CS 463/563: Cryptography for Cybersecurity Fall 2023 Homework #5 Points: 20 Consider a simple system with...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
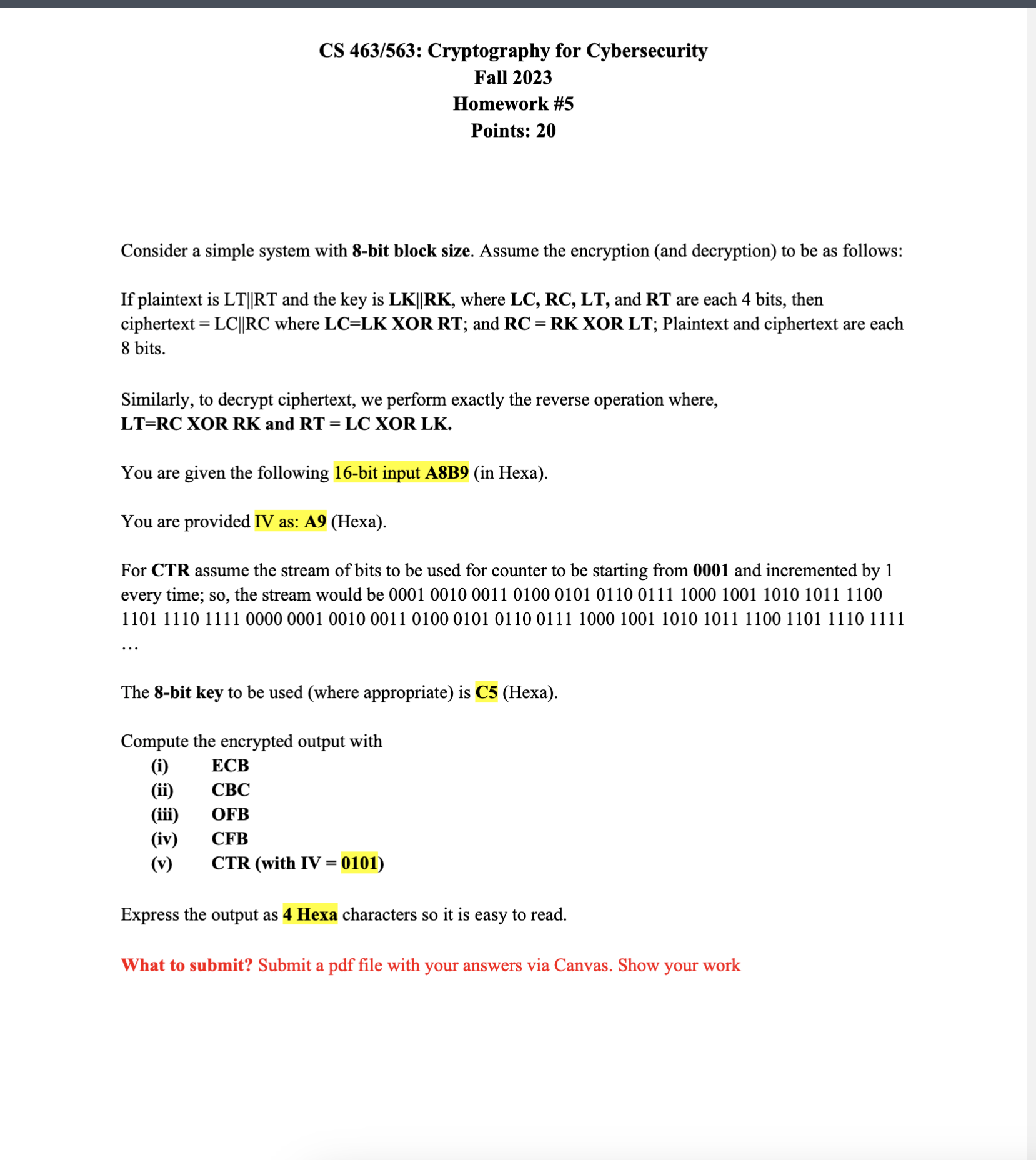
CS 463/563: Cryptography for Cybersecurity Fall 2023 Homework #5 Points: 20 Consider a simple system with 8-bit block size. Assume the encryption (and decryption) to be as follows: If plaintext is LT||RT and the key is LK||RK, where LC, RC, LT, and RT are each 4 bits, then ciphertext=LC||RC where LC=LK XOR RT; and RC = RK XOR LT; Plaintext and ciphertext are each 8 bits. Similarly, to decrypt ciphertext, we perform exactly the reverse operation where, LT=RC XOR RK and RT = LC XOR LK. You are given the following 16-bit input A8B9 (in Hexa). You are provided IV as: A9 (Hexa). For CTR assume the stream of bits to be used for counter to be starting from 0001 and incremented by 1 every time; so, the stream would be 0001 0010 0011 0100 0101 0110 0111 1000 1001 1010 1011 1100 1101 1110 1111 0000 0001 0010 0011 0100 0101 0110 0111 1000 1001 1010 1011 1100 1101 1110 1111 The 8-bit key to be used (where appropriate) is C5 (Hexa). Compute the encrypted output with (i) ECB (ii) CBC (iii) OFB (iv) CFB (v) CTR (with IV = 0101) Express the output as 4 Hexa characters so it is easy to read. What to submit? Submit a pdf file with your answers via Canvas. Show your work CS 463/563: Cryptography for Cybersecurity Fall 2023 Homework #5 Points: 20 Consider a simple system with 8-bit block size. Assume the encryption (and decryption) to be as follows: If plaintext is LT||RT and the key is LK||RK, where LC, RC, LT, and RT are each 4 bits, then ciphertext=LC||RC where LC=LK XOR RT; and RC = RK XOR LT; Plaintext and ciphertext are each 8 bits. Similarly, to decrypt ciphertext, we perform exactly the reverse operation where, LT=RC XOR RK and RT = LC XOR LK. You are given the following 16-bit input A8B9 (in Hexa). You are provided IV as: A9 (Hexa). For CTR assume the stream of bits to be used for counter to be starting from 0001 and incremented by 1 every time; so, the stream would be 0001 0010 0011 0100 0101 0110 0111 1000 1001 1010 1011 1100 1101 1110 1111 0000 0001 0010 0011 0100 0101 0110 0111 1000 1001 1010 1011 1100 1101 1110 1111 The 8-bit key to be used (where appropriate) is C5 (Hexa). Compute the encrypted output with (i) ECB (ii) CBC (iii) OFB (iv) CFB (v) CTR (with IV = 0101) Express the output as 4 Hexa characters so it is easy to read. What to submit? Submit a pdf file with your answers via Canvas. Show your work
Expert Answer:
Answer rating: 100% (QA)
Computer Science Questing Bbit key to be cised 3C hexa 22221 New We Have to compute the e... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these programming questions
-
(20 pts) Water flows into and out of the very large tank as shown. The flow is inviscid and the change in area at the outlet is abrupt such that the contraction coefficient is approximately 0.8....
