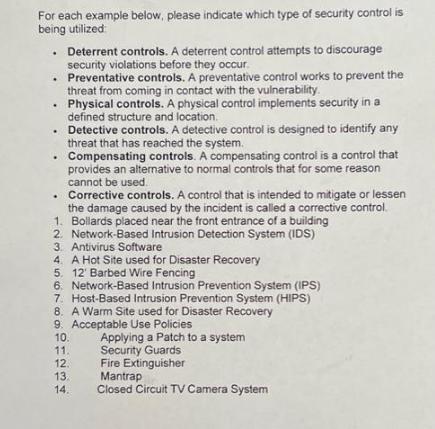
For each example below, please indicate which type of security control is being utilized: Deterrent controls....
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
For each example below, please indicate which type of security control is being utilized: Deterrent controls. A deterrent control attempts to discourage security violations before they occur. . Preventative controls. A preventative control works to prevent the threat from coming in contact with the vulnerability. Physical controls. A physical control implements security in a defined structure and location. Detective controls. A detective control is designed to identify any threat that has reached the system. . Compensating controls. A compensating control is a control that provides an alternative to normal controls that for some reason cannot be used. Corrective controls. A control that is intended to mitigate or lessen the damage caused by the incident is called a corrective control. 1. Bollards placed near the front entrance of a building 2. Network-Based Intrusion Detection System (IDS) 3. Antivirus Software 4. A Hot Site used for Disaster Recovery 5. 12' Barbed Wire Fencing 6. Network-Based Intrusion Prevention System (IPS) 7. Host-Based Intrusion Prevention System (HIPS) 8. A Warm Site used for Disaster Recovery 9. Acceptable Use Policies 10. 11. 12. 13. 14. Applying a Patch to a system Security Guards Fire Extinguisher Mantrap Closed Circuit TV Camera System For each example below, please indicate which type of security control is being utilized: Deterrent controls. A deterrent control attempts to discourage security violations before they occur. . Preventative controls. A preventative control works to prevent the threat from coming in contact with the vulnerability. Physical controls. A physical control implements security in a defined structure and location. Detective controls. A detective control is designed to identify any threat that has reached the system. . Compensating controls. A compensating control is a control that provides an alternative to normal controls that for some reason cannot be used. Corrective controls. A control that is intended to mitigate or lessen the damage caused by the incident is called a corrective control. 1. Bollards placed near the front entrance of a building 2. Network-Based Intrusion Detection System (IDS) 3. Antivirus Software 4. A Hot Site used for Disaster Recovery 5. 12' Barbed Wire Fencing 6. Network-Based Intrusion Prevention System (IPS) 7. Host-Based Intrusion Prevention System (HIPS) 8. A Warm Site used for Disaster Recovery 9. Acceptable Use Policies 10. 11. 12. 13. 14. Applying a Patch to a system Security Guards Fire Extinguisher Mantrap Closed Circuit TV Camera System
Expert Answer:
Answer rating: 100% (QA)
Bollards placed near the front entrance of a building Physical contr... View the full answer

Related Book For 

Financial Accounting Tools for Business Decision Making
ISBN: 978-1119368458
7th Canadian edition
Authors: Paul D. Kimmel, Jerry J. Weygandt, Donald E. Kieso, Barbara Trenholm, Wayne Irvine
Posted Date:
Students also viewed these computer network questions
-
As a DBA, Amy's data role in her organization includes technical implementations of the data policies and standards, as well as managing the data structures that the data is stored in. What data role...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
A ball is dropped from a high rise platform at t = 0 starting from rest. After 6 seconds another ball is thrown downwards from the same platform with a speed v. The two balls meet at t = 18s. What is...
-
A 4.00-kg particle moves along the x axis. Its position varies with time according to x = t + 2.0t3, where x is in meters and t is in seconds. Find (a) The kinetic energy at any time t, (b) The...
-
Your roommate is about to submit a scope statement for a spring concert sponsored by the entertainment council at Western Evergreen State University (WESU). WESU is a residential university with over...
-
Using the carpet plots of Figure 7.58, select the percentages of \(0^{\circ}, \pm 45^{\circ}\), and \(90^{\circ}\) plies that are needed in a \(\left[0_{i} / \pm 45_{i} / 90_{k} ight]\) laminate if...
-
The Walston Company is to be liquidated and has the following liabilities: Income taxes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . $ 8,000 Notes payable...
-
Why is structure and hierarchy so important in understanding and managing organizational conflict? With that in mind, how do you best handle a conflict between yourself and your immediate supervisor?
-
Patriot Co. manufactures flags in two sizes, small and large. The company has total fixed costs of $240,000 per year. Additional data follow. The company is considering buying new equipment that...
-
Find the first four nonzero terms in a power series expansion about x= 0 for a general solution to the given differential equation. (x2 + 18) y" +y = 0 y(x) =D+. %3D (Type an expression in terms of...
-
Calculate the amount of the estimated accounts receivable that the Company would report in its budgeted balance sheet at November 30, 2023. Accounts Receivable @ November 30, 2023 (4 points)
-
Spalding Company has offered to sell to Ping Company its assets at their book values plus $1,800,000 representing payment for goodwill. Operating data for 2023 for the two companies are as follows:...
-
South Dakota v. Wayfair, Inc., 138 S. Ct. 2080 (2018)\ FACT SUMMARY South Dakota, like many states, taxes the retail sales of goods and services in the state. Sellers are required to collect and...
-
If A is the matrix associated to the system (S), so that the system can be written in the form -( Ak X Y Z -k h+k 2h + 1 the linear transformation lk: R IR associated to Ag with respect to the...
-
7) A blob of clay of mass M is propelled upward from a spring that is initially compressed by an amount d. The spring constant is k. What is the ultimate height h above the unstretched spring's end...
-
To modify a checklist task you should - O a. choose the edit menu, click checklists and then choose edit b. open the checklist, click the task and then click the modify button c. select the...
-
What is EBIT/eps analysis? What information does it provide managers?
-
The general ledger of Corso Care Corp., a veterinary company, showed these balances on August 31, 2018: Cash $4,500; Accounts Receivable $1,800; Supplies $350; Equipment $6,500; Accounts Payable...
-
At the beginning of the current golf season, on April 1, 2018, the general ledger of In the Pines Golf Shop showed Cash $4,200; Inventory $19,500; Common Shares $12,000; and Retained Earnings...
-
The year ended June 30, 2019, has been another successful year for ABC. The success, however, has meant that Doug, Bev, Emily, and Daniel have spent many long hours in the business accommodating...
-
This exercise considers data from the Medical Expenditure Panel Survey (MEPS) described in Exercise 1.1 and Section 11.4. Our dependent variable consists of the number of outpatient (COUNTOP) visits....
-
This exercise considers the data described in the Section 13.2.2 ratemaking classification example using data in Table 13.3 Table 13.3 . a. Fit a gamma regression model using a log-link function with...
-
Verify that the Tweedie distribution is a member of the linear exponential family of distributions by checking equation (13.9). In particular, provide an expression for \(S(y, \phi)\) (note that...

Study smarter with the SolutionInn App