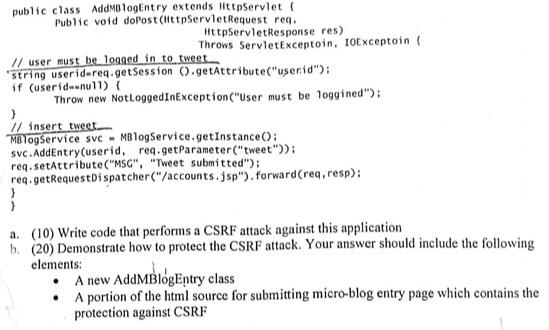
Consider the following servlet implementing a micro-blog entry public class AddMBlogEntry extends HttpServlet ( Public void doPost(HttpServletRequest
Fantastic news! We've Found the answer you've been seeking!
Question:
Consider the following servlet implementing a micro-blog entry
Transcribed Image Text:
public class AddMBlogEntry extends HttpServlet ( Public void doPost(HttpServletRequest req.. HttpServletResponse res) Throws ServletExceptoin, IOExceptoin ( // user must be logged in to tweet string userid-req.getSession ().getAttribute("userid"); if (userid=null) { Throw new NotLoggedInException ("User must be loggined"); } // insert tweet. MBlogService svc MBlogService.getInstance(): svc.AddEntry(userid, req.getParameter("tweet")); req.setAttribute("MSG", "Tweet submitted"); req.getRequestDispatcher("/accounts.jsp"). forward (req, resp); a. (10) Write code that performs a CSRF attack against this application. b. (20) Demonstrate how to protect the CSRF attack. Your answer should include the following elements: A new AddMBlogEntry class A portion of the html source for submitting micro-blog entry page which contains the protection against CSRF public class AddMBlogEntry extends HttpServlet ( Public void doPost(HttpServletRequest req.. HttpServletResponse res) Throws ServletExceptoin, IOExceptoin ( // user must be logged in to tweet string userid-req.getSession ().getAttribute("userid"); if (userid=null) { Throw new NotLoggedInException ("User must be loggined"); } // insert tweet. MBlogService svc MBlogService.getInstance(): svc.AddEntry(userid, req.getParameter("tweet")); req.setAttribute("MSG", "Tweet submitted"); req.getRequestDispatcher("/accounts.jsp"). forward (req, resp); a. (10) Write code that performs a CSRF attack against this application. b. (20) Demonstrate how to protect the CSRF attack. Your answer should include the following elements: A new AddMBlogEntry class A portion of the html source for submitting micro-blog entry page which contains the protection against CSRF
Expert Answer:
Answer rating: 100% (QA)
AddMBlogEntry class import javaioIOException import javaioNotActive Exception import javaxservletSer... View the full answer

Related Book For 

Data Structures and Algorithms in Java
ISBN: 978-1118771334
6th edition
Authors: Michael T. Goodrich, Roberto Tamassia, Michael H. Goldwasser
Posted Date:
Students also viewed these accounting questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Consider the following two scenarios: Scenario I: Over the 20112015 period, Micro Systems, Inc., spends $10 million a year to develop patents on new computer hardware manufacturing technology. While...
-
Consider the micro scale apparatus shown in the figure on the next page. This apparatus is designed to deliver a small, steady stream of methanol (MeOH) vapor to a separate device that reforms the...
-
Each team member is to become an expert on one depreciation method to facilitate teammates' understanding of that method. Follow these procedures: a. Each team member is to select an area of...
-
Explain how the general classification criteria are applied to leases that involve land.
-
What do workers around the world want in a job? An EY global study of full-time workers on work-life challenges found that one of the most important factors when seeking a job is flexibility, with...
-
Tax-deductibility of clean-up costsasset or liability? The IRS [US Inland Revenue Service] reversed its position on the accounting treatment of environmental clean-up costs in Revenue Ruling 94-38....
-
Consider a long bar of square cross section (0.8 m to the side) and of thermal conductivity 2 W/m K. Three of these sides are maintained at a uniform temperature of 300C. The fourth side is exposed...
-
24. At the end of a capital budgeting project, the asset has a book value of $50,000 and is sold for a $10,000 gain before income taxes. The company's tax rate is 35%. What is the after tax cash flow...
-
Maintenance at a major theme park in central Florida is an ongoing process that occurs 24 hours a day. Because it is a long drive from most residential areas to the park, employees do not like to...
-
(a) Explain the concession or build own transfer transactions in project finance (4 marks) (b) Outline the structure of Build Own Transfer projects (10 marks) (c) List and explain the types of...
-
You are cotton farmer. Trace the supply chain from farming cotton to the end result of a Tee- shirt sold on the Boardwalk at the shore. What problems would you encounter in every step of the supply...
-
Camnet Industry is considering introducing a new line of higher end produces. Below are the company's forecast of financial data for the new products. Price per unit: $15 Quantity: ...
-
Pastoral Bakery produces an expensive variety of sourdough bread. The process for baking this bread consists of five steps, which are followed from start to finish for 50 loaves at a time. Once 50...
-
The company's "high fidelity" can produce 40 high-quality turntables per day at an average total cost of $100 per turntable. The marginal cost function is MC(Q) = 2.5. What is the total cost to...
-
There is a series of robberies of jewellery shop outlets owned by a single company. The company investigates the robberies rigorously and is unable to identify any suspects or leads. As a result, the...
-
S MySeneca homepage X 8 F 38 E Priva Tern X Content learn.senecacollege.ca/ultra/courses/_664675_1/cl/outline Remaining Time: 2 hours, 28 minutes, 24 seconds. * Question Completion Status: 2. X 5. 1....
-
When the concentration of a strong acid is not substantially higher than 1.0 10-7 M, the ionization of water must be taken into account in the calculation of the solution's pH. (a) Derive an...
-
Redo the justification of Proposition 7.2 assuming that the the cost of growing the array from size k to size 2k is 3k cyber-dollars. How much should each push operation be charged to make the...
-
Give a simple adapter that implements the stack ADT while using an instance of a deque for storage.
-
An array A contains n integers taken from the interval [0,4n], with repetitions allowed. Describe an efficient algorithm for determining an integer value k that occurs the most often in A. What is...
-
True or False. For a discrete system, the boundary conditions are to be applied explicitly.
-
Fill in the Blank. When a beam is subjected to an axial force (tension), it ____________ the natural frequency.
-
Free end a. Bending moment \(=0\); shear force equals the b. Deflection \(=0\); slope \(=0\) c. Deflection \(=0\); bending moment \(=0\) d. Bending moment \(=0\); shear force \(=0\)

Study smarter with the SolutionInn App