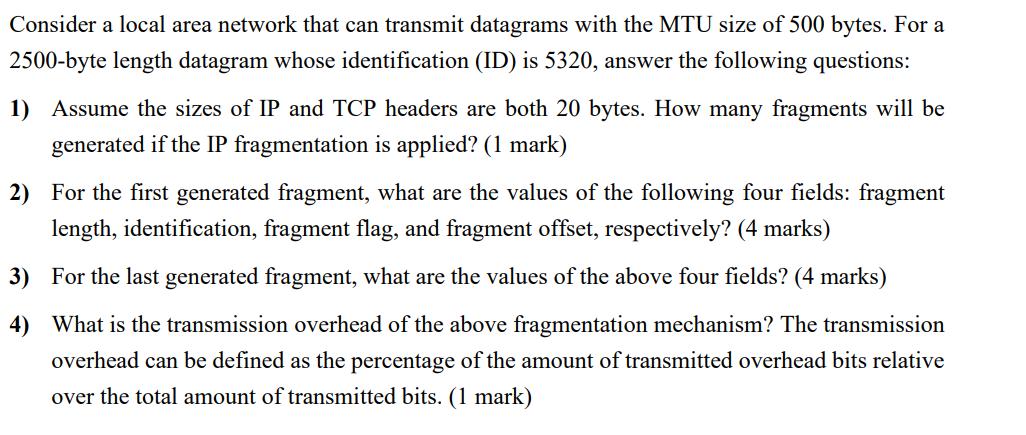
Consider a local area network that can transmit datagrams with the MTU size of 500 bytes. For a 2500-byte length datagram whose identification (ID) is 5320, answer the following questions: 1) Assume the sizes of IP and TCP headers are both 20 bytes. How many fragments will be generated if the IP fragmentation is applied? (1 mark) 2) For the first generated fragment, what are the values of the following four fields: fragment length, identification, fragment flag, and fragment offset, respectively? (4 marks) 3) For the last generated fragment, what are the values of the above four fields? (4 marks) 4) What is the transmission overhead of the above fragmentation mechanism? The transmission overhead can be defined as the percentage of the amount of transmitted overhead bits relative over the total amount of transmitted bits. (1 mark) Consider a local area network that can transmit datagrams with the MTU size of 500 bytes. For a 2500-byte length datagram whose identification (ID) is 5320, answer the following questions: 1) Assume the sizes of IP and TCP headers are both 20 bytes. How many fragments will be generated if the IP fragmentation is applied? (1 mark) 2) For the first generated fragment, what are the values of the following four fields: fragment length, identification, fragment flag, and fragment offset, respectively? (4 marks) 3) For the last generated fragment, what are the values of the above four fields? (4 marks) 4) What is the transmission overhead of the above fragmentation mechanism? The transmission overhead can be defined as the percentage of the amount of transmitted overhead bits relative over the total amount of transmitted bits. (1 mark)
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
Give Correct ANSWERS Human-Computer Interaction (a) If you had been one of the original inventors of the WIMP interface, and engineers on the technical team had been sceptical about the advantages...
-
The FBI Standard Survey of Crimes shows that for about 80% of all property crimes (burglary, larceny, car theft, etc.), the criminals are never found and the case is never solved (Source: True Odds,...
-
Explain the nature of the accruals concept and the matching concept. Give an example of the application of each.
-
1. Review the characteristics of global and transnational companies in Chapter 1. Based on your reading of the case, would IKEA be described as a global firm or a transnational firm? 2. At the end of...
-
Calculate the values of \(K_{p}\) at \(25^{\circ} \mathrm{C}\) and \(800^{\circ} \mathrm{C}\) for the water-gas reaction \[ \mathrm{CO}(\mathrm{g})+\mathrm{H}_{2} \mathrm{O}(\mathrm{g}) ightarrow...
-
Toledo Chemical Company buys A-123 for $2.40 a gallon. At the end of distilling in Department 1, A-123 splits off into three products: B-1, B-2, and B-3. Toledo sells B-1 at the split-off point, with...
-
Analyze the challenges and techniques involved in process migration across distributed systems. How do operating systems and distributed computing frameworks manage process state, data consistency,...
-
The following trial balance was extracted from the books of Old NV on 31 December 20X1. Note of information not taken into the trial balance data: (a) Provide for: (i) An audit fee of 38,000. (ii)...
-
What are Two properties characterize the secure flow of information?
-
Planning is an approach which helps us decide on the path to achieve the set of objectives an individual, an organization, or a group of people have. True False
-
Describe your experience where you have developed a good rapport with your peers and supervisors.
-
Executive methods, market research, and the Delphi method are examples of Quantitative method of forecasting Qualitative method of forecasting Benchmarking None of the above
-
The Zenibeth Factory, which manufactured Quasar television sets, was taken over by a Japanese company in the USA in the 1980s. After overtaking the company, it was decided to make changes in the way...
-
Planning does not render flexibility. True False
-
What are the journal entries for the following? Received a certified check for $827.00 from a customer Alice Cordero as payment in full on her account. Ms. Cordero's account was written off as...
-
1. What is the semi-annually compounded interest rate if $200 accumulates to $318.77 in eight years? Answer in percentage with two decimal places. 2. What is the quarterly compounded interest rate if...
-
The banker's algorithm is being run in a system with m resource classes and n processes. In the limit of large m and n, the number of operations that must be performed to check a state for safety is...
-
Files in MS-DOS have to compete for space in the FAT -16 table in memory. If one file uses k entries, that is k entries that are not available to any other file, what constraint does this place on...
-
Describe a way to use mmap and signals to construct an interprocess-communication mechanism.
-
Located in Tokyo, Japan, Sony Mobile Communications is a prominent competitor in the worldwide electronics equipment market. Because of stagnant sales in its ultra HD TVs, that division has decided...
-
Cory Rogers of CMG Research was happy to call Nick Thomas to inform him that Auto Concepts survey data were collected and ready for analysis. Of course, Cory had other marketing research projects and...
-
What must be determined before using correlation? Why is it essential?

Study smarter with the SolutionInn App


