In an access network, the token bucket algorithm is used for access control. In every time...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
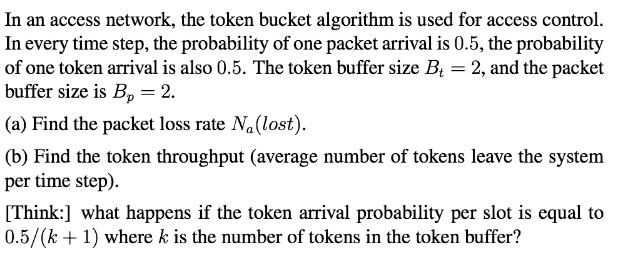
In an access network, the token bucket algorithm is used for access control. In every time step, the probability of one packet arrival is 0.5, the probability of one token arrival is also 0.5. The token buffer size B = 2, and the packet buffer size is B, = 2. (a) Find the packet loss rate N.(lost). (b) Find the token throughput (average number of tokens leave the system per time step). [Think:] what happens if the token arrival probability per slot is equal to 0.5/(k + 1) where k is the number of tokens in the token buffer? In an access network, the token bucket algorithm is used for access control. In every time step, the probability of one packet arrival is 0.5, the probability of one token arrival is also 0.5. The token buffer size B = 2, and the packet buffer size is B, = 2. (a) Find the packet loss rate N.(lost). (b) Find the token throughput (average number of tokens leave the system per time step). [Think:] what happens if the token arrival probability per slot is equal to 0.5/(k + 1) where k is the number of tokens in the token buffer?
Expert Answer:
Answer rating: 100% (QA)
a As we know in token bucket algorithm the token has been disc... View the full answer

Related Book For 

Posted Date:
Students also viewed these mathematics questions
-
To understand how the token bucket algorithm can give credit to the sender that does not use its rate allocation for a while but wants to use it later, lets repeat the previous problem with r = 3 and...
-
Q. Describe how organizations define CSR (their main activities) and how it resonates with a firm. Also, describe the importance of CSR aims for small businesses and why targets are important for CSR...
-
A 0.5-kg block B slides without friction inside a slot cut in arm OA which rotates in a vertical plane at a constant rate, = 2 rad/s. At the instant when =30?, r = 0.6 m and the force exerted on...
-
Suppose a product can be produced using virgin ore at a marginal cost given by MC 1 = 0. 5q 1 and with recycled materials at a marginal cost given by MC 2 = 5 + 0. 1q 2 . (a) If the inverse demand...
-
In recent years, technological improvements have greatly reduced the costs of producing music CDs, and a number of new firms have entered the music CD industry. At the same time, prices of...
-
When 0.075 g of penicillamine is dissolved in 10.0 mL of pyridine and placed in a sample cell 10.0 cm in length, the observed rotation at 20C (using the D line of sodium) is -0.47. Calculate the...
-
Extreme Machine manufactures machines and parts for various industries; they have an office in Youngstown, Ohio. Avery Dennison manufactures and sells labels from a plant in Mentor, Ohio. They use...
-
Spencer Company manufactures and sells three products. Relevant per unit data concerning each product are given below. Instructions (a) Compute the contribution margin per unit of the limited...
-
There are four types of relational models: communal sharing, authority ranking, equality matching, and market pricing. Which relational models do you use in your interpersonal interactions? Is one...
-
The shaded area in the following graph represents the feasible region of a linear programming problem whose objective function is to be maximized. Label each of the following statements as True or...
-
"Find the volume of those points at the end of vectors starting at the origin that are no more than an angle of /6 from the vector v=(1,1,1) and inside a radius of = 4." I do not know how to set up...
-
Explain the difference between the category of business process control and application control covered in this chapter and the business process controls and application controls to be covered in...
-
When would an interaction term be incorporated into a model? Explain its intended purpose. Provide an example of a regression model that would use an interaction term. Give an interpretation of the...
-
What restrictions apply to the dividends- received deduction of dividends received from debt-financed stock purchases?
-
An electronics company is interested in forecasting the quarterly sales for next year for one of its products. Based on the past sales data, they found that the quarterly sales have seasonality and...
-
Indo Corporation was organized on January 4 2018, and began active business on January 5 , 2018. Indo incurred the following expenses in connection with creating its business. What is the maximum...
-
1) Sells $110,163 of services to clients for cash. Describe the effects of this transaction on the accounting equation in terms of debits and credits 0 1 12 13 14 Assets Liabilities Prepare the...
-
Orange juice producers are dismayed and puzzled. An economist told them that the reason the demand for orange juice fell is that a new technology allow tomato producers to pick ripe tomatoes more...
-
Assuming even parity, find the parity bit for each of the following data units. a. 1001011 b. 0001100 c. 1000000 d. 1110111
-
If Alice and Bob need to communicate using asymmetric-key cryptography, how many keys do they need? Who needs to create these keys?
-
Answer the following questions about the digital hierarchy in Figure 6.23: a. What is the overhead (number of extra bits) in the DS-1 service? b. What is the overhead (number of extra bits) in the...
-
Paul Simard was delighted when Ancol Ltd. offered him the job of manager at its Jonquiere, Quebec plant. Simard was happy enough managing a small metal stamping plant with another company, but the...
-
In 1979, Larry Merritt and his wife Bobbie bought The Cake Box, a small business located in a tiny 42-square metre store in Tulsa, Oklahoma. The couple were the only employees. "I would make cakes...
-
For Gilles LaCroix, there is nothing quite as beautiful as a handcrafted wood-framed window. LaCroix's passion for windows goes back to his youth in St. Jean, Quebec, where he was taught how to make...

Study smarter with the SolutionInn App


