Consider the following network of five hosts (h1 to h5), five Openflow switches (s1 to s5)...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
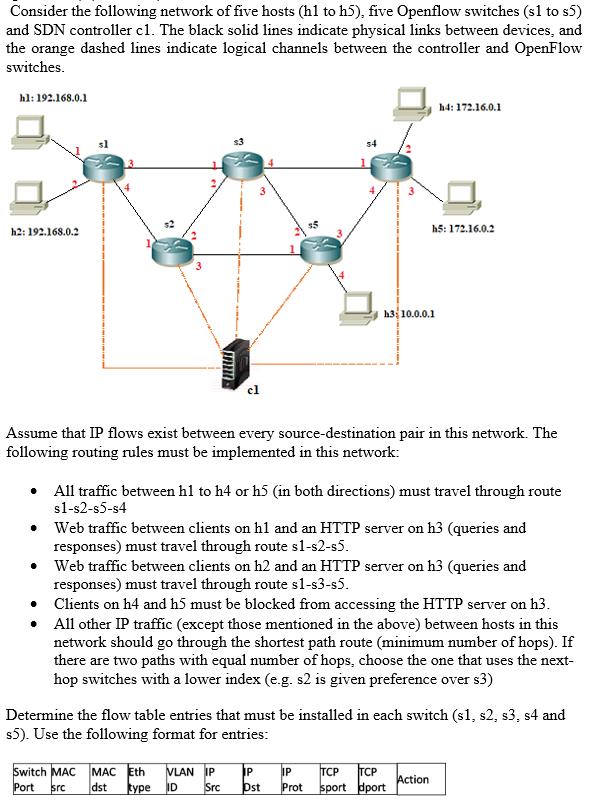
Consider the following network of five hosts (h1 to h5), five Openflow switches (s1 to s5) and SDN controller c1. The black solid lines indicate physical links between devices, and the orange dashed lines indicate logical channels between the controller and OpenFlow switches. hl: 192.168.0.1 h2: 192.168.0.2 IEEE ● 3 • • cl Assume that IP flows exist between every source-destination pair in this network. The following routing rules must be implemented in this network: Switch MAC MAC Eth VLAN IP Port src dst type ID Src $5 • All traffic between h1 to h4 or h5 (in both directions) must travel through route s1-s2-s5-s4 ● Web traffic between clients on h1 and an HTTP server on h3 (queries and responses) must travel through route s1-s2-s5. Web traffic between clients on h2 and an HTTP server on h3 (queries and responses) must travel through route s1-s3-s5. h3:10.0.0.1 IP Dst h4: 172.16.0.1 h5: 172.16.0.2 Clients on h4 and h5 must be blocked from accessing the HTTP server on h3. All other IP traffic (except those mentioned in the above) between hosts in this network should go through the shortest path route (minimum number of hops). If there are two paths with equal number of hops, choose the one that uses the next- hop switches with a lower index (e.g. s2 is given preference over s3) IP Prot Determine the flow table entries that must be installed in each switch (s1, s2, s3, s4 and s5). Use the following format for entries: TCP TCP sport port Action Consider the following network of five hosts (h1 to h5), five Openflow switches (s1 to s5) and SDN controller c1. The black solid lines indicate physical links between devices, and the orange dashed lines indicate logical channels between the controller and OpenFlow switches. hl: 192.168.0.1 h2: 192.168.0.2 IEEE ● 3 • • cl Assume that IP flows exist between every source-destination pair in this network. The following routing rules must be implemented in this network: Switch MAC MAC Eth VLAN IP Port src dst type ID Src $5 • All traffic between h1 to h4 or h5 (in both directions) must travel through route s1-s2-s5-s4 ● Web traffic between clients on h1 and an HTTP server on h3 (queries and responses) must travel through route s1-s2-s5. Web traffic between clients on h2 and an HTTP server on h3 (queries and responses) must travel through route s1-s3-s5. h3:10.0.0.1 IP Dst h4: 172.16.0.1 h5: 172.16.0.2 Clients on h4 and h5 must be blocked from accessing the HTTP server on h3. All other IP traffic (except those mentioned in the above) between hosts in this network should go through the shortest path route (minimum number of hops). If there are two paths with equal number of hops, choose the one that uses the next- hop switches with a lower index (e.g. s2 is given preference over s3) IP Prot Determine the flow table entries that must be installed in each switch (s1, s2, s3, s4 and s5). Use the following format for entries: TCP TCP sport port Action
Expert Answer:
Answer rating: 100% (QA)
Implement flow rules for traffic between h1 and h4h5 To ensure that all traffic between h1 and h4h5 travels through route s1s2s3s4s5 we need to install flow table entries in switches s1 s2 s3 and s4 T... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0133594140
7th edition
Authors: James Kurose, Keith Ross
Posted Date:
Students also viewed these computer network questions
-
Namrata owns and operates a tour bus company called Namrata, LLC. Namrata is an experienced commercial driver who specializes in transporting music groups from city to city. While transporting...
