Create the file /etc/sudoers.d/dbuser1 to configure dbuser1 so that the user can use sudo to run any
Fantastic news! We've Found the answer you've been seeking!
Question:
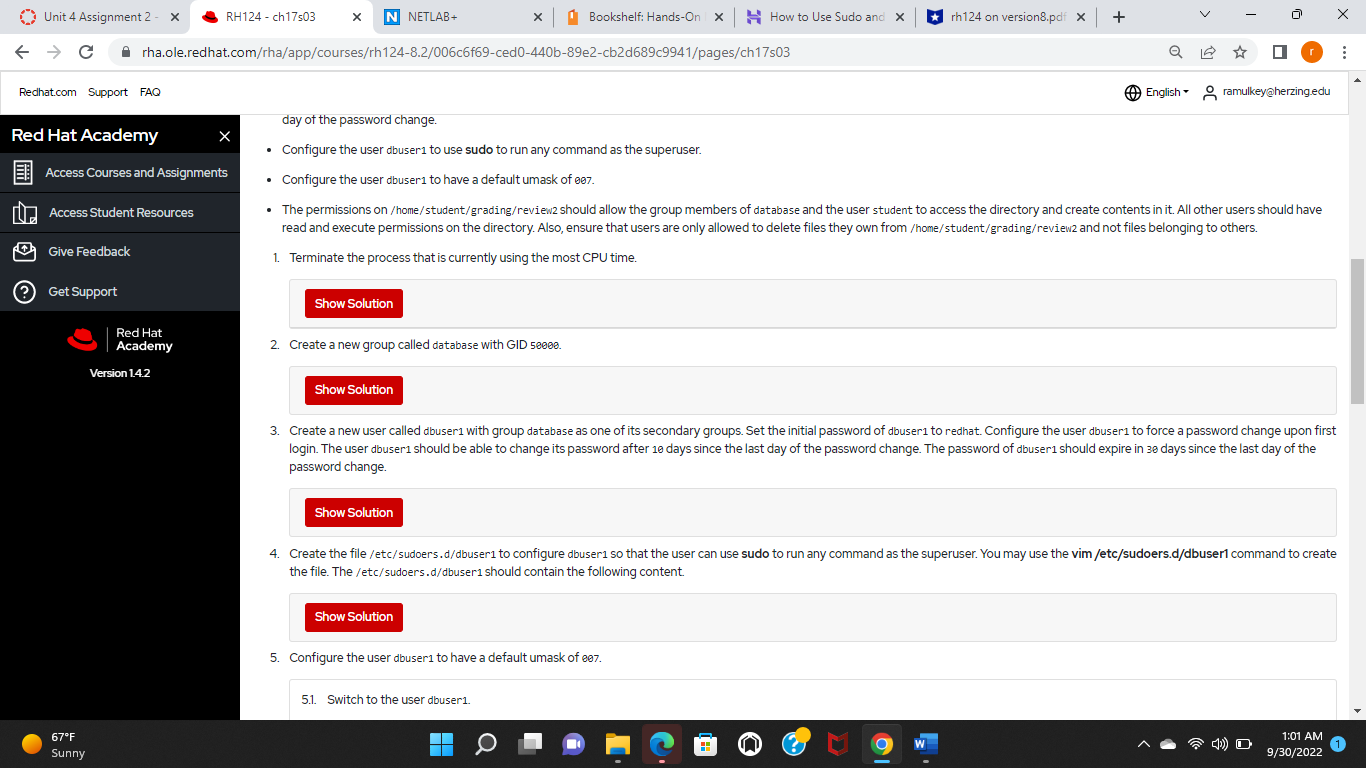
Create the file /etc/sudoers.d/dbuser1 to configure dbuser1 so that the user can use sudo to run any command as the superuser. You may use the vim /etc/sudoers.d/dbuser1 command to create the file. The /etc/sudoers.d/dbuser1 should contain the following content.
Transcribed Image Text:
Unit 4 Assignment 2 - X C Redhat.com Support FAQ !!! Red Hat Academy Access Student Resources Give Feedback Access Courses and Assignments (?) Get Support 67F Sunny RH124 - ch17s03 rha.ole.redhat.com/rha/app/courses/rh124-8.2/006c6f69-ced0-440b-89e2-cb2d689c9941/pages/ch17s03 Red Hat Academy Version 1.4.2 X X N NETLAB+ . Show Solution 2. Create a new group called database with GID 50000. Show Solution x | Show Solution day of the password change. Configure the user abuser 1 to use sudo to run any command as the superuser. Configure the user dbuser1 to have a default umask of 007. The permissions on /home/student/grading/review2 should allow the group members of database and the user student to access the directory and create contents in it. All other users should have read and execute permissions on the directory. Also, ensure that users are only allowed to delete files they own from /home/student/grading/review2 and not files belonging to others. 1. Terminate the process that is currently using the most CPU time. Bookshelf: Hands-On X Show Solution How to Use Sudo and X 5.1. Switch to the user dbuser1. 5. Configure the user dbuser1 to have a default umask of ee7. rh124 on version8.pdf x + 3. Create a new user called dbuser1 with group database as one of its secondary groups. Set the initial password of dbuser1 to redhat. Configure the user dbuser1 to force a password change upon first login. The user dbuser1 should be able to change its password after 10 days since the last day of the password change. The password of abuser1 should expire in 30 days since the last day of the password change. Q 4. Create the file/etc/sudoers.d/dbuser1 to configure dbuser1 so that the user can use sudo to run any command as the superuser. You may use the vim /etc/sudoers.d/dbuser1 command to create the file. The /etc/sudoers.d/dbuser1 should contain the following content. O English ramulkey@herzing.edu 4) O X 1:01 AM 9/30/2022 Unit 4 Assignment 2 - X C Redhat.com Support FAQ !!! Red Hat Academy Access Student Resources Give Feedback Access Courses and Assignments (?) Get Support 67F Sunny RH124 - ch17s03 rha.ole.redhat.com/rha/app/courses/rh124-8.2/006c6f69-ced0-440b-89e2-cb2d689c9941/pages/ch17s03 Red Hat Academy Version 1.4.2 X X N NETLAB+ . Show Solution 2. Create a new group called database with GID 50000. Show Solution x | Show Solution day of the password change. Configure the user abuser 1 to use sudo to run any command as the superuser. Configure the user dbuser1 to have a default umask of 007. The permissions on /home/student/grading/review2 should allow the group members of database and the user student to access the directory and create contents in it. All other users should have read and execute permissions on the directory. Also, ensure that users are only allowed to delete files they own from /home/student/grading/review2 and not files belonging to others. 1. Terminate the process that is currently using the most CPU time. Bookshelf: Hands-On X Show Solution How to Use Sudo and X 5.1. Switch to the user dbuser1. 5. Configure the user dbuser1 to have a default umask of ee7. rh124 on version8.pdf x + 3. Create a new user called dbuser1 with group database as one of its secondary groups. Set the initial password of dbuser1 to redhat. Configure the user dbuser1 to force a password change upon first login. The user dbuser1 should be able to change its password after 10 days since the last day of the password change. The password of abuser1 should expire in 30 days since the last day of the password change. Q 4. Create the file/etc/sudoers.d/dbuser1 to configure dbuser1 so that the user can use sudo to run any command as the superuser. You may use the vim /etc/sudoers.d/dbuser1 command to create the file. The /etc/sudoers.d/dbuser1 should contain the following content. O English ramulkey@herzing.edu 4) O X 1:01 AM 9/30/2022
Expert Answer:

