Consider the following sponsored search auction instance I: 2 slots. The top slot has a...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
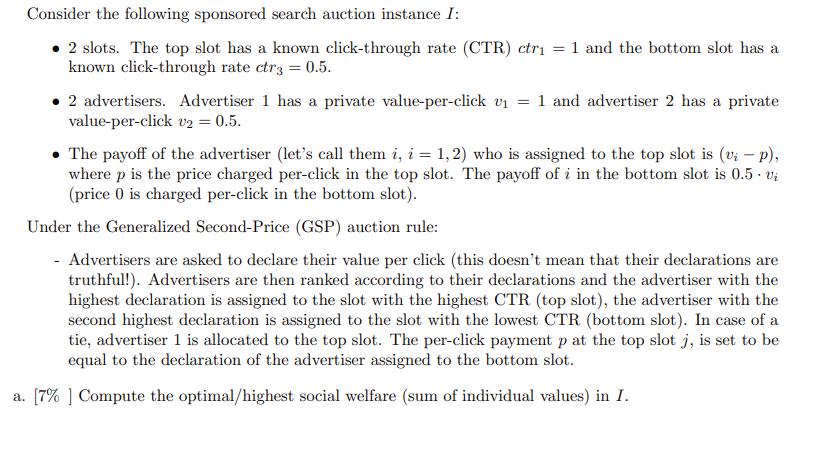
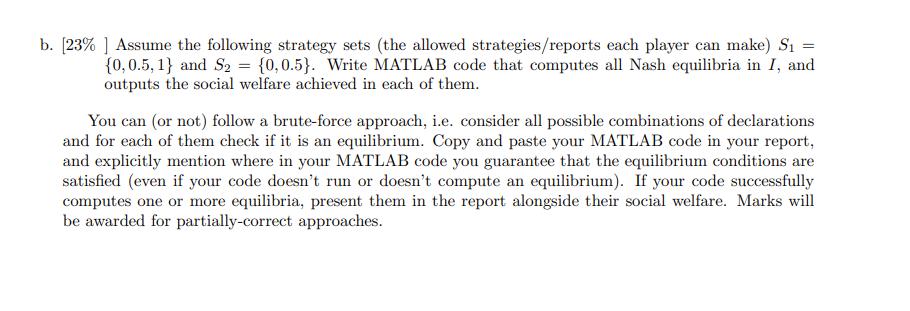
Consider the following sponsored search auction instance I: • 2 slots. The top slot has a known click-through rate (CTR) ctri = 1 and the bottom slot has a known click-through rate ctr3 = 0.5. . 2 advertisers. Advertiser 1 has a private value-per-click v₁ = 1 and advertiser 2 has a private value-per-click v2 = 0.5. • The payoff of the advertiser (let's call them i, i = 1,2) who is assigned to the top slot is (v₂ - p), where p is the price charged per-click in the top slot. The payoff of i in the bottom slot is 0.5. vi (price 0 is charged per-click in the bottom slot). Under the Generalized Second-Price (GSP) auction rule: - Advertisers are asked to declare their value per click (this doesn't mean that their declarations are truthful!). Advertisers are then ranked according to their declarations and the advertiser with the highest declaration is assigned to the slot with the highest CTR (top slot), the advertiser with the second highest declaration is assigned to the slot with the lowest CTR (bottom slot). In case of a tie, advertiser 1 is allocated to the top slot. The per-click payment p at the top slot j, is set to be equal to the declaration of the advertiser assigned to the bottom slot. a. [7%] Compute the optimal/highest social welfare (sum of individual values) in I. b. [23% ] Assume the following strategy sets (the allowed strategies/reports each player can make) S₁ = {0,0.5, 1} and S2 = {0,0.5). Write MATLAB code that computes all Nash equilibria in I, and outputs the social welfare achieved in each of them. You can (or not) follow a brute-force approach, i.e. consider all possible combinations of declarations and for each of them check if it is an equilibrium. Copy and paste your MATLAB code in your report, and explicitly mention where in your MATLAB code you guarantee that the equilibrium conditions are satisfied (even if your code doesn't run or doesn't compute an equilibrium). If your code successfully computes one or more equilibria, present them in the report alongside their social welfare. Marks will be awarded for partially-correct approaches. Consider the following sponsored search auction instance I: • 2 slots. The top slot has a known click-through rate (CTR) ctri = 1 and the bottom slot has a known click-through rate ctr3 = 0.5. . 2 advertisers. Advertiser 1 has a private value-per-click v₁ = 1 and advertiser 2 has a private value-per-click v2 = 0.5. • The payoff of the advertiser (let's call them i, i = 1,2) who is assigned to the top slot is (v₂ - p), where p is the price charged per-click in the top slot. The payoff of i in the bottom slot is 0.5. vi (price 0 is charged per-click in the bottom slot). Under the Generalized Second-Price (GSP) auction rule: - Advertisers are asked to declare their value per click (this doesn't mean that their declarations are truthful!). Advertisers are then ranked according to their declarations and the advertiser with the highest declaration is assigned to the slot with the highest CTR (top slot), the advertiser with the second highest declaration is assigned to the slot with the lowest CTR (bottom slot). In case of a tie, advertiser 1 is allocated to the top slot. The per-click payment p at the top slot j, is set to be equal to the declaration of the advertiser assigned to the bottom slot. a. [7%] Compute the optimal/highest social welfare (sum of individual values) in I. b. [23% ] Assume the following strategy sets (the allowed strategies/reports each player can make) S₁ = {0,0.5, 1} and S2 = {0,0.5). Write MATLAB code that computes all Nash equilibria in I, and outputs the social welfare achieved in each of them. You can (or not) follow a brute-force approach, i.e. consider all possible combinations of declarations and for each of them check if it is an equilibrium. Copy and paste your MATLAB code in your report, and explicitly mention where in your MATLAB code you guarantee that the equilibrium conditions are satisfied (even if your code doesn't run or doesn't compute an equilibrium). If your code successfully computes one or more equilibria, present them in the report alongside their social welfare. Marks will be awarded for partially-correct approaches.
