From any host in your network, map the path that packets take as they travel to...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
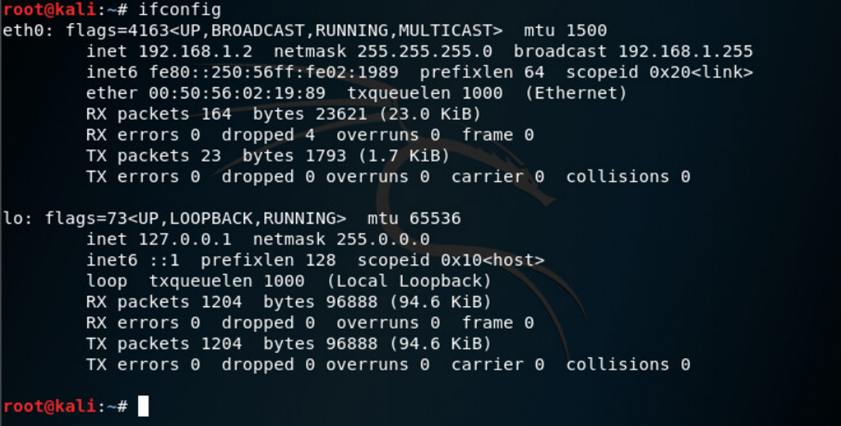
From any host in your network, map the path that packets take as they travel to a host destination (example google.com or local host in our environment). Provide a screenshot below of the command being used and its results. root@kali:~# ifconfig etho: flags=4163 mtu 1500 inet 192.168.1.2 netmask 255.255.255.0 broadcast 192.168.1.255 inet6 fe80::250:56ff:fe02:1989 prefixlen 64 scopeid 0x20 ether 00:50:56:02:19:89 txqueuelen 1000 (Ethernet) RX packets 164 bytes 23621 (23.0 KiB) RX errors0 dropped 4 overruns 0 frame 0 TX packets 23 bytes 1793 (1.7 KiB) TX errors dropped 0 overruns 0 carrier 0 collisions 0 lo: flags=73 mtu 65536 inet 127.0.0.1 netmask 255.0.0.0 inet6 ::1 prefixlen 128 scopeid 0x10 loop txqueuelen 1000 (Local Loopback) RX packets 1204 bytes 96888 (94.6 KiB) RX errors 0 dropped 0 overruns 0 frame o TX packets 1204 bytes 96888 (94.6 KiB) TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0 root@kali:~# From any host in your network, map the path that packets take as they travel to a host destination (example google.com or local host in our environment). Provide a screenshot below of the command being used and its results. root@kali:~# ifconfig etho: flags=4163 mtu 1500 inet 192.168.1.2 netmask 255.255.255.0 broadcast 192.168.1.255 inet6 fe80::250:56ff:fe02:1989 prefixlen 64 scopeid 0x20 ether 00:50:56:02:19:89 txqueuelen 1000 (Ethernet) RX packets 164 bytes 23621 (23.0 KiB) RX errors0 dropped 4 overruns 0 frame 0 TX packets 23 bytes 1793 (1.7 KiB) TX errors dropped 0 overruns 0 carrier 0 collisions 0 lo: flags=73 mtu 65536 inet 127.0.0.1 netmask 255.0.0.0 inet6 ::1 prefixlen 128 scopeid 0x10 loop txqueuelen 1000 (Local Loopback) RX packets 1204 bytes 96888 (94.6 KiB) RX errors 0 dropped 0 overruns 0 frame o TX packets 1204 bytes 96888 (94.6 KiB) TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0 root@kali:~#
Expert Answer:

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these computer network questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
How does routing work? Routers refer to internal routing tables to make decisions about how to route packets along network paths. A routing table records the paths that packets should take to reach...
-
A quality improvement program has been instituted in an organization to reduce total quality costs. Discuss the impact of such a program on prevention, appraisal, and failure costs.
-
Write a paper on what you have learned up to this point and your view of marketing as a result of studying the topic up until this point in the semester.
-
(LO3) If a business has an average of \(\( \$ \) 29\) million or less of gross receipts over the last 3 years, may the business use the cash method of accounting?
-
Journal entries for buyer and seller perpetual inventory system The following are selected transactions of Watsonia Stores: Required (a) Assuming that neither business is registered for GST, record...
-
After graduating from dental school two years ago, Dr. Lauren Farish purchased the dental practice of a long-time dentist who was retiring. In January of this year she had to replace the outdated...
-
In a pest-eradication program, sterilized male flies are released into the general population each day. Ninety percent of those flies will survive a given day. How many flies should be released each...
-
Determine the (i) gain crossover frequency w,, (ii) phase margin om (iii) phase crossover fre- quency Wp. and (iv) gain margin K, of the following open loop transfer functions L(jw) and L(jw) using...
-
AHP Company generated $200 million sales last year, incurred $110 million in cost of goods sold and incurred $50 million in SG&A expenses including depreciation expense of $15 million. During the...
-
It is a criminal offence to issue a dud cheque in Ghana. 1. On the basis of your knowledge in finance and banking, describe briefly the main reason for the criminalisation of the act of issuing dud...
-
At the beginning of July, Fick 3D Corporation has a balance in inventory of $2,950 of 3D printing accessories. The following transactions occur during the month of July. July 3 July 4 July 9 Purchase...
-
The future cash flows of two mutually exclusive capital projects follow: Project A: Uneven Flow Year0123 Cash Flow(-$12,000)$6,500$10,500$6,000 Project B: Annuity Flow Year0123456**Annuity** Cash...
-
Greta died on September 1 0 , 2 0 2 2 . She has never carried on a business. By what date must her final income tax return be filed? Question 5 options: April 3 0 , 2 0 2 3 . April 3 0 , 2 0 2 4 ....
-
QUESTION 1 Organizations are facing with a variety of pressures to change, from many directions. Discuss FIVE (5) external pressures for organizational change together with examples. QUESTION 2...
-
In what ways does a well-designed enterprise search software vary from popular search engines (e.g., Bing, DuckDuckGo, and Google)?
-
In the Ethernet standard, a sender pauses 96 bit times between sending consecutive frames. This pausing time is referred to as inter-frame gap, and it is used to allow a receiving device to complete...
-
Explain why a minimum frame size is required for Ethernet. For example, I OBase Ethernet imposes a minimum frame size constraint of 64 bytes. (If you have done the previous problem, you might have...
-
Consider a network in which all nodes are connected to three other nodes. In a single time step, a node can receive all transmitted broadcast packets from its neighbors, duplicate the packets, and...
-
Consider a particle in a Newtonian potential \(V(r)=-k / r+\epsilon / r^{n}\) for some integer \(n\). Using the alternate variable \(u=1 / r\), (a) show that the radial equation of motion can be put...
-
Consider the equation of motion \[\frac{d^{2} u}{d \varphi^{2}}+u-\frac{1}{p}=3 \lambda u^{2}\] where \(p\) and \(\lambda\) are constants. Find the solution using perturbation theory to first order...
-
Using numerical methods, solve the differential equation \[\frac{d q}{d t}=-\alpha q+\beta\] Compare your results with the exact solution as a function of the discrete time-step you use, and the...

Study smarter with the SolutionInn App