-
Draw a number line analogous to Figure 1.11 for 3-bit unsigned, twos complement, and sign/magnitude numbers. -8 -7 -6 -5 -4 -3 -2 -1 1 3 6 7 8 9. 10 11 12 13 14 15 Unsigned 0000 0001 0010 0011 0100...
-
Draw a number line analogous to Figure 1.11 for 2-bit unsigned, twos complement, and sign/magnitude numbers. -8 -7 -6 -5 -4 -3 -2 -1 1 3 6 7 8 9. 10 11 12 13 14 15 Unsigned 0000 0001 0010 0011 0100...
-
You are asked to evaluate the following two projects for Boring Corporation using the NPV method combined with the PI approach, which project would you select? Use a discount rate of 10 percent....
-
What is a steady-flow process?
-
Determine vo and the required PIV rating of each diode for the configuration of Fig. 2.168. 100 V Ideal diodes -100 V 2.2 k
-
Uniform flow in a sluggish channel having a nearly rectangular cross section that is \(498 \mathrm{ft}\) wide and \(16.5 \mathrm{ft}\) deep carries a flow of \(8,250 \mathrm{ft}^{3} / \mathrm{s}\)....
-
Paul Golding and his wife, Nancy, established Crunchy Chips in 1938. (Nancy sold her piano to help raise capital to start the business.) Paul assumed responsibility for buying potatoes and selling...
-
An investor purchased $100,000 in a 5-year index-linked guaranteed investment certificate (GIC) in a non-registered account. The GIC matured at $110,000. Assuming he is in a 26% marginal tax bracket,...
-
The Springfield School Board has made the decision to close one of its middle schools (sixth, seventh, and eighth grades) at the end of this school year and reassign all of next year's middle school...
-
Becky owns a bridal accessories store. Her total revenue last year was $173,000. Her rent was $10,000, she paid workers $75,000, and her overhead expenses were $20,000. Becky knows that she could...
-
J. Smith has a note with a face value (principal) of $10,000 at 6% for 90 days. After 30 days, he discounts the note at 8%. What is his effective rate of interest? (round to nearest whole percent)
-
Boris Company has multiple business units. Unit A has the following information: sales revenue is $200,000; variable expenses are $140,000; fixed expenses are $100,000. Fixed expenses - which are...
-
Warranty work was completed for a customer. The parts to fix the product cost $2,750 and the labour was $1,550 which was paid in cash. May 1 Borrowed $12,500 from TD Bank by issuing a promissory note...
-
March 10 Virginia signed a note to Bingham Co. for $1,200 on an amount owed. The note carried a 12% interest rate for a term of 60 days. On the fifth day of the note, Bingham Co. discounted it for...
-
Rochelle Company is an Internet service provider. They own a large number of servers and other equipment, which costs $200,000 per year. Capacity costs estimates are reported on a per service hour...
-
Which of the following was NOT a characteristic of the colonial agricultural system in the Americas? A) A reliance on slave labor B) The cultivation of export crops C) The use of advanced farming...
-
Cleaning Service Company's Trial Balance on December 31, 2020 is as follows: Account name Debit Credit Cash 700 Supplies Pre-paid insurance Pre-paid office rent Equipment Accumulated depreciation -...
-
Distinguish that a basic tenet of security architectures is layered implementation of security. Thus, an organization must establish multiple layers of security controls and safeguards, which can be...
-
Explain that worms are viruses that replicate themselves like bunnies until all available resources have been exhausted. Relate to the speed that worms can spread by applying the examples of the...
-
Present that the CISSIP certification is considered the gold standard and the most prestigious certification for security managers and CISOs. Recognize that professionals must possess at least five...
-
Consider a stochastic process such that the underlying security \(S\) follows the model: \[d S_{t}=\mu S_{t} d t+\sigma_{t} S_{t} d Z_{t}\] where \(Z\) is a standard Brownian motion. Suppose the...
-
Calculate the solution to the following SDE: \[d X_{t}=\alpha\left(m-X_{t} ight) d t+\sigma d B_{t}\] with \(X_{0}=x\). The process satisfying this equation is called the meanreverting...
-
If \(X_{t} \sim N\left(0, \sigma^{2} t ight)\) and \(Y_{t}=e^{X_{t}}\), calculate the pdf of \(Y_{t}\). Calculate \(\mathbf{E}\left[Y_{t} ight]\) and \(V\left(Y_{t} ight)\). Calculate the transition...

Study smarter with the SolutionInn App


