In most of these, the method should accept the required pieces of data as arguments and...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
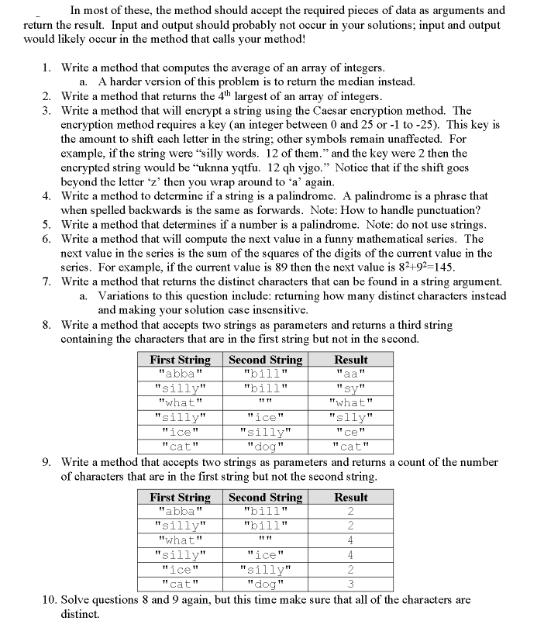
In most of these, the method should accept the required pieces of data as arguments and return the result. Input and output should probably not occur in your solutions; input and output would likely occur in the method that calls your method! 1. Write a method that computes the average of an array of integers. a. A harder version of this problem is to return the median instead. 2. Write a method that returns the 4th largest of an array of integers. 3. Write a method that will encrypt a string using the Caesar encryption method. The encryption method requires a key (an integer between 0 and 25 or -1 to-25). This key is the amount to shift each letter in the string; other symbols remain unaffected. For example, if the string were "silly words. 12 of them." and the key were 2 then the encrypted string would be "uknna yqtfu. 12 qh vigo." Notice that if the shift goes beyond the letter 'z' then you wrap around to "a" again. 4. Write a method to determine if a string is a palindrome. A palindrome is a phrase that when spelled backwards is the same as forwards. Note: How to handle punctuation? Write a method that determines if a number is a palindrome. Note: do not use strings. Write a method that will compute the next value in a funny mathematical series. The next value in the series is the sum of the squares of the digits of the current value in the series. For example, if the current value is 89 then the next value is 8²+92-145. 5. 6. 7. Write a method that returns the distinct characters that can be found in a string argument. a. Variations to this question include: returning how many distinct characters instead and making your solution case insensitive. 8. Write a method that accepts two strings as parameters and returns a third string containing the characters that are in the first string but not in the second. First String Second String " "abba "silly" "what" "silly" "ice" "silly" "ice "cat" "dog" 9. Write a method that accepts two strings as parameters and returns a count of the number of characters that are in the first string but not the second string. First String Second String "bill" "abba" "silly" "bill" FFF "what" "silly" "ice "cat" 11 "bill" "bill" *** "ice" "silly" "dog Result waa 11 11 -11 "what" "slly" ce" cat" Result 2 2 4 4 2 10. Solve questions 8 and 9 again, but this time make sure that all of the characters are distinct. In most of these, the method should accept the required pieces of data as arguments and return the result. Input and output should probably not occur in your solutions; input and output would likely occur in the method that calls your method! 1. Write a method that computes the average of an array of integers. a. A harder version of this problem is to return the median instead. 2. Write a method that returns the 4th largest of an array of integers. 3. Write a method that will encrypt a string using the Caesar encryption method. The encryption method requires a key (an integer between 0 and 25 or -1 to-25). This key is the amount to shift each letter in the string; other symbols remain unaffected. For example, if the string were "silly words. 12 of them." and the key were 2 then the encrypted string would be "uknna yqtfu. 12 qh vigo." Notice that if the shift goes beyond the letter 'z' then you wrap around to "a" again. 4. Write a method to determine if a string is a palindrome. A palindrome is a phrase that when spelled backwards is the same as forwards. Note: How to handle punctuation? Write a method that determines if a number is a palindrome. Note: do not use strings. Write a method that will compute the next value in a funny mathematical series. The next value in the series is the sum of the squares of the digits of the current value in the series. For example, if the current value is 89 then the next value is 8²+92-145. 5. 6. 7. Write a method that returns the distinct characters that can be found in a string argument. a. Variations to this question include: returning how many distinct characters instead and making your solution case insensitive. 8. Write a method that accepts two strings as parameters and returns a third string containing the characters that are in the first string but not in the second. First String Second String " "abba "silly" "what" "silly" "ice" "silly" "ice "cat" "dog" 9. Write a method that accepts two strings as parameters and returns a count of the number of characters that are in the first string but not the second string. First String Second String "bill" "abba" "silly" "bill" FFF "what" "silly" "ice "cat" 11 "bill" "bill" *** "ice" "silly" "dog Result waa 11 11 -11 "what" "slly" ce" cat" Result 2 2 4 4 2 10. Solve questions 8 and 9 again, but this time make sure that all of the characters are distinct.
Expert Answer:

Related Book For 

Principles of Auditing and Other Assurance Services
ISBN: 978-0078025617
19th edition
Authors: Ray Whittington, Kurt Pany
Posted Date:
Students also viewed these programming questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
If y=tan-13/t^2 find dy/dt
-
An object is dropped from a height of 80 feet. t1 = 1, t2 = 2? (a) Use the position equation s 16t2 + v0t + s0 to write a function that represents the situation, (b) Use a graphing utility to graph...
-
This spreadsheet assignment is a continuation of the spreadsheet assignments given in earlier chapters. If you completed those spreadsheets, you have a head start on this one. If needed, review the...
-
A proton (inertia \(1.67 \times 10^{-27} \mathrm{~kg}\) ) and an electron (inertia \(9.11 \times 10^{-31} \mathrm{~kg}\) ) are being separately subjected to an electric force of \(3.2 \times 10^{-14}...
-
MagTech assembles tape players from four major components arranged as follows: The components can be purchased from three different vendors, who have supplied the following reliability data: a. If...
-
10. A plastic ball is rising in water with terminal speed v. If we use a different plastic whose density is double that of the original ball but still less that density of water, keeping the radius...
-
1. What should BoB have done to avoid this situation? 2. Should the sales support staff ask the IT department to rewrite the user manual as a maintenance project, or should they request more training...
-
Trafford Co is a manufacturer of engine parts, supplying parts to the major car manufacturers. The company's year-end is 31 July 2022. You are an audit supervisor in Mourinho & Co and are currently...
-
Pierre works at Winners and as an employee he is given the ability to buy a suit for $100 when regular customers would pay $500 for the same suit. Winners cost for the suit is $150. Does Pierre have...
-
The following equations represent the demand and supply for silver pendants. QD = 70 - 2P QS -10+2P Find market equilibrium quantity. Please omit any units in your answer
-
Let f(x) be given by the function f(x) = a = 0. (ax - b if x 2 15-2ax - (2- x) if x < 2 a. Write an expression for b if f is continuous at x = 2. b. If fis continuous at x = 2, explain why b cannot...
-
For this fourth Discussion Board, please recall that inputs will be based on the Cases assigned in the Syllabus thus far. If you worked them as a case study, making a summary and comments, your...
-
The following are partial balance sheets for the Bank of Canada and the 14 LVTS Participants: BANK OF CANADA Assets($Bs): Securities SPRA Advances to LVTS Participants. Liabilities ($Bs): 1200 LVTS...
-
Suppose the returns on an asset are normally distributed. The historical average annual return for the asset was 6.5 percent and the standard deviation was 8.5 percent. a. What is the probability...
-
With your classmates, form small teams of skunkworks. Your task is to identify an innovation that you think would benefit your school, college, or university, and to outline an action plan for...
-
In response to threats from a terrorist organization, Technology International installed protective measures consisting of chainlink fences, concrete road barriers, electronic gates, and underground...
-
Distinguish between the system review and the engagement review types of peer reviews.
-
The firm of Wilson and Wiener (WW), CPAs, has had requests from a number of clients and prospective clients to perform various types of services. Please reply as to whether the appropriate...
-
Suppose a bond is taxable for both federal and state purposes. Let Rb = the BTROR on the bond, tfed = the federal tax rate, and tst = the state tax rate. Determine the ATROR (i.e., after federal and...
-
Under what conditions are the Exempt Model and Pension Model equivalent? Under what conditions would one model perform better than the other? How does the \($6,500\) limitation on deductible and Roth...
-
Consider three taxpayers who are in the following tax brackets: Alice 25% Brad 35% Camille 40%

Study smarter with the SolutionInn App