Expert Answer:

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these databases questions
-
A police officer who is assigned to a casino refuses the assignment, claiming his Baptist religion prohibits him from gambling or being around gambling. Is he legitimately able to do so? [Endres v....
-
Let S and T be linear transformations V W, where dim V = n and dim W = m. Show that im S = im T if and only if T = SR for some isomorphism R : V V. [Show that dim(ker S) = dim(ker T) and choose...
-
Let S and T be linear operators on V and assume that ST = TS. (a) Show that imS and kerS1 are T-invariant. (b) If U is T-invariant, show that S(U) is T-invariant.
-
A firm makes three types of furniture: beds, chairs and tables. The manufacturing times required to make them, the profit and capacity available at each work centre are given below; To make one unit...
-
Sarahs house caught on fire. Through the prompt assistance of her neighbor Odessa, the fire was quickly extinguished. In gratitude, Sarah promised to pay Odessa $1,000. Can Odessa enforce this...
-
Equipment was purchased on January 2, 2014, for $24,000, but no portion of the cost has been charged to depreciation. The corporation wishes to use the straight-line method for these assets, which...
-
Which of the following terms describe the types of adjusting entries? a. Deferrals and depreciation b. Expenses and revenues C. Deferrals and accruals d. Prepaid expenses and prepaid revenues
-
The following situations suggest a strength or a weakness in e-commerce internal controls. a. Netproducts sells merchandise over the Internet. Customers input their credit card information for...
-
If interest rates rise 5% and if you own a bond with a maturity of 10years and a duration of 5with a 5% yield your bond price will change by approximately what percentage amount? A- up 5% b- down 5%...
-
The steel plane truss shown in the figure is loaded by three forces P, each of which is 490 kN. The truss members each have a cross-sectional area of 3900 mm2 and are connected by pins each with a...
-
The algebraic system reads Ax=b, where A = 2 0 -2 0 2 -1 0 -1 2 -1 0-1 2 b= -2 (a) Make a Maple procedure for Successive Over-Relaxation (SOR). (b) Perform 15 iterations of Jacobi and Gauss-Seidel...
-
Assume you are a project cost engineer calculating the cost of a repetitive activity for your project. There are a total of 20 iterations of this activity required for the project. The project...
-
Comprehensive Problem (Tax Return Problem). Carl Chubbs, age 64, earned \(\$ 85,000\) during 2018 . His wife, Dawn, age 66, is blind. During 2018, Carl and Dawn received \(\$ 1,000\) in dividends....
-
Assume the network diagram shown in Figure 11.19. Megan is responsible for activities A and C. Use the critical chain methodology to resource-level the network. What are two options for redrawing the...
-
Construct a value stream map of getting ready to go to school or work.
-
Search for student holidays (or anything else) using a search engine (e.g. Google, Bing, Yahoo!). Go to the third results page and select one of the links. Evaluate the content of this website and...
-
Assume a block cipher which operates on 4-bit blocks written as hexadecimal digits. For a particular key K it implements the following "encryption" on message m: m 0 1 2 3 4 5 5 C 7 e 6 7 8 9 a 2 a 4...
-
Use of the contraceptive Depo Provera appears to triple women's risk of infection with chlamydia and gonorrhea , a study reports today. An estimated 20 million to 30 million women worldwide use Depo...
-
What are the differences between the following types of wireless channel impairments: path loss, multi path propagation, interference from other sources?
-
Suppose Alice has a message that she is ready to seod to anyone who asks. Thousands of people want to obtain Alice's message, but each wants to be sure of the integrity of the message. In this...
-
Suppose Alice wants to communicate with Bob using symmetric key cryptography using a session key KS. In Section 8.2, we learned how public-key cryptography can be used to distribute the session key...
-
The audit procedures applied to accrued liabilities differ from those applied to accounts payable because a. Accrued liabilities balances are less material than accounts payable balances. b. Evidence...
-
Match each assertion to the related audit objective. Each assertion may be used once, more than once, or not at all. Audit objective 1. To determine whether the amount shown as invento- ries in the...
-
Audit procedures should be designed to accomplish specific audit objectives. Review the following inventory audit procedures and indicate which audit objectives are being accomplished and how. a....

Study smarter with the SolutionInn App


