Details 1. Skill Builder Exercise - Working with PRTK This exercise requires the Mantooth and Washer...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
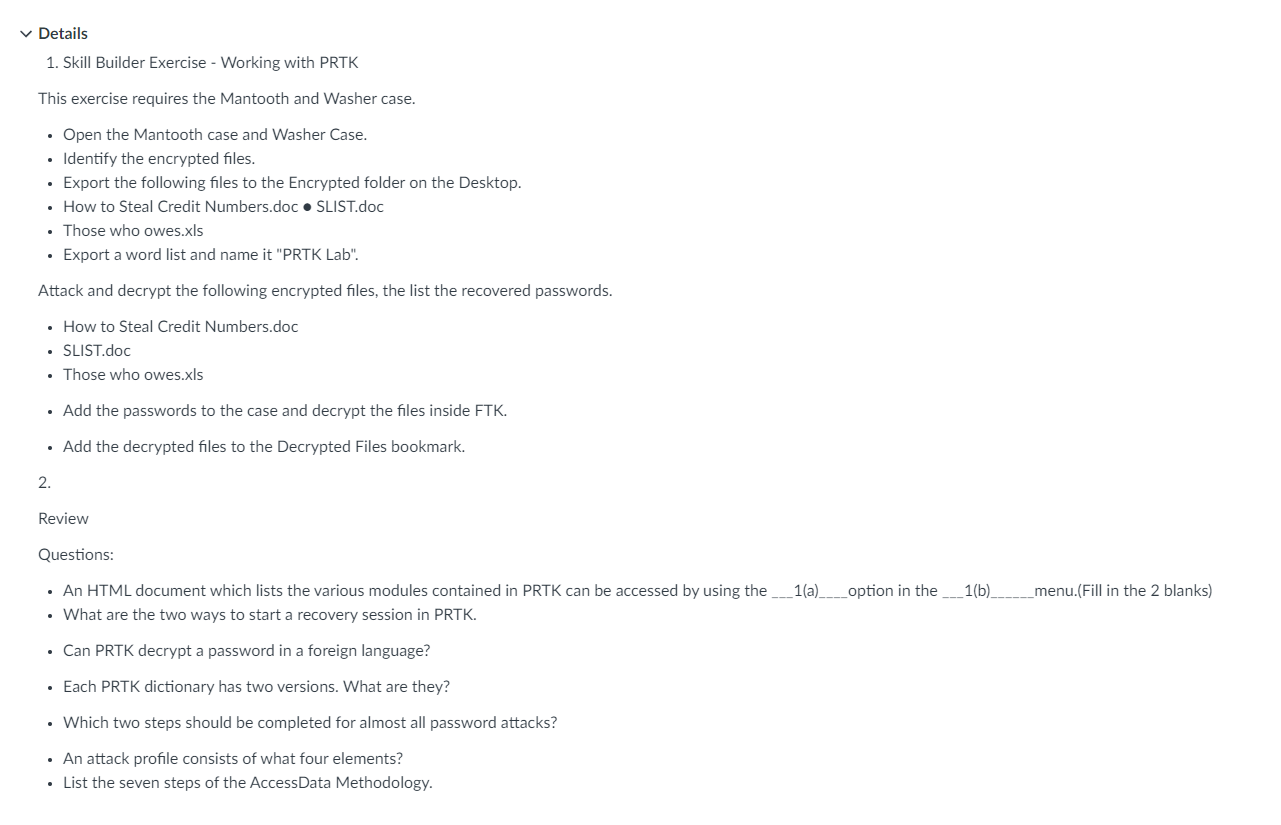
✓ Details 1. Skill Builder Exercise - Working with PRTK This exercise requires the Mantooth and Washer case. • Open the Mantooth case and Washer Case. • Identify the encrypted files. Export the following files to the Encrypted folder on the Desktop. • How to Steal Credit Numbers.doc • SLIST.doc • Those who owes.xls • Export a word list and name it "PRTK Lab". Attack and decrypt the following encrypted files, the list the recovered passwords. • How to Steal Credit Numbers.doc • SLIST.doc • Those who owes.xls • Add the passwords to the case and decrypt the files inside FTK. • Add the decrypted files to the Decrypted Files bookmark. 2. Review Questions: • An HTML document which lists the various modules contained in PRTK can be accessed by using the ____1(a)_______option in the ____1(b)_ • What are the two ways to start a recovery session in PRTK. • Can PRTK decrypt a password in a foreign language? • Each PRTK dictionary has two versions. What are they? • Which two steps should be completed for almost all password attacks? • An attack profile consists of what four elements? • List the seven steps of the AccessData Methodology. __menu.(Fill in the 2 blanks) ✓ Details 1. Skill Builder Exercise - Working with PRTK This exercise requires the Mantooth and Washer case. • Open the Mantooth case and Washer Case. • Identify the encrypted files. Export the following files to the Encrypted folder on the Desktop. • How to Steal Credit Numbers.doc • SLIST.doc • Those who owes.xls • Export a word list and name it "PRTK Lab". Attack and decrypt the following encrypted files, the list the recovered passwords. • How to Steal Credit Numbers.doc • SLIST.doc • Those who owes.xls • Add the passwords to the case and decrypt the files inside FTK. • Add the decrypted files to the Decrypted Files bookmark. 2. Review Questions: • An HTML document which lists the various modules contained in PRTK can be accessed by using the ____1(a)_______option in the ____1(b)_ • What are the two ways to start a recovery session in PRTK. • Can PRTK decrypt a password in a foreign language? • Each PRTK dictionary has two versions. What are they? • Which two steps should be completed for almost all password attacks? • An attack profile consists of what four elements? • List the seven steps of the AccessData Methodology. __menu.(Fill in the 2 blanks)
Expert Answer:
Answer rating: 100% (QA)
I can see that youve provided a set of tasks and questions related to using PRTK Password Recovery T... View the full answer

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these programming questions
-
Illustrate step-by-step the stack algorithm to convert this to postfix. a+b* (d *e+f)
-
Case Study: Quick Fix Dental Practice Technology requirements Application must be built using Visual Studio 2019 or Visual Studio 2017, professional or enterprise. The community edition is not...
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
According to data released by the World Bank, the mean PM10 (particulate matter) concentration for the city of Kabul, Afghanistan, in 1999 was 46. Suppose that because of efforts to improve air...
-
For a thin wing moving parallel to its chord line, transition to a turbulent boundary layer occurs at a local Reynolds number Rex, where x is the distance from the leading edge of the wing. The...
