Data gistrun sending inside a pack fills in as conventional allowing subordinate rules to execute on progressive
Question:
Data gistrun
sending inside a pack fills in as conventional allowing subordinate rules
to execute on progressive clock cycles. Correspondence between gatherings
conventionally causes a surprising difficulty of 1 or 2 clock cycles. The gathering
thought may similarly be loosened up to consolidate the issue pad (generally called the issue
window). made for John
(I) What issue does gathering try to settle?
(ii) Assume a processor has two symmetric gatherings that contain both utilitarian
units and an issue support. In this processor, headings ought to be controlled
to a particular pack before they are implanted in an issue pad. What
should the two major targets of a good directing system be?
(a) (I) Define the possibility of least pre-fixed point fix(f) of a steady endofunction
f on an area and express Tarski's appropriate point theory for it. [
(ii) State Scott's appropriate point acknowledgment rule. [
) program to process the worth of a given situation in Pascal's Triangle (See picture).
The method for processing any given position's worth is to include the numbers to the position's both ways in the previous column. For example, to process the center number in the third column, you add 1 and 1; the sides of the triangle are consistently 1 since you just add the number to the upper left or the upper not too far off (being no second number on the opposite side).
The program ought to provoke the client to enter a column and a situation in the line. The program ought to guarantee that the info is substantial prior to processing an incentive for the position.
2 ) I really want a program that, when run, will print out its source code. This source code, thus, ought to accumulate and print out itself. (Fun reality: a program that prints itself is known as a quine.)
3)given a variety of numbers, the objective is to productively find the subarray that has the best worth when its components are all added together. Note that since certain components of the exhibit might be negative, the issue isn't settled by basically picking the beginning and end components of the cluster to be the subarrray, and adding the whole exhibit.
a) In Verilog, what is the contrast between nonstop task and
non-impeding task? [4 marks]
(b) What are the circuit graphs relating to RandomBitsA and
RandomBitsB? [8 marks]
(c) What is the result from RandomBitsA and RandomBitsB? [8 marks]
4
CST.2000.4.5
6 Data Structures and Algorithms
Depict exhaustively both Prim's and Kruskal's calculations for viewing as a base expense
spreading over tree of an undirected diagram with edges marked with positive expenses, and
make sense of why they are right. [7 marks each]
Look at the general benefits of the two calculations. [6 marks]
7 Operating System Functions
For what reason is it significant for a working framework to plan circle demands? [4 marks]
Momentarily depict every one of the SSTF, SCAN and C-SCAN plate planning calculations.
Which issue with SSTF truly does SCAN look to survive? Which issue with
Examine does C-SCAN look to survive? [5 marks]
Consider a Winchester-style hard circle with 100 chambers, 4 twofold sided platters
furthermore, 25 areas for each track. Coming up next is the (time-requested) succession of solicitations
for circle areas:
{ 3518, 1846, 8924, 6672, 1590, 4126, 107, 9750, 158, 6621, 446, 11 }
The circle arm is presently at chamber 10, moving towards 100. For every one of SSTF,
Sweep and C-SCAN, provide the request wherein the above solicitations would be adjusted.
[3 marks]
Which variables do the above circle arm booking calculations disregard? How should
these be considered? [4 marks]
Talk about manners by which a working framework can build legitimate volumes which are
(a) more dependable and (b) better execution than the fundamental equipment.
[4 marks]
5 [TURN OVER
CST.2000.4.6
8 Computation Theory
Allow N to be the regular numbers {0, 1, 2 . . .
What is implied by every one of the accompanying assertions?
? The subset S ? N is recursive.
? The subset S ? N is recursively enumerable.
[5 marks]
How might you expand the meaning of recursive identification to sets of processable
capabilities? [3 marks]
A grouping of regular numbers is a complete capability s : N ? N. The arrangement is
recursive if and provided that s is processable.
