In the hybrid cryptosystem, which of the following is true? Key exchange and digital signatures are...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
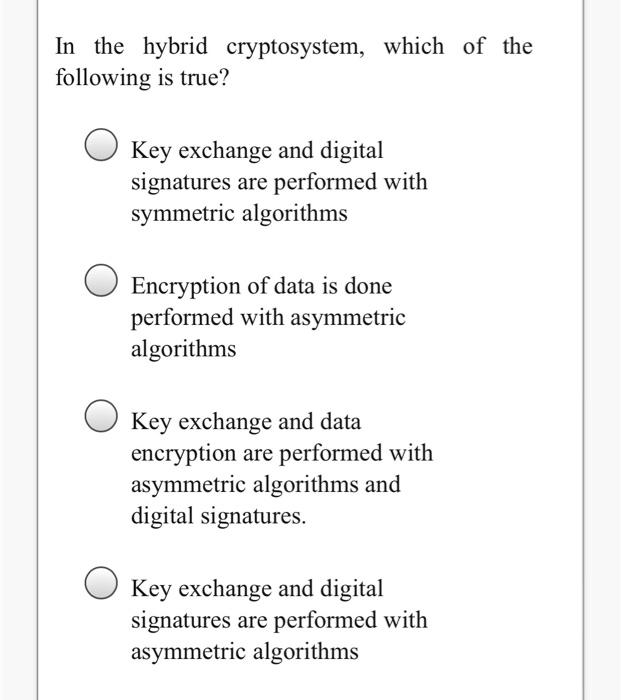
In the hybrid cryptosystem, which of the following is true? Key exchange and digital signatures are performed with symmetric algorithms Encryption of data is done performed with asymmetric algorithms Key exchange and data encryption are performed with asymmetric algorithms and digital signatures. Key exchange and digital signatures are performed with asymmetric algorithms In the hybrid cryptosystem, which of the following is true? Key exchange and digital signatures are performed with symmetric algorithms Encryption of data is done performed with asymmetric algorithms Key exchange and data encryption are performed with asymmetric algorithms and digital signatures. Key exchange and digital signatures are performed with asymmetric algorithms
Expert Answer:
Answer rating: 100% (QA)
Answer C Key exchange and data encryption are performed with asymmetric algorithms and digital sig... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these programming questions
-
Which of the following is true with respect to fraud risk factors in an IT environment? a. Employees in an IT environment are highly skilled. b. Audit teams cannot evaluate the accounting information...
-
Which of the following is true about UNICAP rules? Only otherwise deductible expenses can qualify as a UNICAP expense UNICAP cost are always fully deductible in the current year only direct cost our...
-
Which of the following is true about all series ac circuits? (a) The voltage across any circuit element is a maximum when the current is a maximum in that circuit element. (b) The current at any...
-
A feature of most autumns in the northeastern United States is a period of mild, sunny weather called Indian summer, which occurs when an anticyclone happens to stall for a few days off the East...
-
How does a leveraged lease differ from an ordinary, long-term financial lease? List the key differences.
-
Finding 2 cv and setting the decision rule. Use = .05. (a) If df = 4, what is 2 cv ? (b) What is the decision rule?
-
What are the three steps that can be taken along a corporate eco-efficiency path? How are the five modules related to development of a measure of eco-efficiency?
-
Using the information for Sarot, Inc., in SE 4 and SE 5 compute the profit margin, asset turnover, return on assets, and return on equity for 2011 and 2012. In 2010, total assets were $400,000 and...
-
Question 2 (24 marks) Ben Mogashe has been tasked with preparing the cash budget for the forthcoming quarter. The accounting department has provided the following information to him for this purpose:...
-
Your client, Summerford, Inc., has a debt agreement with Valley City Bank that includes a number of restrictions and covenants. Violation of any restriction or covenant results in the entire amount...
-
Westland Manufacturing spends $ 2 0 , 0 0 0 to update the lighting in its factory to more energy - efficient LED fixtures. This will save the company $ 4 , 0 0 0 per year in electricity costs. What...
-
5. A lender wants to achieve a yield (YTM or IRR) of 7.25% on a 25-year amortization, monthly-payment loan with a 10-year term (i.e. maturity) with balloon. How many points must the lender charge...
-
Conduct a search on the companies Enron Corporation, Arthur Andersen, Merrill Lynch and WorldCom and develop an analysis that includes what corporate fraud consisted of for each of them. He explains...
-
Define - then compare and contrast - line-item budgeting, performance budgeting, program budgeting, and zero-base budgeting (ZBB). Present examples of each type of budget using a spreadsheet. What...
-
What information is sent between the card/smartphone and the card reader when it is placed in front of it? What is the maximum amount you can pay for something using a contactless card, or...
-
Simplify 3x (2x-3x+4) (3x-4)(2x+3) 3x(2x) (2x-1)(3x-3x+4)
-
BUSINESS LAW!! Mary and Bob Raine own a summer cabin in the Poconos Mountains. The Raine's contract with Julian, a local painter, to paint the cabin before the summer season. They agree on a price of...
-
Sportique Boutique reported the following financial data for 2012 and 2011. Instructions(a) Calculate the current ratio for Sportique Boutique for 2012 and 2011.(b) Suppose that at the end of 2012,...
-
If a node has a wireless connection to the Internet, does that node have to be mobile? Explain. Suppose that a user with a laptop walks around her house with her laptop, and always accesses the...
-
The word protocol is often used to describe diplomatic relations. Give an example of a diplomatic protocol.
-
In this problem we consider sending real-time voice from Host A to Host B over a packet-switched network (VoIP). Host A converts analog voice to a digital 64 kbps bit stream on the fly. Host A then...
-
A simplified vibration analysis of an airplane considers bounce and pitch motions (Fig. 6.24(a)). For this, a model consisting of a rigid bar (corresponding to the body of the airplane) supported on...
-
Derive the equations of motion, using Newton's second law of motion, for each of the systems shown in Figs. 6.21. Pulley, mass M, mass moment of inertia Jo 3r 3m T x(1) F(t) 2k 000 T x2(1) m T X3(1)...
-
Derive the equations of motion, using Newton's second law of motion, for each of the systems shown in Figs. 6.22. M, cos wt G 15 G3 13 ka 03 4 kn 12 G k3 16 G6 G Number of teeth on gear G, n, (i = 1...

Study smarter with the SolutionInn App


