Consider the following frame captured in Wireshark. Frame 29: 418 bytes on wire (3344 bits), 418...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
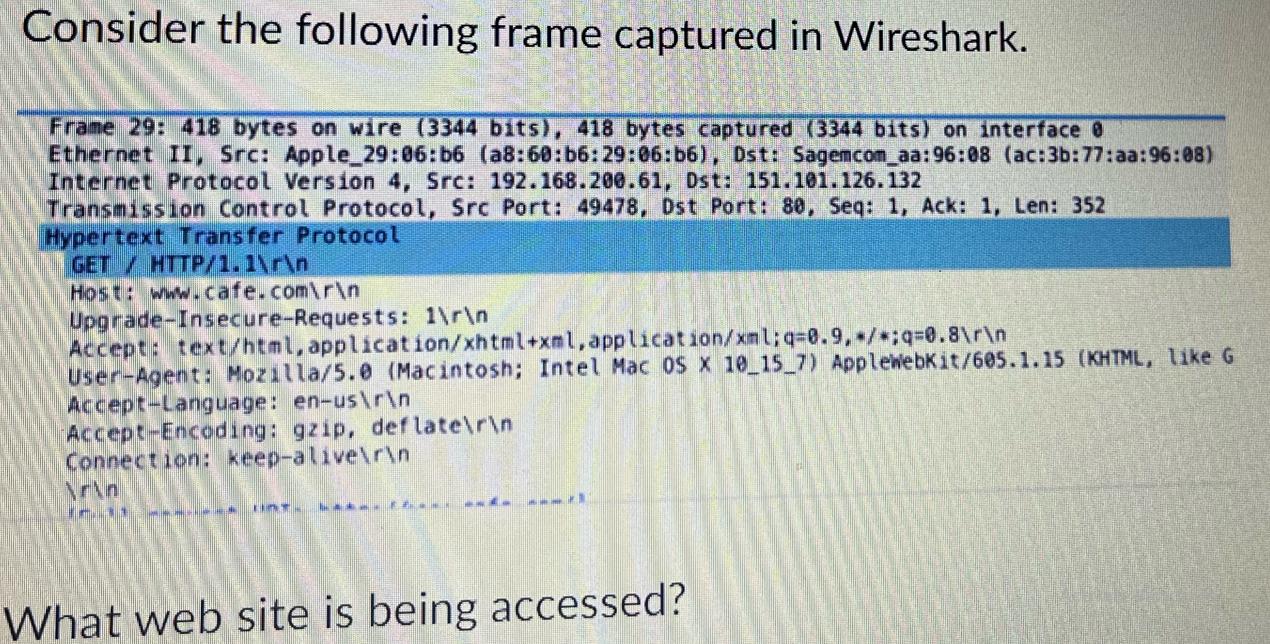
Consider the following frame captured in Wireshark. Frame 29: 418 bytes on wire (3344 bits), 418 bytes captured (3344 bits) on interface 8 Ethernet II, Src: Apple_29:06:b6 (a8:60:b6:29:06:b6), Dst: Sagemcom aa:96:08 (ac:3b:77:aa:96:08) Internet Protocol Version 4, Src: 192.168.200.61, Dst: 151.101.126.132 Transmission Control Protocol, Src Port: 49478, Dst Port: 80, Seq: 1, Ack: 1, Len: 352 Hypertext Transfer Protocol GET/ HTTP/1.1\r\n Host: www.cafe.com\r\n Upgrade-Insecure-Requests: 1\r\n Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q-0.8\r\n User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) ApplewebKit/605.1.15 (KHTML, like G Accept-Language: en-us\r\n Accept-Encoding: gzip, deflate\r\n Connection: keep-alive\r\n \r\n 1. UNT. Lake. What web site is being accessed? Consider the following frame captured in Wireshark. Frame 29: 418 bytes on wire (3344 bits), 418 bytes captured (3344 bits) on interface 8 Ethernet II, Src: Apple_29:06:b6 (a8:60:b6:29:06:b6), Dst: Sagemcom aa:96:08 (ac:3b:77:aa:96:08) Internet Protocol Version 4, Src: 192.168.200.61, Dst: 151.101.126.132 Transmission Control Protocol, Src Port: 49478, Dst Port: 80, Seq: 1, Ack: 1, Len: 352 Hypertext Transfer Protocol GET/ HTTP/1.1\r\n Host: www.cafe.com\r\n Upgrade-Insecure-Requests: 1\r\n Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q-0.8\r\n User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) ApplewebKit/605.1.15 (KHTML, like G Accept-Language: en-us\r\n Accept-Encoding: gzip, deflate\r\n Connection: keep-alive\r\n \r\n 1. UNT. Lake. What web site is being accessed?
