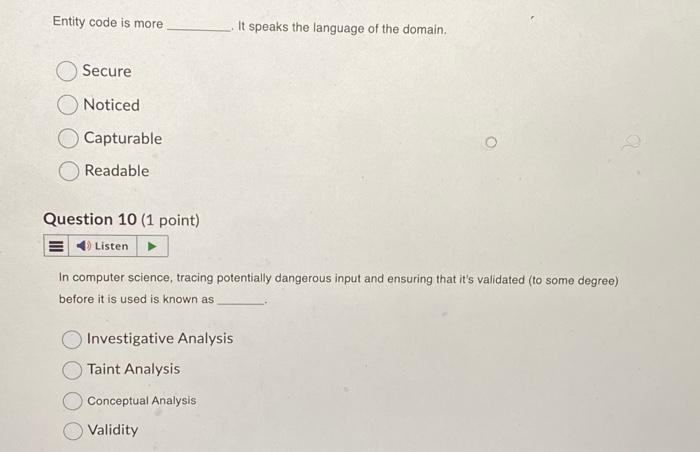
Entity code is more Secure Noticed Capturable Readable Question 10 (1 point) E Listen In computer...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Entity code is more Secure Noticed Capturable Readable Question 10 (1 point) E Listen In computer science, tracing potentially dangerous input and ensuring that it's validated (to some degree) before it is used is known as Investigative Analysis Taint Analysis It speaks the language of the domain. Conceptual Analysis Validity Entity code is more Secure Noticed Capturable Readable Question 10 (1 point) E Listen In computer science, tracing potentially dangerous input and ensuring that it's validated (to some degree) before it is used is known as Investigative Analysis Taint Analysis It speaks the language of the domain. Conceptual Analysis Validity
Expert Answer:
Answer rating: 100% (QA)
The detailed answer for the above question is provided below Entity code is moreIt speak... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these programming questions
-
Are virtual and travel medical care facilities ( cruise ships, hotels, etc. ) beneficial or harmful to the overall state of medical tourism? What can the United States do to compete for global...
-
Case Study: Quick Fix Dental Practice Technology requirements Application must be built using Visual Studio 2019 or Visual Studio 2017, professional or enterprise. The community edition is not...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
In order to evaluate lim f(a+h)-f(), it is necessary to evaluate f(a + h). h xa For f(x) = x 3, f(a+h) =
-
Calculate the frequency of the J = 3 f-- 2 transition in the pure rotational spectrum of 12CI60. The equilibrium bond length is 112.81 pm.
-
For the common-base configuration of Fig. 5.18, an ac signal of 10 mV is applied, resulting in an ac emitter current of 0.5 mA. If α = 0.980, determine: a. Zi b. Vo if RL = 1.2...
-
On a distant planet small-amplitude waves travel across a \(1-\mathrm{m}\)-deep pond with a speed of \(5 \mathrm{~m} / \mathrm{s}\). Determine the acceleration of gravity on the surface of that...
-
Hamilton Hawks Players' Association and Mr. Sideline, the CEO and majority owner of Hamilton Hawks Soccer, Inc, ask your help in resolving a salary dispute. Mr. Sideline presents the following income...
-
Two balls, one with a mass of 2 kg and the other with a mass of 3 kg, collide elastically. After the collision, the 2-kg ball moves to the left with a velocity of 4 m/s and the 3-kg ball moves to the...
-
Ethan is the leader of a team with N members. He has assigned an error score to each member in his team based on the bugs that he has found in that particular team member's task. Because the error...
-
Design a transmitting earth station to provide a clear air C/N of 26 dB in a C- band transponder at a frequency of 6.285 GHz. Given an FM band of 27MHz. Use an uplink antenna with a diameter of 9 m...
-
Use the future value formula to find the indicated value. FV = $5227; n = 11; i = 0.06; PMT = ? PMT = $ (Round to the nearest cent.)
-
Corp's total assets at the end of last year were $460,000 and its EBIT was $45,000. What was its basic earning power (BEP) ratio?
-
Solve the following system of equations by the substitution method. Check the solution(s). y = 3x+2 5x+2y=9
-
4. University of Notre Dame is a premier institution that draws students from all over the world to its campus. Although it is privately funded, it aspires to world-class quality and reputation,...
-
(a) A velocity selector consists of electric and magnetic fields described by the expressions = E k and B = B , with B = 14.0 mT. Find the value of E (in kV/m) such that a 830 eV electron moving in...
-
Recombination rates between three loci in corn are shown here, R and W2 R and L2 W2 and L2 What is the order of the genes on the chromosome? 17% 35% 18%
-
Cable Corporation is 60% owned by Anna and 40% owned by Jim, who are unrelated. It has noncash assets, which it sells to an unrelated purchaser for $100,000 in cash and $900,000 in installment...
-
I. Analyze the two most common methods of encrypting plaintext: bit stream and block cipher. II. Review that in the bit stream method, each bit in the plaintext is transformed into a cipher bit one...
-
Explain that the latest type of attack in this category is known as ransomware, which is a malware attack on the host system that denies access to the user and then offers to provide a key to allow...
-
Detail the purpose of cyberterrorism and what the United States and other government bodies are doing to combat this. Differentiate between the three examples provided in the text with respect to...
-
Refer to the Alexia Corporation data in Short Exercise 13-17. Assume the market price of Alexia Corporations common stock is \($16.00\) per share. Compute Alexia Corporations price/earnings ratio....
-
The details in Figure 16.9 relate to D Co. Using that information and appropriate ratios, prepare a financial report on the company. The opening inventory value figures were :135,000 20X1 actual and...
-
A loan is made to a company of $20,000, which is equal to :10,000 at the date of the loan during year 1. The loan is legally denominated in dollars. At the end of year 1, the loan is translated as...

Study smarter with the SolutionInn App