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these computer network questions
-
Q1. You have identified a market opportunity for home media players that would cater for older members of the population. Many older people have difficulty in understanding the operating principles...
-
Design a Java class that represents a cache with a fixed size. It should support operations like add, retrieve, and remove, and it should evict the least recently used item when it reaches capacity.
-
In Exercises 6567, consider a scalar function and a vector field F in space. Determine whether the expression is a vector field, a scalar function, or neither. Explain. div[curl()]
-
Rossano, Inc., makes and sells drum sets. Nick Ross, controller, is responsible for preparing the master budget. The sales manager has given Nick the following sales forecast for the coming months....
-
A sample of lead ore contains 78.0% galena, PbS. How many metric tons of Pb can be obtained from 1.00 metric ton of the lead ore?
-
Give three examples of strategic technologies and how they can influence organizational performance.
-
Develop a chase aggregate plan for Draper using a permanent workforce of 12 employees supplemented by overtime. All demand must be met each period. (a) Show what would happen if this plan were...
-
Your team have just been assigned to a major project in its capital budgeting division. This assignment requires your team to determine the net cash flows and Net Present Value (NPV), Internal Rate...
-
This Mini Practice Set will help you review all the key concepts of the accounting cycle for a merchandising company, along with the integration of payroll. Betty Loeb took over the business now...
-
What would the outlines be for a communication plan to key stakeholders from FEMA for the water resources and siren warning system of the Lahaina, Maui wildfire and what potential roadblocks could...
-
Young screenwriter Carl Draper has just finished his first script. It has action, drama and humour, and he thinks it will be a blockbuster. He takes the script to every film studio in town and tries...
-
This question takes a step back from the quantitative analysis and makes you think about how you would manage a capital budgeting project in a firm. You have just graduated from university and taken...
-
In the accounts of P Toona, an account payable tax invoice for office equipment from G Heath for $8415 ($7650 + $765 GST) was erroneously entered and processed in the purchases journal as $5148...
-
On April 20, 2004, six lanes of the Nicoll Highway in Singapore disappeared into a 100-foot hole when a tunnel being constructed underneath the highway collapsed. Incredibly, no one was driving on...
-
What is the relationship between the one-factor model and the CAPM? In contrast to the CAPM, the APT does not indicate which factors are expected to determine the risk premium of an asset. How can we...
-
A drillstring is composed of 9,000 ft of 5-in. 19.5-lbm/ft drillpipe and 1,000 ft of drill collars having a 3.0-in. ID. Compute these items: a. Capacity of the drillpipe in barrels. Answer: 159.8...
-
Find the area of the surface generated by revolving the para- metric curve x = cos 1, y = sin? 1 (0 < I sa/2) about the y-axis.
-
Kathy Kennedy (age 44) is a single taxpayer and she lives at 212 North Pine Way, Payson, AZ 85541. Her Social Security number is 467-98-9784. Kathy's earnings and income tax withholding as the...
-
Cedar Corporation has an S corporation election in effect. During the 2012 calendar tax year, the corporation had ordinary taxable income of $200,000, and on January 15, 2012, the corporation paid...
-
Quince Interests is a partnership with a tax year that ends September 30, 2012. During that year, Potter, a partner, received $3,000 per month as a guaranteed payment, and his share of partnership...
-
Should the instruction following the TEST instruction be interruptible? If so, what must the implicit BRANCH instruction (interrupt) do?
-
It seems that there are far fewer commercial implementations of SIMD, MIMD, and MISD architectures than there were just 10 years ago. This is probably due to a variety of factors, including high...
-
GCP, Inc., has contracted you to analyze and develop commercial off-the-shelf (COTS) processors to be phased into their existing product lines. Your objective is to select four popular commercial...

Study smarter with the SolutionInn App