Expert Answer:
Answer rating: 100% (QA)
The website being accessed in the image is wwwcafecom The image shows a scr... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0133594140
7th edition
Authors: James Kurose, Keith Ross
Posted Date:
Students also viewed these computer network questions
-
analyze the attached Seagate case. In your analysis, you should address the following questions: 1) Why is Seagate undertaking this transaction? Is it necessary to divest the Veritas shares in a...
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
(10 points) Given that ry + xy = 1. 1. Find a solution of the differential equation that satisfies the initial condition y(1) = 10. Answer: y = 2. Find a solution of the differential equation that...
-
John dies on 3 March 2021. Between 6 April 2020 and 3 March 2021, he has capital gains of 1,200 and capital losses of 15,400. His net gains in recent tax years (and the annual exemption for each...
-
1. Give a formula that can be used to calculate each of the following: 2. State the binomial theorem. (, ) (, ) !
-
Darden Restaurants (subject of the Global Company Profile at the beginning of this chapter), owner of popular brands such as Olive Garden and Red Lobster, requires unique supply chains to serve more...
-
In your audit of the Whitestable Company's December 31, 1999 financial statements, you become aware of the following controls or procedures over investments, debt, and equity: a. On June 15, 1999,...
-
Cam and Anna are very satisfied with their first month of operations. Their major effort centered on signing various artists to live performance contracts, and they had more success than they had...
-
Nishi Corporation prepares financial statements for each month-end. As part of its accounting process, estimated income taxes are accrued each month for 32% of the current month's net income. The...
-
Beacons Company maintains and repairs warning lights, such as those found on radio towers and lighthouses. Beacons Company prepared the following end-of-period spreadsheet at December 31, 20Y5, the...
-
As a result of a chemical spill, benzene is evaporating at the rate of 1 gram per minute into a room that is 6m x 6m x 3 m in size and has a ventilation rate of 10m 3 /min. Compute the steady-state...
-
What is the probable effect of each of the following on the exchange rate of a country, other things being equal? a. The quantity of oil imports is greatly decreased, but the expenditure on imported...
-
To whom is credit given for the development of the JIT/ Lean system?
-
Identify the two pillars of the Toyota Production System.
-
List the seven wastes.
-
What two fundamental advantages are provided by JIT/Lean?
-
A piano tuner who wishes to tune the note D corresponding to a frequency of 73.416 hertz has tuned A4 to a frequency of 440.000 hertz. Which harmonic of D (counting the fundamental as the first...
-
What are three disadvantages of using the direct write-off method?
-
What is an essential different between RR and WFQ packet scheduling? Is there a case (Consider the WFQ weights) where RR and WFQ will behave exactly the same?
-
How arc different RTP streams in different sessions identified by a receiver? How are different streams from within the same session identified?
-
Visit the Go-sack-N Java applet at the companion Web site. a. Have the source send five packets, and then pause the animation before any of the five packets reach the destination. Then kill the first...
-
Under what conditions is an auditor most likely to confirm payables?
-
Explain how an auditor determines whether all recorded payables actually represent bona fide obligations of the entity.
-
Why is confirmation ineffective in detecting understatement of liabilities?

Study smarter with the SolutionInn App