A limited succession ? of regular numbers is determined by a couple (l, x), where l ? N is
the quantity of components, and x : [1, l] ? N is a capability that characterizes those components.
The case l = 0 characterizes the invalid succession.
In every one of the accompanying cases, lay out whether the set characterized is recursively
enumerable:
(a) the arrangement of all recursive subsets of N [5 marks]
(b) the arrangement of all recursive successions of normal numbers [2 marks]
(c) the arrangement of all limited groupings of normal numbers [5 marks]
6
CST.2000.4.7
9 Numerical Analysis I
Characterize the outright blunder ?x and relative mistake ?x in addressing a number x. How
are these blunders related? Which sort of blunder is related with the term loss of
importance? Characterize machine epsilon ?m.
(a) (I) In a Hopfield brain network designed as a cooperative memory, with
All its loads prepared and fixed, what three potential ways of behaving may
happen over the long haul in setup space as the net keeps on emphasizing in
reaction to a given info? [3 marks]
(ii) what number stable substance addressable recollections would you expect a completely
associated Hopfield network comprising of 100 neurons to be prepared to do
putting away? [1 mark]
(iii) What property of those memory examples would make it generally plausible
that you could effectively prepare the organization to store the most extreme
number, and why? [3 marks]
(b) Explain how five free elements of visual handling are multiplexed
together into the three accessible spatial components of brain tissue, by the
construction of the cubic millimeter hypercolumns in the mind's visual cortex.
[5 marks]
(c) The retina is many times viewed as a picture catch gadget; however it has about
100 million info sensors (photoreceptors) yet just 1 million result strands
(optic nerve axons). What are a ramifications of this 100-to-1 proportion of
input channels to yield channels? [4 marks]
(d) Provide some quantitative proof and contentions supporting the suggestion
that: "Availability is the essential computational standard in the cerebrum".
[4 marks]
8 Computer Systems Modeling
(a) What standards would you consider while choosing between a model in light of
queueing hypothesis and one in view of reenactment? When could you utilize both
approaches? [5 marks]
(b) Describe the design of a discrete occasion test system. What is the head
information structure included? [5 marks]
(c) A queueing network is described by a bunch of visit counts, Vi
, furthermore, per-visit
administration prerequisites, Si
, for every one of N gadgets. Infer upper limits on the
framework throughput (I) when the heap is exceptionally low and (ii) as the heap tends to
limitlessness. [5 marks]
(d) In what circumstances may the limits be especially uncertain? What can be
done to build more tight limits for the framework throughput?
Skip Question
Show 1 Comment
Report Issue
(a) What is an information reserve and how can it contrast from a guidance store?
[4 marks]
(b) What factual properties of memory access do reserves exploit to convey
further developed execution? [4 marks]
(c) What effect will a working framework oversaw setting switch have on reserve
hit rate? Legitimize your response. [4 marks]
(d) Modern work area and server processors support concurrent multithreading
(additionally called hyperthreading). At the point when will there be an exhibition benefit in
booking two non-intelligent applications on the equivalent hyperthreaded processor
center so they run in equal as opposed to running consecutively, one work one
after the other? [4 marks]
(e) For level-1 data holds using a snoopy store coherency show, is a make back
then again a make through methodology bound to be used?
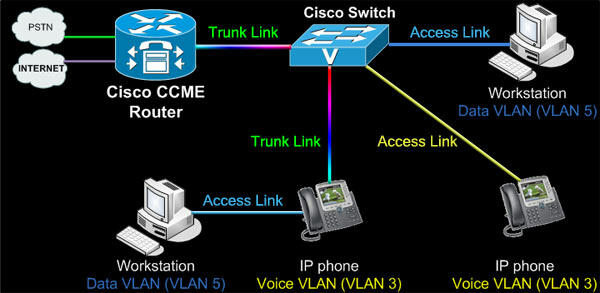
(a) What is the distinction among directing and sending? [2 marks]
(b) Routing calculations can be either interface state or distance-vector. Characterize these two
terms and make sense of the compromises between them. [6 marks]
(c) You are expected to plan a geography revelation convention for an organization of
exchanging hubs interconnected by joins. There are n hubs, l connections, the
greatest level of any hub is k and there is a way between any two hubs of
not more than d bounces. All connections are bi-directional.