-
Consider the SDN Open Flow network shown in Figure 4.30. Suppose that the desired forwarding behavior for data-grams arriving at s2 is as follows: Any datgrams arriving on input port 1 from hosts h5...
-
Solve: +32 Give your answer as an interval. Enter DNE if the inequality does not have a solution. > Next Question
-
Cost information for Lake County Library is as follows. In addition to directly traceable costs, the library incurred $24,000 for a building lease. REQUIRED A. Allocate to departments any costs that...
-
Consider the film speed data in Exercise 10-24. Test H0: 2/1 = 2/2 versus using a = 0.02.
-
Q1 - At the heart of understanding marketing is something known as the marketing concept. In essence the marketing concept states: focus on creating transactions understand customer wants and needs...
-
Visit www.pearsonglobaleditions.com/malhotra to read the video case and view the accompanying video. Marriott: Marketing Research Leads to Expanded Offerings highlights Marriotts success in using...
-
How can the extent of price discounting be tracked on a customer-by-customer basis?
-
After spending the day packing merchandise into boxes for a makers convention, Jaime is ready to pack up their rental van and make the drive to the next town over. Jaime wants the unloading of the...
-
GigaCo. manufactures 1-GB flash drives (jump drives). Price and cost data for a relevant range extending to 200,000 units per month are as follows: Sales price per unit (current monthly sales volume...
-
The number of patient records coded by a facility's coding staff in a week would be an example of a: (check all that apply) Question options: Financial indicator Performance indicator Structure...
-
Techno-byte Ltd sells computers. At the beginning of May 2022 the business had an overdraft of R70 000 and the bank had asked that it be settled by the end of October 2022. As a result, the directors...
-
Assumes that the dividends paid by the company will continue to go up at a constant growth rate indefinitely. It helps investors determine the fair price to pay for a stock today based on future...
-
Calculate the debt ratio (total liabilities to total liabilities and owners' equity), and the debt/equity ratio (total liabilities to total owners' equity)? 11. Based on the results of your analysis...
-
1. The fixed point scheme is in such a way that xr+1 = g(xr). 2. Given f(x) = x2 - 2x - 3, 3. Generate all the possible schemes by splitting f (x). (4 Marks) 4. (Using the convergence Criterion,...
-
Given the risk-neutral process dS/S = rdt + odz, with o being constant, show that E(STST...ST | SO) = Sexp(-1(r + (k-i)o)T), for T...> T > T (b) Consider an average price at time T defined as ht= =...
-
We have discussed in class the different policies that governments can have around their exchange rates - Clean or managed float, adjusted peg, crawling peg, to name a few. Select a country of your...
-
1. Use these cost, revenue, and probability estimates along with the decision tree to identify the best decision strategy for Trendy's Pies. 2. Suppose that Trendy is concerned about her probability...
-
Why is it that voice and video traffic is often sent over TCP rather than UDP in todays Internet?
-
Consider a router that interconnects three subnets: Subnet 1, Subnet 2, and Subnet 3. Suppose all of the interfaces in each of these three subnets are required to have the prefix 223.1.17/24. Also...
-
An IKE SA and an IPsec SA are the same thing. True or false?
-
Companies are facing a great amount of change in every facet of their operations today. To remain competitive, companies must keep abreast of current developments in several areas. You recently got...
-
For each of the situations listed, identify the primary standard from the IMA Statement of Ethical Professional Practice that is violated (competence, confidentiality, integrity, or credibility.)...
-
Complete the following statements with one of the terms listed here. You may use a term more than once, and some terms may not be used at all. a. To quickly navigate to the end of the data in a...

Study smarter with the SolutionInn App


