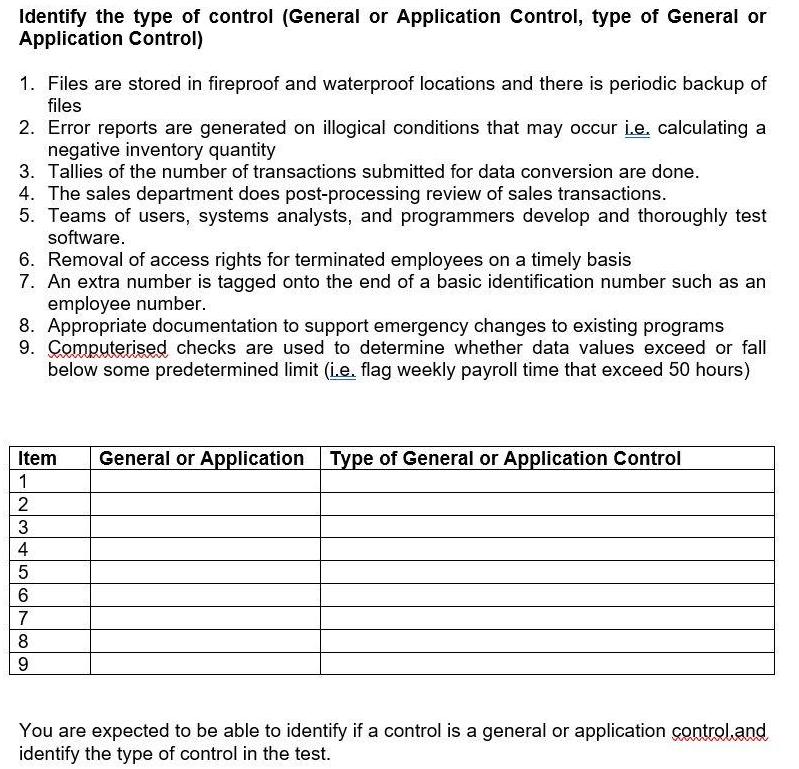
Identify the type of control (General or Application Control, type of General or Application Control) 1....
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Identify the type of control (General or Application Control, type of General or Application Control) 1. Files are stored in fireproof and waterproof locations and there is periodic backup of files 2. Error reports are generated on illogical conditions that may occur i.e. calculating a negative inventory quantity 3. Tallies of the number of transactions submitted for data conversion are done. 4. The sales department does post-processing review of sales transactions. 5. Teams of users, systems analysts, and programmers develop and thoroughly test software. 6. Removal of access rights for terminated employees on a timely basis 7. An extra number is tagged onto the end of a basic identification number such as an employee number. 8. Appropriate documentation to support emergency changes to existing programs 9. Computerised checks are used to determine whether data values exceed or fall below some predetermined limit (i.e. flag weekly payroll time that exceed 50 hours) Item 1 2 3 4 5 6 7 8 9 General or Application Type of General or Application Control You are expected to be able to identify if a control is a general or application control and identify the type of control in the test. Identify the type of control (General or Application Control, type of General or Application Control) 1. Files are stored in fireproof and waterproof locations and there is periodic backup of files 2. Error reports are generated on illogical conditions that may occur i.e. calculating a negative inventory quantity 3. Tallies of the number of transactions submitted for data conversion are done. 4. The sales department does post-processing review of sales transactions. 5. Teams of users, systems analysts, and programmers develop and thoroughly test software. 6. Removal of access rights for terminated employees on a timely basis 7. An extra number is tagged onto the end of a basic identification number such as an employee number. 8. Appropriate documentation to support emergency changes to existing programs 9. Computerised checks are used to determine whether data values exceed or fall below some predetermined limit (i.e. flag weekly payroll time that exceed 50 hours) Item 1 2 3 4 5 6 7 8 9 General or Application Type of General or Application Control You are expected to be able to identify if a control is a general or application control and identify the type of control in the test.
Expert Answer:
Answer rating: 100% (QA)
Question Step 1 1 General Control Data Security Control 2 Application Control Processing Contro... View the full answer

