Use the following information. Assumptions Data type int is 32 bits long. Right shifts of...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
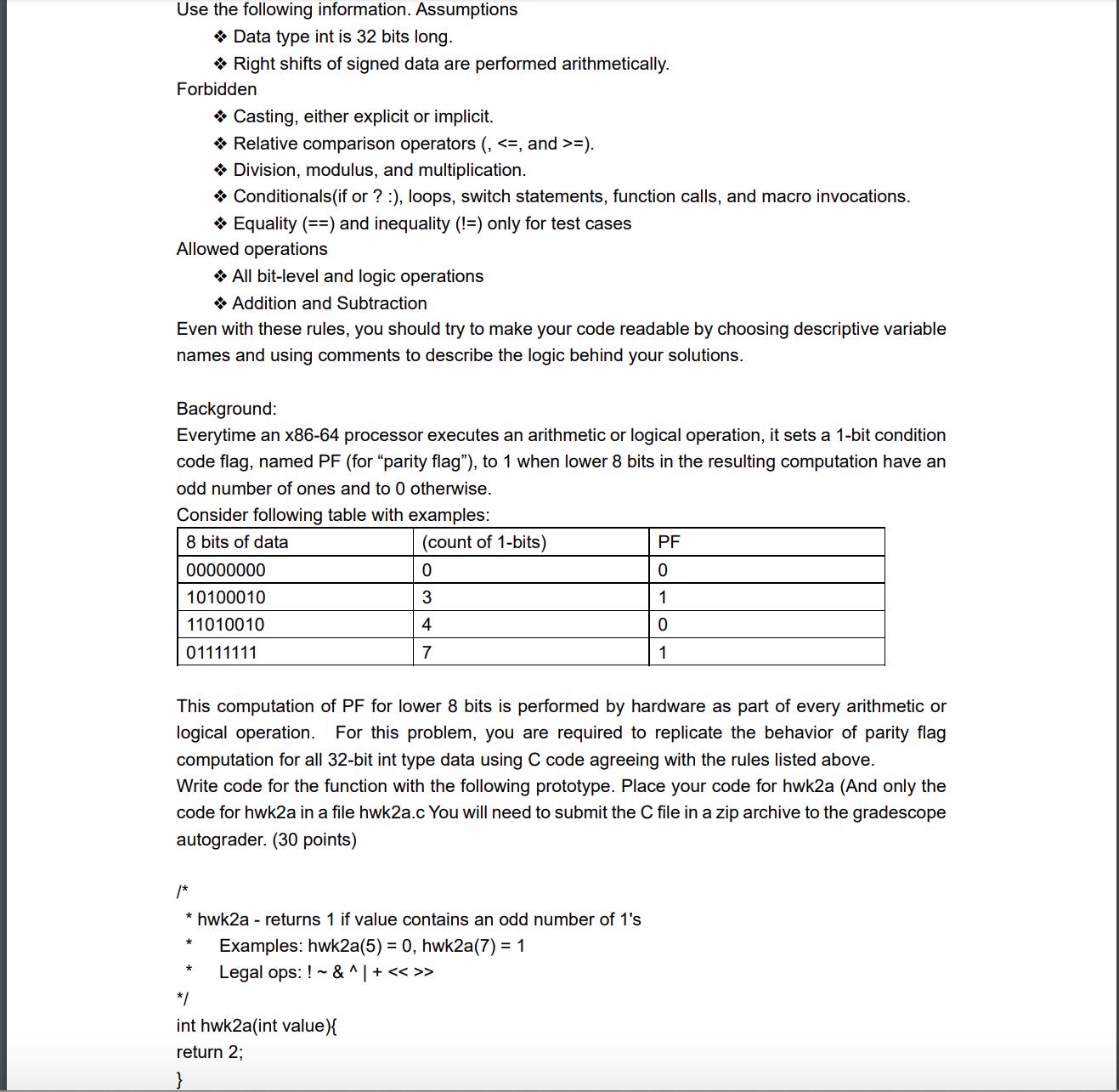
Use the following information. Assumptions → Data type int is 32 bits long. Right shifts of signed data are performed arithmetically. Forbidden Casting, either explicit or implicit. ✰ Relative comparison operators (, <=, and >=). ◆ Division, modulus, and multiplication. → Conditionals (if or ? :), loops, switch statements, function calls, and macro invocations. → Equality (==) and inequality (!=) only for test cases Allowed operations Even with these rules, you should try to make your code readable by choosing descriptive variable names and using comments to describe the logic behind your solutions. All bit-level and logic operations Addition and Subtraction Background: Everytime an x86-64 processor executes an arithmetic or logical operation, it sets a 1-bit condition code flag, named PF (for "parity flag"), to 1 when lower 8 bits in the resulting computation have an odd number of ones and to 0 otherwise. Consider following table with examples: 8 bits of data 00000000 10100010 11010010 01111111 * * (count of 1-bits) This computation of PF for lower 8 bits is performed by hardware as part of every arithmetic or logical operation. For this problem, you are required to replicate the behavior of parity flag computation for all 32-bit int type data using C code agreeing with the rules listed above. Write code for the function with the following prototype. Place your code for hwk2a (And only the code for hwk2a in a file hwk2a.c You will need to submit the C file in a zip archive to the gradescope autograder. (30 points) /* * hwk2a - returns 1 if value contains an odd number of 1's Examples: hwk2a(5) = 0, hwk2a(7) = 1 Legal ops: ! & ^ | + << >> 0 3 4 7 */ int hwk2a(int value){ return 2; PF 0 1 0 1 Use the following information. Assumptions → Data type int is 32 bits long. Right shifts of signed data are performed arithmetically. Forbidden Casting, either explicit or implicit. ✰ Relative comparison operators (, <=, and >=). ◆ Division, modulus, and multiplication. → Conditionals (if or ? :), loops, switch statements, function calls, and macro invocations. → Equality (==) and inequality (!=) only for test cases Allowed operations Even with these rules, you should try to make your code readable by choosing descriptive variable names and using comments to describe the logic behind your solutions. All bit-level and logic operations Addition and Subtraction Background: Everytime an x86-64 processor executes an arithmetic or logical operation, it sets a 1-bit condition code flag, named PF (for "parity flag"), to 1 when lower 8 bits in the resulting computation have an odd number of ones and to 0 otherwise. Consider following table with examples: 8 bits of data 00000000 10100010 11010010 01111111 * * (count of 1-bits) This computation of PF for lower 8 bits is performed by hardware as part of every arithmetic or logical operation. For this problem, you are required to replicate the behavior of parity flag computation for all 32-bit int type data using C code agreeing with the rules listed above. Write code for the function with the following prototype. Place your code for hwk2a (And only the code for hwk2a in a file hwk2a.c You will need to submit the C file in a zip archive to the gradescope autograder. (30 points) /* * hwk2a - returns 1 if value contains an odd number of 1's Examples: hwk2a(5) = 0, hwk2a(7) = 1 Legal ops: ! & ^ | + << >> 0 3 4 7 */ int hwk2a(int value){ return 2; PF 0 1 0 1
Expert Answer:
Answer rating: 100% (QA)
Answer write a C function hwk2a that determines whether a 32bit integer has an odd number of set bit... View the full answer

Posted Date:
Students also viewed these operating system questions
