Identify the traffic between your machine and the web machine: When did the interaction occur? ...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
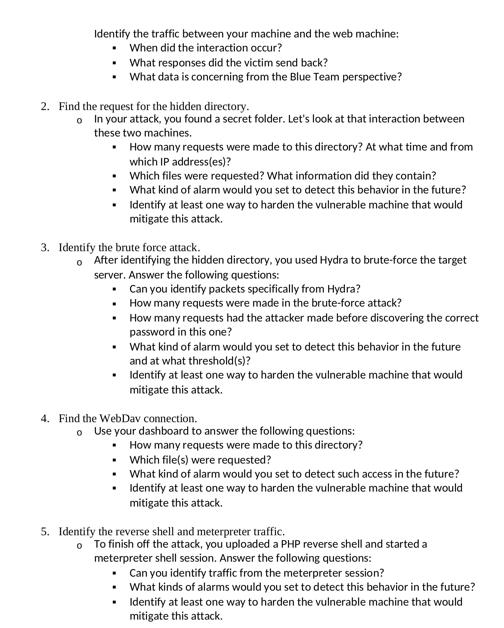
Identify the traffic between your machine and the web machine: When did the interaction occur? • What responses did the victim send back? What data is concerning from the Blue Team perspective? 2. Find the request for the hidden directory. o In your attack, you found a secret folder. Let's look at that interaction between these two machines. • How many requests were made to this directory? At what time and from which IP address(es)? Which files were requested? What information did they contain? • • • What kind of alarm would you set to detect this behavior in the future? Identify at least one way to harden the vulnerable machine that would mitigate this attack. 3. Identify the brute force attack. o After identifying the hidden directory, you used Hydra to brute-force the target server. Answer the following questions: . Can you identify packets specifically from Hydra? • How many requests were made in the brute-force attack? How many requests had the attacker made before discovering the correct password in this one? What kind of alarm would you set to detect this behavior in the future and at what threshold(s)? • Identify at least one way to harden the vulnerable machine that would mitigate this attack. 4. Find the WebDav connection. 0 Use your dashboard to answer the following questions: . How many requests were made to this directory? • Which file(s) were requested? • What kind of alarm would you set to detect such access in the future? Identify at least one way to harden the vulnerable machine that would mitigate this attack. 5. Identify the reverse shell and meterpreter traffic. o To finish off the attack, you uploaded a PHP reverse shell and started a meterpreter shell session. Answer the following questions: . Can you identify traffic from the meterpreter session? • What kinds of alarms would you set to detect this behavior in the future? Identify at least one way to harden the vulnerable machine that would mitigate this attack. • Identify the traffic between your machine and the web machine: When did the interaction occur? • What responses did the victim send back? What data is concerning from the Blue Team perspective? 2. Find the request for the hidden directory. o In your attack, you found a secret folder. Let's look at that interaction between these two machines. • How many requests were made to this directory? At what time and from which IP address(es)? Which files were requested? What information did they contain? • • • What kind of alarm would you set to detect this behavior in the future? Identify at least one way to harden the vulnerable machine that would mitigate this attack. 3. Identify the brute force attack. o After identifying the hidden directory, you used Hydra to brute-force the target server. Answer the following questions: . Can you identify packets specifically from Hydra? • How many requests were made in the brute-force attack? How many requests had the attacker made before discovering the correct password in this one? What kind of alarm would you set to detect this behavior in the future and at what threshold(s)? • Identify at least one way to harden the vulnerable machine that would mitigate this attack. 4. Find the WebDav connection. 0 Use your dashboard to answer the following questions: . How many requests were made to this directory? • Which file(s) were requested? • What kind of alarm would you set to detect such access in the future? Identify at least one way to harden the vulnerable machine that would mitigate this attack. 5. Identify the reverse shell and meterpreter traffic. o To finish off the attack, you uploaded a PHP reverse shell and started a meterpreter shell session. Answer the following questions: . Can you identify traffic from the meterpreter session? • What kinds of alarms would you set to detect this behavior in the future? Identify at least one way to harden the vulnerable machine that would mitigate this attack. •
Expert Answer:
Answer rating: 100% (QA)
Identify the traffic between your machine and the web machine Determine the time of interaction resp... View the full answer