Related Book For 

Auditing and Assurance services an integrated approach
ISBN: 978-0132575959
14th Edition
Authors: Alvin a. arens, Randal j. elder, Mark s. Beasley
Posted Date:
Students also viewed these accounting questions
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
You're pretty sure that your candidate for class president has about 55% of the votes in the entire school. But you're worried that only 100 students will show up to vote. How often will the underdog...
-
The Results of inspection of DNA samples taken over the past 10 days are given below. Sample size is 100. (a) Construct a 3-sigma p-chart using this information. (b) If the number of defectives on...
-
Sumter Pumps Corporation, a manufacturer of industrial pumps, reports the following results for the year ended January 31, 2016: Retained earnings, February 1, 2015 . . . . . . . . . . . . . . . . ....
-
Check the name of a corporation that does business in California and determine where its principal place of business is located.
-
The following partial list of accounts and account balances has been taken from the trial balance and the adjusted trial balance of the Barker Company: Required Prepare the adjusting entry that...
-
As a TQM consultant for one of the companies what would be your advice / plane ? ( Discuss decline failure or success and give your advice )
-
2D crystal A3B (blue for A and yellow for B) is shown in the following figure. 1. Can you find 6-fold rotational symmetry? Can you find mirror symmetry? If yes, plot one rotation center/mirror line....
-
What are management's responsibility for internal control reporting? What does it have to do and what does it have to report in the 10K?Does the PCAOB generally think auditors have been doing a good...
-
Chrystal borrowed $1,000,000 from MQ Bank for one year at simple interest rate of 6.4% p.a. Unfortunately, she misread the documentation for the loan, and has misunderstood the interest charge. In...
-
What are the implications of technological advancements, such as social media and digital surveillance, on the identification and control of deviant behavior ?
-
The data shown were obtained from the financial records of Italian Exports, Inc., for March: Estimated Sales, $560,000, Sales 567,923, Purchases 294,823, Ending Inventory of next month's sales 10%,...
-
Provide ? differintial ? equation ? or ? the equation of motion ? of the ? below system with ? specific steps , , ? if you can make ? it ? more specific with free ? body ? diagram . . ? take ?...
-
According to Chavravety (2020), often, academically strong students lose confidence in their abilities and past achievements because of the pressure associated with doctoral education and...
-
1. _____ modifies MAC addresses in the ARP cache, so that network traffic goes from the victim's computer, through the attackers computer, and then to the destination computer. A. MAC cloning...
-
A summary of changes in Pen Corporation's Investment in Sam account from January 1, 2011, to December 31, 2013, follows (in thousands): ADDITIONAL INFORMATION 1. Pen acquired its 80 percent interest...
-
Distinguish between FOB destination and FOB origin. What procedures should the auditor follow concerning acquisitions of inventory on an FOB origin basis near year-end?
-
BestSellers.com sells fiction and nonfiction books to customers through the company's Web site. Customers place orders for books via the Web site by providing their name, address, credit card number,...
-
Explain how the rules concerning stock ownership apply to partners and professional staff. Give an example of when stock ownership would be prohibited for each.
-
A cylindrical tank of methanol has a mass of \(60 \mathrm{~kg}\) and a volume of \(75 \mathrm{~L}\). Determine the methanol's weight, density, and specific gravity. Take the gravitational...
-
A mass of \(0.5-\mathrm{kg}\) of argon is maintained at \(1400 \mathrm{kPa}\) and \(40^{\circ} \mathrm{C}\) in a tank. What is the volume of the tank?
-
The air in an automobile tire with a volume of \(0.015 \mathrm{~m}^{3}\) is at \(30^{\circ} \mathrm{C}\) and \(140 \mathrm{kPa}\) (gage). Determine the amount of air that must be added to raise the...

Study smarter with the SolutionInn App