Every hub has a remarkable identifier of four bytes which it knows.
(I) Describe a convention for a hub to find out about its nearby neighbors.
You ought to indicate the arrangement of your messages and the size of any message
fields. [4 marks]
(ii) Using the qualities of the organization portrayed above, plan a convention
for disseminating this data across the organization. It would be ideal for you to determine
the configuration of your messages and the size of any message fields
This question connects with double requirement fulfillment issues (CSPs). A CSP has
a set X = {x1, . . . , xn} of factors, each having a space Di = {v1, . . . , vni
} of
values. What's more, a CSP has a set C = {C1, . . . , Cm} of limitations, each relating
to a subset of X and determining the permissible mixes of tasks to the
factors in that subset.
(a) Give an overall meaning of an answer for a CSP. [1 mark]
(b) Given a parallel CSP, characterize how it affects a coordinated curve xi ? xj between
factors xi and xj to be circular segment steady. [2 marks]
(c) Give an illustration of how a coordinated curve xi ? xj can neglect to be bend predictable.
Make sense of how this can be fixed. [2 marks]
(d) Describe the AC-3 calculation for authorizing curve consistency. [5 marks]
(e) Prove that the time intricacy of the AC-3 calculation is O(n
2d
3
) where d is the
size of the biggest space. [3 marks]
(f ) Suggest a manner by which the idea of curve consistency, otherwise called
2-consistency can be stretched out to sets of three, instead of two factors. In the
rest of the inquiry we will allude to this as 3-consistency. [1 mark]
(g) Give an illustration of how a bunch of three factors could neglect to be 3-predictable,
also, show how 3-consistency could then be forced. [2 marks]
(h) Suggest a changed variant of the AC-3 calculation that can be utilized to uphold
3-consistency.
Given a succession of focuses (Vi)
n
i=0 on a plane, consider the issue of introducing
a smooth bend through every one of the places all together by building a succession of
polynomial parametric capabilities, one for every span [Vi
, Vi+1]
n?1
i=0 .
(a) What is implied by Ck congruity at the intersection between two bend portions?
[2 marks]
(b) Explain how the level of the polynomial capability for a bend section obliges
the progression at its two closures. What progression can be accomplished at each finish of
a cubic fragment? [4 marks]
(c) Derive a cubic parametric capability for the span [Vi
, Vi+1] where 0 < I < n?1.
[10 marks]
0 will contain the precomputed values for this inquiry. In
this way the normal and costly question can be responded to by a solitary key-based
peruse. (Note: Sum ought to be 0 on the off chance that no matching records exist.)
(a) Explain how the activity embed (a, b) into S can be accurately carried out in
the {S
0
, R, T} data set. [4 marks]
(b) Explain how the activity embed (c, v) into T can be accurately executed in
the {S
0
, R, T} information base. [4 marks]
(c) Explain how the activity embed (a, c) into R can be accurately executed in
the {S
0
, R, T} information base. [4 marks]
(d) For an OLTP information base, examine the exhibition ramifications of this supposed
streamlining. [4 marks]
(e) This model represents a major compromise in the plan and execution of data set applications. Examine. [4 marks]
6
CST.2014.4.7
6 Databases
(a) We are given a social pattern R(A, B, C, D, E) and told that the accompanying
table addresses a lawful case of R.
A B C D E tuple number
1 2 5 4 3 (#1)
1 4 5 4 4 (#2)
2 4 5 4 5 (#3)
2 5 5 4 3 (#4)
Which of the accompanying arrangements of practical conditions might hold in R? If a set
of conditions can't hold, then make sense of why. You can allude to tuple numbers
in your clarification.
