Consider the following pseudocodes: public int bar(n) { if(n...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
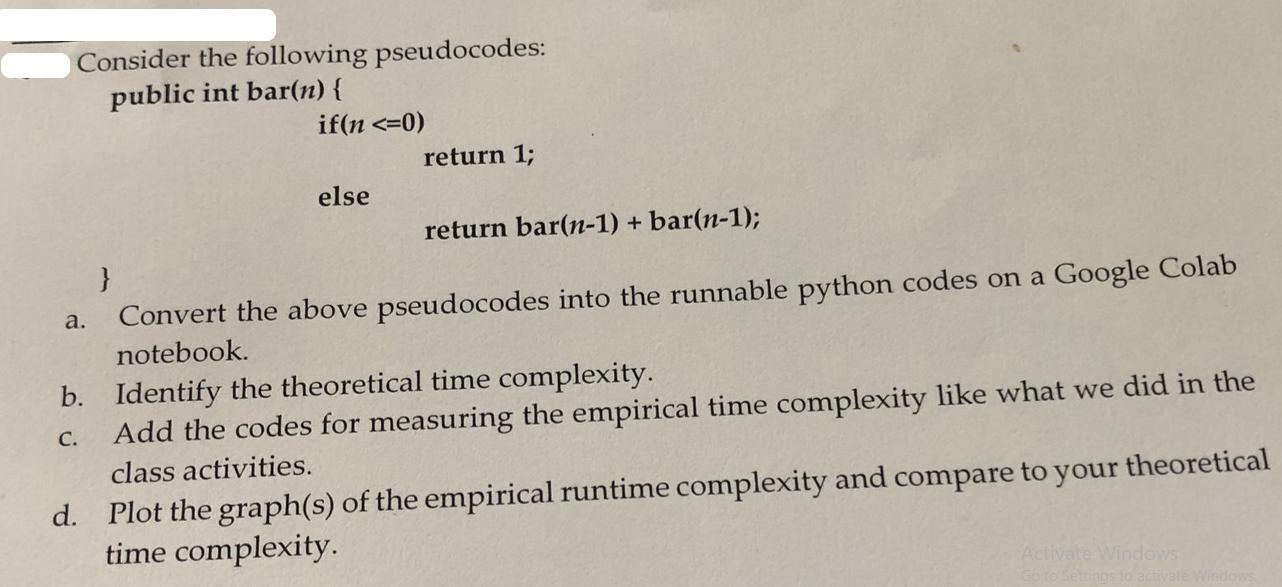
Consider the following pseudocodes: public int bar(n) { if(n <=0) a. else } return 1; return bar(n-1) + bar(n-1); Convert the above pseudocodes into the runnable python codes on a Google Colab notebook. b. Identify the theoretical time complexity. C. Add the codes for measuring the empirical time complexity like what we did in the class activities. d. Plot the graph(s) of the empirical runtime complexity and compare to your theoretical time complexity. Activate Windows Consider the following pseudocodes: public int bar(n) { if(n <=0) a. else } return 1; return bar(n-1) + bar(n-1); Convert the above pseudocodes into the runnable python codes on a Google Colab notebook. b. Identify the theoretical time complexity. C. Add the codes for measuring the empirical time complexity like what we did in the class activities. d. Plot the graph(s) of the empirical runtime complexity and compare to your theoretical time complexity. Activate Windows
Expert Answer:
Answer rating: 100% (QA)
Lets start by converting the pseudocode into a runnable Python ... View the full answer