-
Write a research paper on the following topic: Security Threat Groups/Gangs in Prison, Research the following Security Threat Groups/Gangs: The Aryan Brotherhood, Black Guerilla Family, the Folk...
-
Write a research paper on Standard Oil Co. Inc. Analyze the rationale for the so called "Trust-busting" Standard Oil apart. Examine the main advantages and disadvantages of "Trust-busting". Write...
-
Write a research paper on how family fund their children's tuition
-
Factor each polynomial. 125k - 64k 4
-
The following data are cost (in cents) per ounce for nine different brands of sliced Swiss cheese (www.consumerreports.org): a. Compute the variance and standard deviation for this data set. s2 5...
-
Second Chance Welding rebuilds spot welders for manufacturers. The following budgeted cost data for 2014 is available for Second Chance. The company desires a $30 profit margin per hour of labor and...
-
What is a cash discount? What are the benefits to the seller of allowing cash discounts? Distinguish between a cash discount and a trade discount.
-
In its income statement for the year ended December 31, 2014, Michael Company reported the following condensed data. Instructions (a) Prepare a multiple-step income statement. (b) Prepare a...
-
Question two (20mks) Building Societies Act is a well structured and balanced Organism that spells out different functions. Identify and describe the organization and management of building society...
-
The Kreeger Grocery Store chain has bought out a competing grocery store chain. However, it now has too many stores in close proximity to each other in certain cities. In Roanoke the chain has 10...
-
When would the last truck unload and how long would it have waited? This question is from the National Cranberry Cooperative, see link attached for article details....
-
Which one of the following items is not required to be included in a companys periodic 8-K report filed with the SEC when significant events occur? a. Acquisition or disposition of a significant...
-
Form 8-K must generally be submitted to the SEC within four days after the occurrence of a significant event. Which one of the following is not an event that would be reported by Form 8-K? a. The...
-
Within four days after the occurrence of any event that is of material importance to the stockholders, a company must file a Form 8-K information report with the SEC to disclose the event. An example...
-
Shareholders may ask or allow others to enter their vote at a shareholders meeting that they are unable to attend. The document furnished to shareholders to provide background information for their...
-
Which of the following factors by itself requires a corporation to comply with the reporting requirements of the Securities Exchange Act of 1934? a. 600 employees. b. Shares listed on a national...
-
GE's beginning and ending LIFO inventories were: 10,427 and 9,203 , respectively . GE had a pre-tax liquidation gain of 507. Note that inventory increased despite the liquidation, because GE uses...
-
Sue Deliveau opened a software consulting firm that immediately paid $2,000 for a computer. Was this event a transaction for the business?
-
Shiloh supplies equipment to the automotive and commercial vehicle markets and other industrial customers. It specializes in materials and designs that reduce vehicle weight and increase fuel...
-
Plaintiffs purchased stock warrants (rights to purchase) for blocks of Osborne Computer Corp., the manufacturer of the first mass-market portable personal computer. Because of inability to produce a...
-
Kronenberger Burgoyne, LLP, was a law firm with two equity partners who agreed to equal ownership as of 2009. Before 2009, Kronenberger had owned a majority interest in the firm, and when, in 2011,...

Study smarter with the SolutionInn App