(I) F1 is the set {A ? D}. [2 marks]
(ii) F2 is the set
A, B ? C
E ? B
D, E ? A
[2 marks]
(iii) F3 is the set
A, B ? C
D, E ? C
A ? D
[4 marks]
(b) We are given a social diagram R(Z, W, Y). Assume that in some (right)
occasion of R the inquiry
(?Z,W(R) ? ?Z,Y(R)) ? R
isn't vacant. What might we at any point close about the practical reliance Z ? W?
Make sense of your response. [4 marks]
(c) during the time spent utilizing practical conditions to standardize an outline, what
is implied by a lossless join deterioration and how is such a disintegration
ensured? [4 marks]
(d) In mapping standardization, is Boyce-Codd Normal Form (BCNF) consistently to be
liked over third Normal Form (3NF)? Make sense of your response.
: Compose program to peruse a string and show its length (number of characters).
in c+
: Compose program to peruse a letter and demonstrate whether the letter is 'a' or not.
programing language is VB8
compose program to peruse in a string from the console and show the entire string in reverse
(a) Describe the arrangements of the Data Protection Act. [8 marks]
(b) You are planning and are going to send off a cell phone application which will look for
to comprehend the profound state of the client, utilizing various information sources, for example,
movement detecting, look acknowledgment, voice pressure estimation and the
investigation of entered text. Its proclaimed intention is to empower administrations to communicate
more empathically with clients. You propose to adapt it by serving promotions at
times when the client is bound to purchase. Your "patrons" have raised a worry
that this application will actually want to analyze misery, and that in outcome you
might be putting away significant measures of delicate individual data.
Examine this issue from the perspectives of the two information assurance regulation and morals.
(a) Windows carries out static legacy for the entrance control arrangements of NTFS records
furthermore, envelopes.
(I) What does static legacy mean here and how can it contrast from dynamicinheritance? [4 marks]
(ii) Five flag bits (ci,oi,np,io,i) in each NTFS access-control entry (ACE)
manage how it is inherited. Briefly describe the purpose of each bit.
[5 marks]
(iii) User mike gives his folder project the following access-control list:
project
AllowAccess mike: full-access (oi,ci)
AllowAccess alice: read-execute (ci,np)
AllowAccess bob: read-only (oi)
It contains one folder and two text files, none of which have any noninherited access-control entries:
project\doc.txt
project\src
project\src\main.c
For each of these three objects, list all inherited access-control entries,
showing in parentheses the inheritance-control flag bits that are set (using
the same notation as above). [5 marks]
(b) Describe the purpose and four typical functions of a root kit.
Data Structures and Algorithms (a) Describe and justify an algorithm for finding the shortest distance between each pair of vertices in an undirected graph in which each edge has a given positive length. If there is no path between a pair of vertices a very large result should arise. [12 marks] (b) Is it sensible to use your algorithm to discover whether such a graph is connected? Suggest an alternative that would be appropriate for a graph of 1000 vertices and 10,000 edges.
Computer Design (a) What is a pipeline bubble and why might a branch instruction introduce one or more bubbles? [4 marks] (b) Explain, with the aid of an example, how conditional instructions may be used to reduce the number of bubbles in a pipeline. [4 marks] (c) What is the difference between branches, interrupts, software interrupts (initiated by a SWI instruction on the ARM) and exceptions? [8 marks] (d) What is an imprecise exception and why might a processor designer prefer it to a precise exception mechanism?
Digital Communication I Information is to be conveyed from A to B using automatic repeat request (ARQ), forward error correction (FEC), and lossless compression. (a) Explain the terms ARQ, FEC and lossless compression. [5 marks] (b) If we consider each of these functions to be operating at different protocol layers, what would be the most sensible ordering of the layers, and why? [5 marks] (c) Suppose: ? The underlying bit channel has a capacity of B, a delay ? and error rate 0. ? The compression ratio is C < 1. ? The FEC has rate R < 1 and given an error rate 0 provides an error rate 1 (which is detected). ? The ARQ protocol has a window size of W. At what rate can the information be conveyed? [Hint: Consider when retransmissions are made.] State any assumptions you make about the operation of the ARQ protocol.