Related Book For 

Building Java Programs A Back To Basics Approach
ISBN: 9780135471944
5th Edition
Authors: Stuart Reges, Marty Stepp
Posted Date:
Students also viewed these programming questions
-
How do you simplify the max method in the following, using the conditional operator? 1: /** Return the max of two numbers */ 2: public static int max ( int num1, int num2 ) { 3: int result; 4: 5: if...
-
Consider the table below, apply the steps of the banker's algorithm to detect the deadlock. (as we learnt in class) Request matrix, Q Allocation matrix A Available vector V R1 R2 R3 R4 R1 R2 R3 R4 R1...
-
SQL statements can be divided into two categories: data manipulation language (DML) and data definition language (DDL). Compare and contrast data manipulation and definition language and provide an...
-
1 - Describe the purpose of the bubble sort algorithm 2 - The pseudocode below shows the working of the main condition in a bubble sort algorithm, but one part of the code is missinIF items [ i ] >...
-
The following facts pertain to Lifecycle Corporation: Able owns a parcel of land (Land A) having a $30,000 FMV and $16,000 adjusted basis. Baker owns an adjacent parcel of land (Land B) having a...
-
Carlisle Co. is a U.S. firm that is about to purchase a large company in Switzerland at a purchase price of $20 million. This company produces furniture and sells it locally (in Switzerland), and it...
-
If you owned stock in a publicly traded company, in which group of companies in Exhibit 8-3 would you want your company to be? Assume Elizabeth buys the Boardman stock and consistently earns an 8...
-
Given the following project to landscape a new building site, (a) Draw a Gantt chart using MSP. (b) Find the critical path and project duration in days. (c) Given that each resource is assigned 100%...
-
Onshore Bank has $24 million in assets, with risk-adjusted assets of $14 million. Core Equity Tier 1 (CET1) capital is $750,000, additional Tier I capital is $130,000, and Tier II capital is...
-
The book balance in the checking account of Lyles Salon as of November 30 is $3,282.95. The bank statement shows an ending balance of $2,127.00. By examining last months bank reconciliation,...
-
Motivation refers toa process of inducing and stimulating an individual to act in certain manner. Discuss.
-
What are the benefits and drawbacks of using Building Information Modeling (BIM) in the construction management process, and how does BIM impact project coordination and communication among...
-
Steven and Brandon are best friends who enjoy travel. When driving through a seemingly empty road their Jeep is hit with a blast of materials. The materials hit the Jeep when a city construction...
-
1. Please provide your explanation of the text of the Rule stating that evidence must be relevant, and provide the rule number. Please provide the Rule number defining hearsay. 4. What are "writings"...
-
In a seminar held by Marketing Science Institute, two executives from Kantar analytics share how they use search, social, eCommerce, and online data to identify growth opportunities and drive...
-
Provide thorough information below when it comes to Roe vs Wade: Background Material (including lower court proceedings and how the cases have fared as they made their way through the judicial system...
-
to be auto-discovered, understood and visualized to be monoged effectively. Monitoring multiple data sources like flow packet, SNMP, performance, REST, non-SNMP, etc.. because there are many...
-
Explain briefly what is meant by electronic data interchange (EDI). How does EDI affect a companys audit trail?
-
Write a method called allDigitsOdd that returns whether every digit of a positive integer is odd. Return true if the number consists entirely of odd digits (1, 3, 5, 7, 9) and false if any of its...
-
Write a method called deleteBack that deletes the last value (the value at the back of the list) and returns the deleted value. If the list is empty, throw a NoSuchElementException.
-
Evaluate the following expressions: a. Math.abs(1.6) b. Math.abs(2 + 4) c. Math.pow(6, 2) d. Math.pow(5 / 2, 6) e. Math.ceil(9.1) f. Math.ceil(115.8) g. Math.max(7, 4) h. Math.min(8, 3 + 2) i....
-
In 2013, Verizon Communications Inc. owned 55 percent of Verizon Wireless, and the noncontrolling interest reported in Verizons financial statements is Vodafone Group Plcs 45 percent interest in...
-
Suzlon, a subsidiary of Patni, provides services to Patni. During 2016, Suzlon charged \($3,000,000\) for services provided to Patni. Cost of the services provided was \($2,100,000.\) How should the...
-
A parent makes an interest-bearing loan to its 90%-owned subsidiary in 2016, which is still outstanding in 2017. The eliminating entries (I) on the consolidation working paper for 2017, related to...

Study smarter with the SolutionInn App