Consider the following message authentication code: H: {0, 1}* {0, 1}n H(m) = = m mod...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
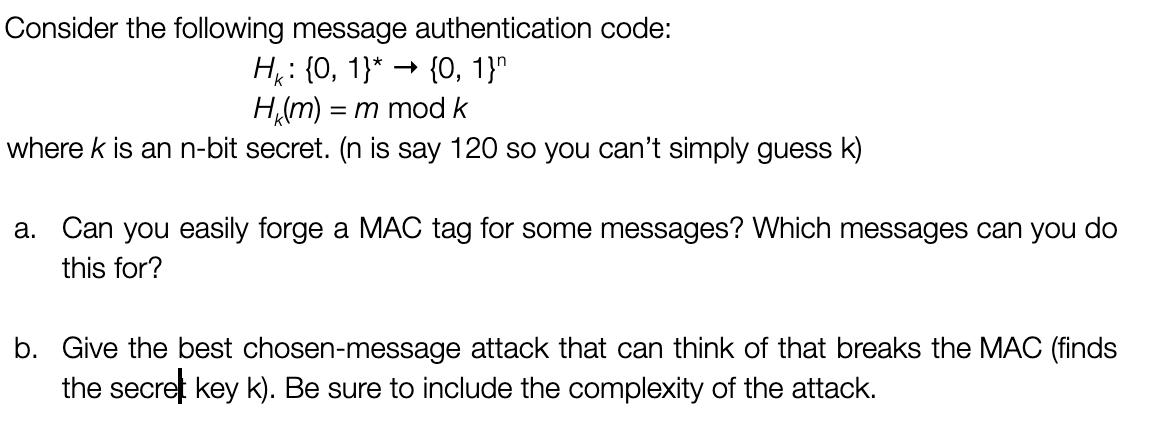
Consider the following message authentication code: H: {0, 1}* {0, 1}n H(m) = = m mod k where k is an n-bit secret. (n is say 120 so you can't simply guess k) a. Can you easily forge a MAC tag for some messages? Which messages can you do this for? b. Give the best chosen-message attack that can think of that breaks the MAC (finds the secret key k). Be sure to include the complexity of the attack. Consider the following message authentication code: H: {0, 1}* {0, 1}n H(m) = = m mod k where k is an n-bit secret. (n is say 120 so you can't simply guess k) a. Can you easily forge a MAC tag for some messages? Which messages can you do this for? b. Give the best chosen-message attack that can think of that breaks the MAC (finds the secret key k). Be sure to include the complexity of the attack.
Expert Answer:
Answer rating: 100% (QA)
a Can you easily forge a MAC tag for some messages Which messages can you do this for Yesyou can easily forge a MAC tag for any message that is equal to the secret key k mod kFor exampleif the secret ... View the full answer

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
Describe how the work placement organization monitors and reviews the effectiveness of the services provided to clients in relation to relevant social and cultural factors. Include how this is in...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
This data set represents the web server hit logs for a single website for a single day. You're going to do some analysis of the data, but first you need to normalize it properly -- which requires...
-
A particle is thrown vertically upwards into the air. Its height s (in m) above the ground after time t (in seconds) is given by s = 25t 5t 2 (a) What height does the particle reach? (b)What is its...
-
LaDanion's Limos reports net income of $120,000, average total assets of $600,000, and average total liabilities of $240,000. Calculate LaDanion's return on assets and return on equity ratios.
-
Oxford Consulting, Inc., expects the following costs and expenses during the coming year: Required a. Compute a predetermined overhead rate applied on the basis of direct labor hours. b. Prepare a...
-
Non-current liabilities are those which: a. Are due for repayment in less than one year b. Are never repaid c. Are due for repayment after more than one year d. Will be repaid in one year's time
-
Refer to the financial statements for Castile Products, Inc., in Exercise 16-7. Assets at the beginning of the year totaled $280,000, and the stockholders equity totaled $161,600. Required: Compute...
-
Find the necessary sample size. Weights of women in one age group are normally distributed with a standard deviation o 17 lb. A researcher wishes to estimate the mean weight of all women in this age...
-
Certain radial tires had useful lives of 35,200, 41,000, 44,700, 38,600, and 41,500 miles. Assuming that these data can be looked upon as a random sample from an exponential population, use the...
-
What is one anti - pattern of the inspect too many teams, present enablers and Technical debt not enough preparation goes into the quantitative and qualitative measurement product, managers, lead the...
-
The operating income and the amount of invested assets in each division of Conley Industries are as follows: Retail Division Commercial Division Internet Division Operating income Invested Assets...
-
How do allosteric enzymes dynamically modulate their activity in response to the presence of specific effector molecules, and what role do these effectors play in the regulation of enzymatic function...
-
Select one of the following projects with your learning team to complete over the duration of the semester: Open a new restaurant Start-up an autonomous vehicle taxi service Plan and execute a...
-
The volume can then be approximated with the Riemann sum A(x1)Ax++ A(xn)Ax, where n is the number of scans, Ax is the space between scans, and A(x) is the area of the organ given by the ith scan. For...
-
How do theories of motivation, such as Self-Determination Theory and Expectancy Theory, inform the design of effective incentive structures within organizations ?
-
An essay includes contains five paragraphs. A diagram [ Escoger ] The key words of a thesis [ Escoger ] statement The thesis statement [ Escoger ] A typical essay [ Escoger ] A Common Method of [...
-
A fast-food restaurant averages 150 customers per hour. The average processing time per customer is 90 seconds. a. Determine how many cash registers the restaurant should have if it wishes to...
-
Although new TCP implementations use the SACK option to report the out of order and duplicate range of bytes, explain how old implementations can indicate that the bytes in a received segment are out...
-
What is the purpose of a firewall?
-
The DatagramPacket class has two constructors (see Table 25.11). Which constructor can be used as a sending packet? Table 25.11 Some methods in DatagramPacket class public final class...
-
The controls in a computerized system are classified as: a. input, processing, and output. b. input, processing, output, and storage. c. input, processing, output, and control. d. input, processing,...
-
An employee in the receiving department keyed in a shipment from a remote terminal and inadvertently omitted the purchase order number. The best systems control to detect this error would be a a....
-
In a computer system, how are accounting records posted? a. master file is updated to a transaction file b. master file is updated to an index file c. transaction file is updated to a master file d....

Study smarter with the SolutionInn App