4 Computer Graphics and Image Processing (a) Describe the limitations of human vision in terms of: (i) spatial resolution (ii) luminance (iii) colour and explain the implications that each of these limitations has on the design of display devices. [10 marks] (b) In image compression we utilise three different mechanisms to compress pixel data: (i) mapping the pixel values to some other set of values (ii) quantising those values (iii) symbol encoding the resulting values Explain each mechanism, describe the way in which it helps us to compress the image, and describe in what way it affects the visual quality of the resulting (decompressed) image when compared with the original. [10 marks] SECTION B 5 Comparative Programming Languages (a) Outline the main innovations that are in Simula 67 but were not in Algol 60, paying particular attention to Simula Classes. [6 marks] (b) Illustrate how Simula can be used to simulate a small restaurant with six tables, two waiters and small groups of customers arriving at random intervals. You need specify only the classes you would define. Most of the algorithmic details may be omitted. [6 marks] (c) Discuss to what extent Simula has been made redundant by the development of modern object-oriented languages such as Java.
Databases (a) Explain how to describe the structure of a collection of data using entities, attributes and relationships. [6 marks] (b) How would you identify particular instances of data in order to record the information in a database? Illustrate your answer by considering both a relational database maintained using SQL-92 and an ODMG database. [6 marks] (c) A high street bank has just announced a merger with a nationwide building society. You are employed as a consultant to advise on the integration of their client databases. Both institutions use relational databases. Write brief notes to alert the database administrators to the difficulties that they may encounter. [8 marks] SECTION C 9 Semantics of Programming Languages (a) The integer expressions E of a programming language are given by E ::= n | X | ?E | E + E where n ranges over integer constants and X ranges over identifiers. Explain the principle of structural induction for proving that some property ?(E) holds for all integer expressions E. [5 marks] (b) Taking states to be finite partial functions mapping identifiers to integer constants, define a relation E, s ? n giving the result n (if any) of evaluating integer expression E in state s. [7 marks] (c) Use structural induction to prove that if E, s ? n1 and E, s ? n2 both hold, then n1 = n2. [Hint: Consider the property ?(E) given by ?s, n1, n2((E, s ? n1) & (E, s ? n2) ? n1 = n2).] [7 marks] (d) What property of the pair E, s ensures that there is some n for which E, s ? n holds?
A novice SystemVerilog programmer has written the following decimal counter
module which should zero the decimal_count on reset and then, when enabled,
increment modulo 10 the decimal_count on every positive clock edge.
module count_decimal_wrong(
input logic clk;
input logic reset;
input logic enable;
output logic decimal_count);
always_comb @(posedge clk or reset)
if(enable)
begin
decimal_count = decimal_count+1;
if(decimal_count>9)
decimal_count = 0;
end
elsif(reset)
decimal_count = 0;
endmodule // count_decimal_wrong
Ray tracing works by firing one or more rays from the eye point through each pixel. The colour assigned to a ray is the colour of the first object that it hits, determined by the object's surface properties at the ray-object intersection point, the illumination at that point, and contributions from any reflection or refraction that occurs at that point. The colour of a pixel is some average of the colours of all the rays fired through it. The power of ray tracing lies in the fact that secondary rays are fired from the ray-object intersection point to determine its exact illumination (and hence colour). This spawning of secondary rays allows reflection, refraction, and shadowing to be handled with ease. A simple raytraced image can be seen in Figure 1 and the basic algorithm in Figure 13. Ray tracing's big disadvantage is that it is slow. It takes minutes, or hours, to render a reasonably detailed scene. Ray tracing was first implemented in hardware by a Cambridge company, Advanced Rendering Technologies2 , in the late 1990s. The quality of the images that they can produce is high compared with polygon scan conversion. This is their main selling point. However, ray tracing is so computationally intensive that it is not possible to produce images at the same speed as hardware assisted polygon scan conversion. Other researchers are trying to do this by using multiple processors (dozens to hundreds), but ray tracing will always be slower than polygon scan conversion. Ray tracing therefore is only used where the visual effects cannot be obtained using polygon scan conversion. This means that it is, in practice, used by a minority of movie and television special effects companies, advertising companies, and enthusiastic amateurs. 