Create two dictionaries to encrypt and decrypt messages, one to encode each letter and one to...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
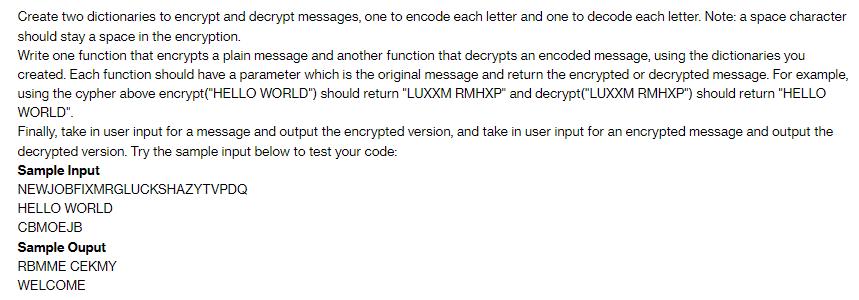
Create two dictionaries to encrypt and decrypt messages, one to encode each letter and one to decode each letter. Note: a space character should stay a space in the encryption. Write one function that encrypts a plain message and another function that decrypts an encoded message, using the dictionaries you created. Each function should have a parameter which is the original message and return the encrypted or decrypted message. For example, using the cypher above encrypt("HELLO WORLD") should return "LUXXM RMHXP" and decrypt("LUXXM RMHXP") should return "HELLO WORLD". Finally, take in user input for a message and output the encrypted version, and take in user input for an encrypted message and output the decrypted version. Try the sample input below to test your code: Sample Input NEWJOBFIXMRGLUCKSHAZYTVPDQ HELLO WORLD CBMOEJB Sample Ouput RBMME CEKMY WELCOME Create two dictionaries to encrypt and decrypt messages, one to encode each letter and one to decode each letter. Note: a space character should stay a space in the encryption. Write one function that encrypts a plain message and another function that decrypts an encoded message, using the dictionaries you created. Each function should have a parameter which is the original message and return the encrypted or decrypted message. For example, using the cypher above encrypt("HELLO WORLD") should return "LUXXM RMHXP" and decrypt("LUXXM RMHXP") should return "HELLO WORLD". Finally, take in user input for a message and output the encrypted version, and take in user input for an encrypted message and output the decrypted version. Try the sample input below to test your code: Sample Input NEWJOBFIXMRGLUCKSHAZYTVPDQ HELLO WORLD CBMOEJB Sample Ouput RBMME CEKMY WELCOME
Expert Answer:
Answer rating: 100% (QA)
To create dictionaries for encryption and decryption you can use two dictionaries where keys represe... View the full answer

Related Book For 

Java An Introduction To Problem Solving And Programming
ISBN: 9780134462035
8th Edition
Authors: Walter Savitch
Posted Date:
Students also viewed these programming questions
-
1. Who and what does the Privacy Act cover? 2. According to the Principle of Ethics and Code of Professional conduct in dentistry, answer the following questions: a) How would you maintain...
-
A stock you are evaluating just paid an annual dividend of $2.70. Dividends have grown at a constant rate of 2.4 percent over the last 15 years and you expect this to continue. a. If the required...
-
test 1 for financial analysis and budgeting 1013 lambton college fpwt
-
According to the 1980 revisions to the Copyright Act of 1976,_____. a. the owner of a copyrighted program is allowed to make multiplecopies or adaptations for use on other computers b. copyright...
-
As plastic bushings are inserted into a 3-in.-diameter cylindrical sheet metal container, the insertion tool exerts the forces shown on the enclosure. Each of the forces is parallel to one of the...
-
Consider two-bandit problem with the following reward distributions: ~ R(a) Uniform[0 1.4] R(a2) N(u=0.5, = 1) ~ a) Compute the optimal Q*(a), Q*(a) and *. b) Consider the reward distributions are...
-
For each of the following sets of data, (1) calculate the mean of the scores \(\left(\mathrm{X}^{-} ight),(2)\) calculate the deviation of each score from the mean \(\mathrm{X}-\mathrm{X}^{-}\), and...
-
How can HRM technology make a human resource department more productive? How can technology improve the quality of HRM decisions?
-
Print Company acquired 80% of the stock of Sand Corp. on January 1, 2023. The stockholder's equity section of Sand's balance sheet at that date is as follows: Stockholder's Equity Section Common...
-
Jake claims that he can buy a $210,000 for about the same as his rent, and therefore he should definitely buy because he has heard that "renting is bad". Help him walk through this argument. a....
-
Tolson Corp owns 40% of the voting common shares of Ramos Corp and has significant influence. In 2010, Tolson buys inventory costing $100,000 from third parties and then sells it Ramos for $150,000....
-
What are the different types of advances of a bank according to RBI prudential norms?
-
You are the auditors of Apollo Services Ltd. and you have recently been reading a report on a similar company that criticised the auditors for failing to comment on the existence of the material...
-
What do you mean by Auditors Report?
-
Write short notes on compulsory tax audit.
-
What special points the auditor has to consider in conducting audit in the following institutions: (a) Charitable institution. (b) Educational institution.
-
Describe functions (responsibility, roles, and duties) of DBA to handle DBMS.
-
What is removed during each of the three stages of wastewater treatment: primary, secondary, and tertiary? During which state would you expect items to be recovered that were accidentally flushed,...
-
Derive a class CombinedDiscount from DiscountPolicy, as described in Exercise 10. It should have a constructor that has two parameters of type DiscountPolicy. It should define the method...
-
Sometimes we would like a class that has just a single unique instance. Create a class Merlin that has one attribute, theWizard, which is static and of type Merlin. The class has only one constructor...
-
Write a recursive method that will compute the sum of the digits in a positive number.
-
Some have argued that social entrepreneurship is another form of commercial entrepreneurship with positive social or environmental change as its product. Do you agree with the accuracy of this...
-
What is meant by the term business model?
-
How does the lean start-up process differ from traditional business planning?

Study smarter with the SolutionInn App