-
British Quince comes across an average-risk investment project that offers a rate of return of 9.5%. This is less than the company's normal rate of return, but one of Quince's directors notes that...
-
What is the function of clutch in automabile vehicle ? Which type of clutch is used in two - wheelers and why ?
-
Steam produced in a boiler is frequently wetthat is. it is a mist composed of saturated water vapor and entrained liquid droplets. The quality of a wet steam is defined as the fraction of the mixture...
-
How much work ( in joules) is done in lifting a 45.57 newton box from the floor to a table that is 0.73 meters above the floor? Round your final answer to two decimal places. A ball is thrown...
-
Angela Petrillo recendy opened her own law office, which she operates as a corporation. The name of the new entity is Angela Petrillo, Attorney. Petrillo experienced the following events during the...
-
Should a job redesign be undertaken if it will improve efficiency even if the employees do not want it?Should a job redesign be undertaken if it will improve efficiency even if the employees do not...
-
Calculate the tension in the cable connecting the two masses. Assume all surfaces are frictionless. (8 marks) 5.0 kg 6.0 kg 60 70
-
Each of the following statements violates at least one of the criteria for effective supporting materials discussed in this chapter. Identify the flaw (or flaws) in each statement. According to a...
-
Define five different types of conflict. Offer examples. Engage with and cite readings and other media
-
Explain why you would use sampling techniques in picking a portfolio. Explain your rationale if you would not use sampling techniques. Defend the approach you would prefer if you had to use sampling...
-
Define the concept "pay yourself first". With this in mind, what is your advice to someone on paying off credit card debt and investing for their retirement? Do you feel as though they should pay off...
-
Use Stokes' Theorem to evaluate ff curl F. dS, where F(x, y, z) = (arctan(z2yz), ry, z2) and S is the cone x = /y + 2 from 0x2 oriented in the direction of the positive x-aris.
-
Use the T account for Cash below to record the portion of each of the following transactions, if any that affect cash. How do these transactions affect the companys liquidity? Jan. 2 Provided...
-
Sherry Hopson owns a retail family clothing store. Her store is located at 4321 Circle Drive, Houston, TX 77001. Her employer identification number is 95- 1234321 and her Social Security number is...
-
The following additional information is available for the Dr. Ivan and Irene Incisor family. Ivan and Irene have the following investment income, in addition to that reported in Chapter 1: Dividends...
-
On September 14, 2012, Jay purchased a passenger automobile that is used 75 percent in his accounting business. The automobile has a basis for depreciation purposes of $35,000, and Jay uses the...
-
Carry out an Internet search to find more examples of project success and failure. From your search, are there any common themes in each? What are the implications of success and failure in each case?
-
How successful are government contracting arrangements? How do these compare, for instance, with the arrangements BAA had with their suppliers in the construction of T5 at Heathrow (Project...
-
What is the role of brainstorming and how might it be used to greatest effect?

Study smarter with the SolutionInn App