1.1.2 Example The kitchen in Figure 2 was rendered using the ray tracing program Rayshade3 . Rayshade has not been updated for over a decade. An alternative ray tracer, which is kept up to date, is POVray4 , with which you may like to experiment. It is worth visiting the POVray website to see the stunning imagery which has been produced using the ray tracer . The close-ups of the kitchen scene in Figures 3 and 4 show some of the power of ray tracing. The kitchen sink reflects the wall tiles. The bench top in front of the kitchen sink has a specular highlight on its curved front edge. The washing machine door is a perfectly curved object (impossible to achieve with polygons). The inner curve is part of a cone, the outer curve is a cylinder. You can see the floor tiles reflected in the door. Both the washing machine door and the sink basin were made using CSG techniques (see section 8.2). The grill on the stove casts interesting shadows (there are two lights in the scene). This sort of thing is much easier to do with ray tracing than with polygon scan conversion. 2http://www.artvps.com/ 3http://graphics.stanford.edu/?cek/rayshade/rayshade.html 4http://www.povray.org/ 6 Advanced Graphics Lecture Notes Figure 2: A ray traced model of a kitchen design. Figure 3: A close up of the kitchen sink. Figure 4: Close up views of the washing machine door and the grill on the stove. Neil Dodgson 7 Figure 5: A scan converted model of a city (courtesy of Jon Sewell). 1.1.3 Polygon scan conversion This term encompasses a range of algorithms where polygons are rendered, normally one at a time, into a frame buffer. The term scan comes from the fact that an image on a CRT is made up of scan lines. Examples of polygon scan conversion algorithms are the painter's algorithm, the z-buffer, and the A-buffer (see your Part IB lecture notes, FvDFH chapter 15, or F&vD chapter 15). In this course we will generally assume that polygon scan conversion refers to the z-buffer algorithm or one of its derivatives, such as the A-buffer. The advantage of polygon scan conversion is that it is fast. Polygon scan conversion algorithms are used in computer games, flight simulators, and other applications where interactivity is important. To give a human the illusion that they are interacting with a 3D model in real time, you need to present the human with animation running at 10 frames per second or faster for passive viewing on a monitor, TV, or movie screen. Research at the University of North Carolina5 has experimentally shown that for immersive virtual reality applications this is not high enough and at least 15 frames per second is a minimum. Polygon scan conversion is capable of providing this sort of speed. The NVIDIA6 GeForce8 graphics processing unit (GPU) architecture, for example, has up to 128 parallel stream processors running at 1.35GHz. It can render up to 36.8 billion textured pixels per second, and can render scenes containing several million triangles in real time. While we might hope that scientific or medical applications were considered important applications of computer graphics, it is the game industry that is driving the development of graphics card technology. One problem with polygon scan conversion is that it can only support simplistic lighting models, so images do not necessarily look realistic. For example: transparency can be supported, but refraction requires the use of a texture-mapping technique called "refraction mapping"; reflections can be supported, at the expense of rendering a "reflection map" before rendering the scene; shadows can be produced using "shadow maps". All of these are more complicated methods than those used in ray tracing. Where ray tracing 5http://www.cs.unc.edu 6http://www.nvidia.com/ 8 Advanced Graphics Lecture Notes Figure 6: An SGI O2 computer and components drawn with and without texture maps. Figure 7: Left: some floating objects in a simulated environment. Right: a close up of the red ball showing the reflection of the ball in the shiny floor. is a clean and simple algorithm, polygon scan conversion uses a variety of tricks of the trade to get the desired results. The other limitation of polygon scan conversion is that it only has a single primitive: the polygon, which means that everything is made up of flat surfaces. This is especially unrealistic when modelling natural objects such as humans or animals, unless you use polygons that are no bigger than a pixel, which is indeed what happens these days. An image generated using a polygon scan conversion algorithm, even one which makes heavy use of texture mapping, will still tend to look computer generated. 