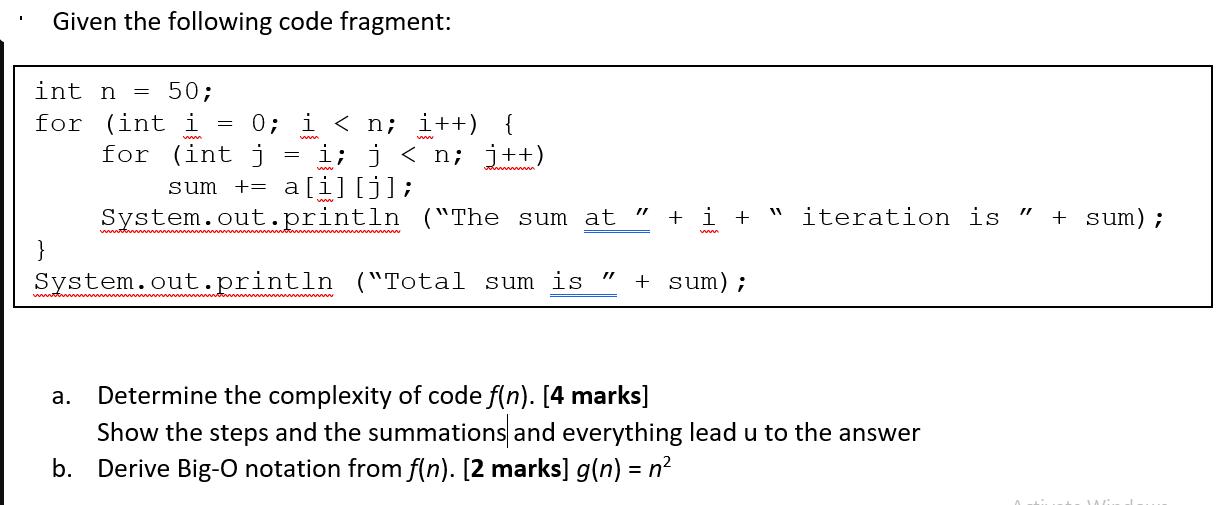
Given the following code fragment: int n = 50; for (int i ww 0; i...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Given the following code fragment: int n = 50; for (int i ww 0; i<n; i++) { i; j<n; j++) for (int j sum += a[i][j]; System.out.println = ("The sum at 11 // + i+ iteration is " + sum); ww System.out.println ("Total sum is + sum); 11 a. Determine the complexity of code f(n). [4 marks] Show the steps and the summations and everything lead u to the answer b. Derive Big-O notation from f(n). [2 marks] g(n) = n² Given the following code fragment: int n = 50; for (int i ww 0; i<n; i++) { i; j<n; j++) for (int j sum += a[i][j]; System.out.println = ("The sum at 11 // + i+ iteration is " + sum); ww System.out.println ("Total sum is + sum); 11 a. Determine the complexity of code f(n). [4 marks] Show the steps and the summations and everything lead u to the answer b. Derive Big-O notation from f(n). [2 marks] g(n) = n²
Expert Answer:
Answer rating: 100% (QA)
The image includes a Java code snippet with a nested forloop which youve asked to analyze in terms o... View the full answer

Related Book For 

Introduction to Algorithms
ISBN: 978-0262033848
3rd edition
Authors: Thomas H. Cormen, Charles E. Leiserson, Ronald L. Rivest
Posted Date:
Students also viewed these programming questions
-
Use linear approximation, i.e. the tangent line, to approximate 64.1 as follows: Let f(x)=x. The equation of the tangent line to f(x) at x = 64 can be written in the form y = mx + b where m is: and...
-
Assume that the differential equation dy(t) dt -2y(t) is solved via the midpoint method (see above). Determine the bound on the dis- cretization step h so that the numerical solution remains stable.
-
The following code fragment implements Horner?s rule for evaluating a polynomial The following code fragment implements Horner?s rule for evaluating a polynomial given the coefficients a 0, a 1 ??.,a...
-
Division A of ABC, Inc. produces part TZ20 that is used by Division B in the manufacture of product 100BD.Below is a summary of the manufacturing costs of the TZ20 part: Direct Labour $8.00 per unit...
-
A warehouse contains 500 machines. Each machine is either new or used, and each machine has either good quality or bad quality. There are 120 new machines that have bad quality. There are 230 used...
-
Consider the information presented in E13-10. Required: 1. How would Sprint report the debt in its balance sheet if it reported under IFRS? Why? 2. Would your answer to requirement 1 change if Sprint...
-
A forensic account determines the following facts about a company: Cash and equivalents. \(\$ 76,000\) Receivables 218,000 Current assets. 420,000 Current liabilities 240,000 Average inventory...
-
Gestalt. Inc. uses a kanban system in its automobile production facility in Germany. This facility operates 8 hours per day to produce the Jitterbug, a replacement for the obsolete but immensely...
-
intercultural communication is the subject and the topic i have choosen is discrimination. Sunday, Apr 10, 2022 at 11:59 pm Over the course of the term, you will be asked to write five reflective...
-
WorldCom revealed that in addition to the US$3.8bn in expenses improperly recorded as capital, an internal audit discovered that US$3.3bn in profits were improperly recorded on its books from 1999 to...
-
Consider the modification of the STS KAS that is presented as Protocol 3. In this modification of the protocol, the signatures omit the intended receiver. Show how this renders the protocol insecure,...
-
What are some of the limitations of using test data?
-
Program controls in a computer processing system are used as substitutes for human controls in a manual system. Which of the following is an example of a program control? a. Dual read. b. Echo check....
-
What are computer-assisted audit programs?
-
Which of the following would most likely be a weakness in internal control of a client that utilizes microcomputers rather than a larger computer system a. Employee collusion possibilities are...
-
Which of the following employees normally would be assigned the operating responsibility for designing a computer processing installation, including flowcharts of data processing routines? a....
-
Environmentally conscious Susan has been told that a new electric car will only generate 5 ounces of greenhouse gases (GHG) per mile, but that a standard internal combustion car is double that at 10...
-
I frequently use NY Times and CNN and am aware of Fox News but I never use it. I visit these sites, NY Times and CNN, a few times a week whenever I have to research something or see something on...
-
This problem explores the space requirements for van Emde Boas trees and suggests a way to modify the data structure to make its space requirement depend on the number n of elements actually stored...
-
Write an O(n)-time non recursive procedure that, given an n-node binary tree, prints out the key of each node in the tree. Use a stack as an auxiliary data structure.
-
An n-input, m-output boolean function is a function from {TRUE, FALSE} n to {TRUE, FALSE} m . How many n-input, 1-output boolean functions are there? How many n-input, m-output boolean functions are...
-
Use the information from question 5. After delivery, at what amount is the merchandise carried on the U.S. companys books? Use the following forward and spot prices for Canadian dollars (C\($)\) to...
-
A U.S. company expects to buy merchandise from a Canadian supplier for approximately C\($1,000,000\), in the middle of April. On November 15, 2016, the company enters a forward contract locking in...
-
On March 1, 2017, a U.S. company enters a forward contract locking in the selling price of C\($1\) ,000,000, for delivery on April 15, 2017. The contract does not qualify for hedge accounting. What...

Study smarter with the SolutionInn App