Related Book For 

College Physics
ISBN: 978-0495113690
7th Edition
Authors: Raymond A. Serway, Jerry S. Faughn, Chris Vuille, Charles A. Bennett
Posted Date:
Students also viewed these accounting questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Case Study: Quick Fix Dental Practice Technology requirements Application must be built using Visual Studio 2019 or Visual Studio 2017, professional or enterprise. The community edition is not...
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
The two optional steps in the accounting cycle are preparing O a worksheet and post-closing trial balances. an adjusted trial balance and a post-closing trial balance. O a post-closing trial balance...
-
A piece of machinery of weight W is temporarily supported by cables AB, AC, and ADE. Cable ADE is attached to the ring at A, passes over the pulley at D and back through the ring, and is attached to...
-
Distinguish between a reissued and an updated audit report.
-
IHOP issued common stock and received \(\$ 32,000,000\). The par value of the IHOP stock was only \(\$ 32,000\). Is the excess amount of \(\$ 31,968,000\) a profit to IHOP? Does the excess affect net...
-
McDonnell Douglas Aircraft Corporation manufactures the C-17, the newest jet transport used by the U.S. Air Force. The company sells the C-17 for a flyaway cost of $175 million per jet. The variable...
-
A credit card company charges an effective rate of 19% for Joanne's credit card bill of $7500. Joanne decides to stop using her card and make the minimum payment of $175 at the beginning of each...
-
1. A friend has offered to play a gambling game with you that involves flipping a coin that be has provided. Since a flip of heads will be to his advantage, you want to test the coin for fairness...
-
A Python program that implements a graph using an adjacency matrix A Python a program that implements a graph using an adjacency list Vertex 0: -> 3 -> 2 -> 1 Vertex 1: > 2 -> 0 Vertex 2: -> 1-> 0...
-
Metlock, Inc. Inc. had a beginning inventory of 105 units of Product RST at a cost of $7 per unit. During the year, purchases were: Feb. 20 575 units at $8 Aug. 12 405 units at $10 May 5 480 units at...
-
How do adept communicators adeptly leverage etymology and semantic precision to imbue their business writing with layers of meaning and connotation, fostering deeper engagement and understanding...
-
Any Co is a medium-sized company that manufactures small plastic toys. You may have seen some of them the last time you bought a Happy Meal for a child. It has about 1,000 employees that have...
-
Anational catalog and the internet retailer has three warehouses and three major distribution centers located around the country. Normally, items are shipped directly from the warehouses to the...
-
How do adept writers adeptly navigate the delicate balance between formality and accessibility in their business correspondence, particularly when addressing stakeholders of varied educational...
-
Bruce invested $12,000 in a mutual fund 5 years ago. he received a dividend check for $1,000 after the first year. He received $750 after the second year. At the end of the 3rd year he received a...
-
For the following exercises, rewrite the sum as a product of two functions or the product as a sum of two functions. Give your answer in terms of sines and cosines. Then evaluate the final answer...
-
Refer to Figure. The charge lowered into the center of the hollow conductor has a magnitude of 5 C. Find the magnitude and sign of the charge on the inside and outside of the hollow conductor when...
-
If the current carried by a conductor is doubled, what happens to (a) The charge carrier density? (b) The electron drift velocity?
-
Two converging lenses, each of focal length 15.0 cm, are placed 40.0 cm apart, and an object is placed 30.0 cm in front of the first lens. Where is the final image formed, and what is the...
-
Derive Equation 3.9, \(x(t)=C e^{-\zeta \omega_{n} t} \cos \left(\omega_{d} t-\phi ight)\).
-
(a) The response of an oscillator with mass \(m=1\) kg is shown in Figure 3.51. What can you say about the properties of the oscillator and the response? Determine the equation of motion and the...
-
Solve Equation 3.6, \(\ddot{x}+2 \zeta \omega_{n} \dot{x}+\omega_{n}^{2} x=0\) for \(\zeta>1\).\

Study smarter with the SolutionInn App