1.1.4 Examples Texture mapping is a simple way of making a polygon scan conversion (or a ray tracing) scene look better without introducing lots of polygons. The images in Figure 6 show a scene both with and without any texture maps. Obviously this scene was designed to be viewed with the texture maps turned on. This example shows that texture mapping can make simple geometry look interesting to a human observer. The images in Figure 7 were generated using polygon scan conversion. Texture map- Neil Dodgson 9 Figure 8: An example of environment mapping: a silvered SGI O2 computer reflecting an environment map of the interior of a cafe. ping has been used to make the back and side walls more interesting. All the objects are reflected in the floor. This reflection is achieved by duplicating all of the geometry, upside-down, under the floor, and making the floor partially transparent. The close-up shows the reflection of the red ball, along with a circular "shadow" of the ball. This shadow is, in fact, a polygonal approximation to a circle drawn on the floor polygon and bears no relationship to the lights whatsoever. You may need to look at the version of these images on the Lab's website to see the images more clearly and in colour. Environment mapping (Figure 8) is another clever idea which makes polygon scan conversion images look more realistic. In environment mapping we have a texture map of the environment which can be thought of as wrapping completely around the entire scene (you could think of it as six textures on the six inside faces of a big box). The environment map itself is not drawn, but if any polygon is reflective then the normal to the polygon is found at each pixel (this normal is needed for Gouraud shading anyway) and from this, and a vector pointing to the eye, the appropriate point (and therefore colour) on the environment map can be located. You may note that finding the correct point on the environment map is actually a simple (and easily optimised) piece of ray tracing. 1.1.5 Line drawing An alternative to the above methods is to draw the 3D model as a wire frame outline. This is obviously unrealistic, but is useful in particular applications. The wire frame outline can be either see through or hidden lines can be removed (FvDFH section 15.3 or F&vD section 14.2.6). In general, the lines that are drawn will be the edges of the polygons which would be drawn by a polygon scan conversion algorithm. Line drawing was historically faster than polygon scan conversion. However, modern graphics cards can handle both lines and polygons at about the same speed. Line drawing of 3D models is used in Computer Aided Design (CAD) and in 3D model design. The software which people use to design 3D models tends to use line drawing in its user 10 Advanced Graphics Lecture Notes Figure 9: Screen shots from commercial flight simulators (circa 1995). Figure 10: The real cockpit of a commercial flight simulator: an exact replica of the equivalent airplane's cockpit. interface with polygon scan conversion providing preview images of the model. I find it interesting that, when R&A was first written in 1976, the authors had only line drawing algorithms with which to illustrate their 3D models. Only one figure in the entire book did not use exclusively line drawing: Fig. 6-52, which had screen shots of a prototype polygon scan conversion system. Technology has moved on enormously since then. Neil Dodgson 11
| (a) What bugs exist in the code and how can they be rectified? [10 marks] |
| (b) SystemVerilog synthesis tools use a Boolean optimiser to simplify the implementation logic. |
| (c) Why are don't care terms useful for Boolean optimisation? [3 marks] |
| (d) How could the SystemVerilog be modified to introduce don't care terms for |
| (e)unreachable states above 9? [3 marks] |
| (f) For a modern FPGA with 6-input look-up tables (LUTs), will Boolean. |

Computer Architecture A Quantitative Approach
ISBN: 9780128119051
6th Edition
Authors: John L. Hennessy, David A. Patterson